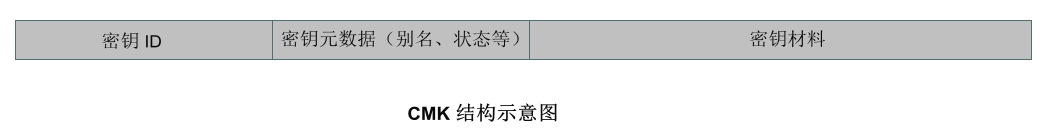
用户主密钥(CMK,Customer Master Key)是 KMS 服务的基本元素,它包含密钥 ID、密钥元数据(别名、描述、状态等)和用于加解密数据的密钥材料。
默认情况下,通过 KMS 服务创建 CMK 密钥时,由 KMS 服务底层加密机生成安全的密钥材料。当您希望使用自己的密钥材料时,也就是希望实施 BYOK(Bring Your Own Key)方案时,可通过 KMS 服务生成一个密钥材料为空的 CMK,并将自己的密钥材料导入到该用户主密钥中,形成一个外部密钥 CMK(EXTERNAL CMK),再由 KMS 服务进行该外部密钥的分发管理。
功能特点
在腾讯云上实施 BYOK(Bring Your Own Key)方案,即允许您在腾讯云架构上使用您自有的密钥材料进行敏感数据加解密服务。
完全掌控并管理您在腾讯云上使用的密钥服务,包括按需导入或删除密钥材料。
您可以在本地密钥管理基础设施中备份一份密钥材料,作为腾讯云密钥管理系统的额外灾备措施。
通过支持在云上使用您自有的密钥材料进行加解密操作,满足相关行业合规要求。
注意事项
需要确保导入密钥材料的安全性:
在使用密钥导入功能时,您需要确保自己生成密钥材料的随机源的安全可靠性。目前 KMS 国密版本仅允许导入128位对称密钥,FIPS 版本仅允许导入256位对称密钥。
需要确保导入密钥材料的可用性:
KMS 服务提供自身服务的高可用及备份恢复能力,但导入的密钥材料的可用性需由用户来管理。强烈建议您采用安全可靠的方式保存密钥材料的原始备份,以便在意外删除密钥材料或密钥材料过期时,能及时将备份的密钥材料重新导入KMS服务。
需注意密钥导入操作的规范性:
当您将密钥材料导入CMK 时,该 CMK 与该密钥材料永久关联,即不能将其他密钥材料导入该外部密钥 CMK 中。当使用该外部密钥 CMK 加密数据时,加密后的数据必须使用加密时采用的 CMK(即 CMK 的元数据及密钥材料与导入的密钥匹配)才能解密数据,否则解密将失败。请谨慎处理密钥材料、CMK 的删除操作。
需要注意密钥导入的状态:
待导入状态的密钥属于启用状态的密钥,该启用状态密钥需付费使用。