创建子账号(用户)
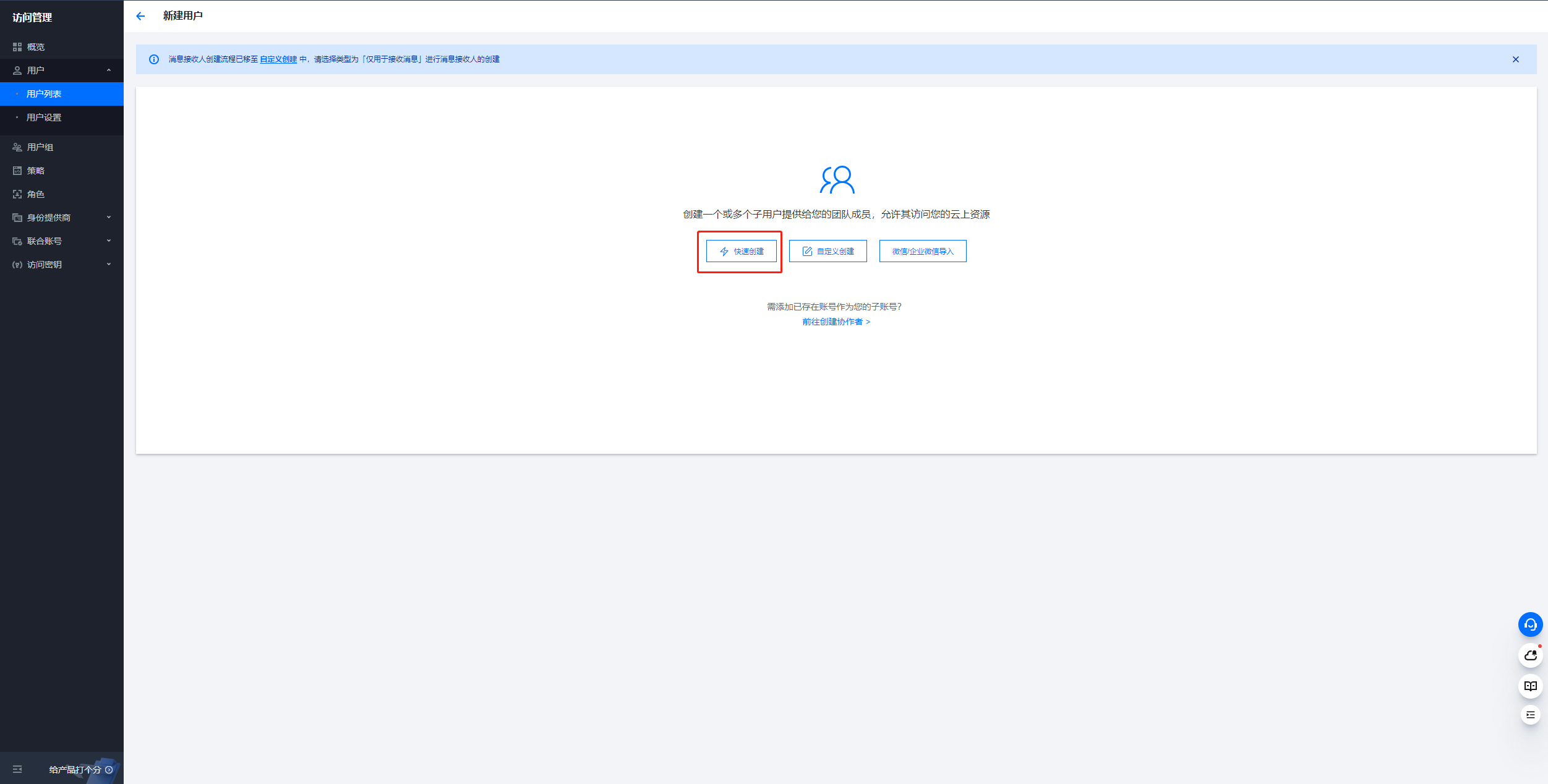
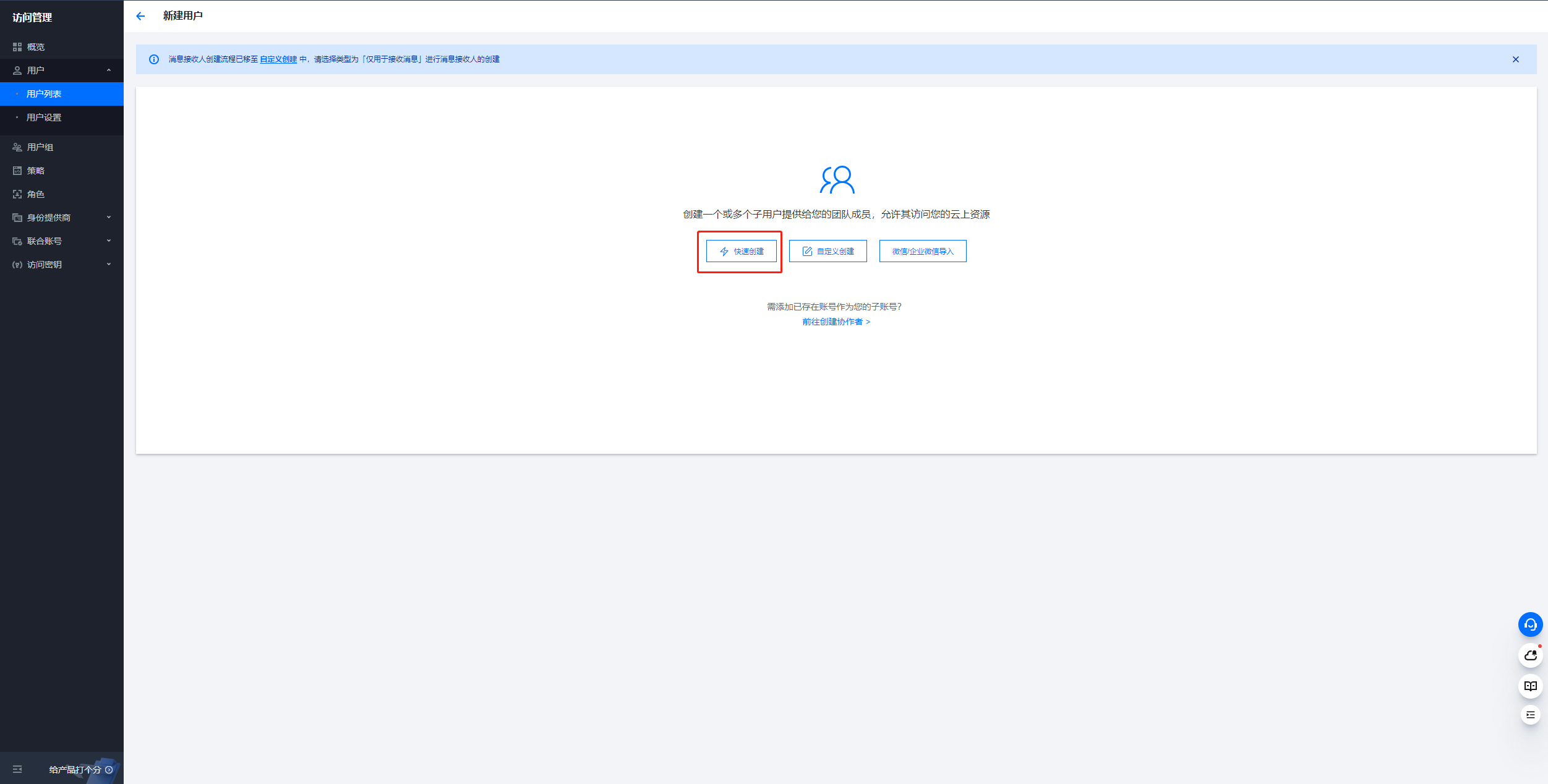
第一步:新建用户
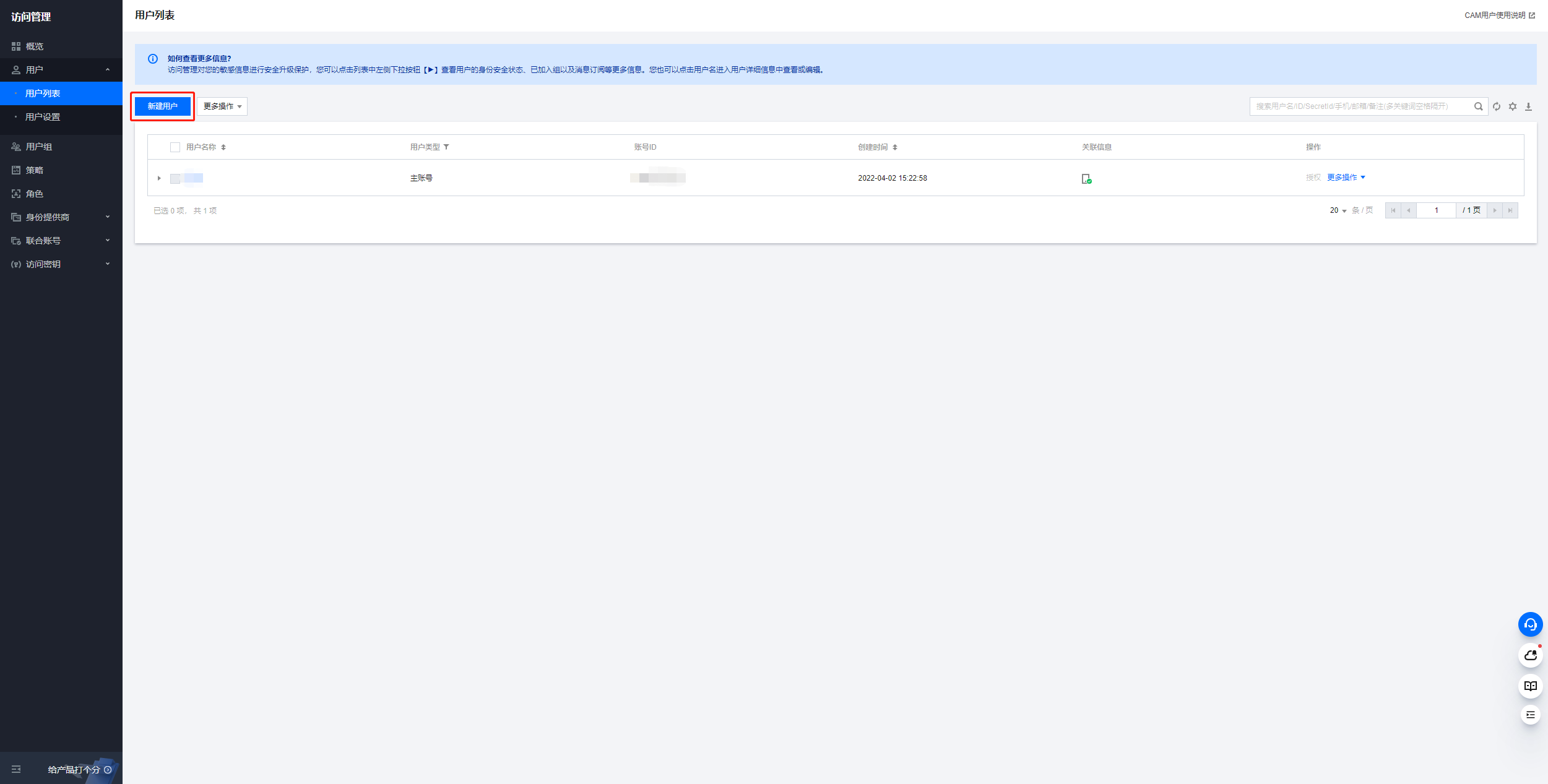
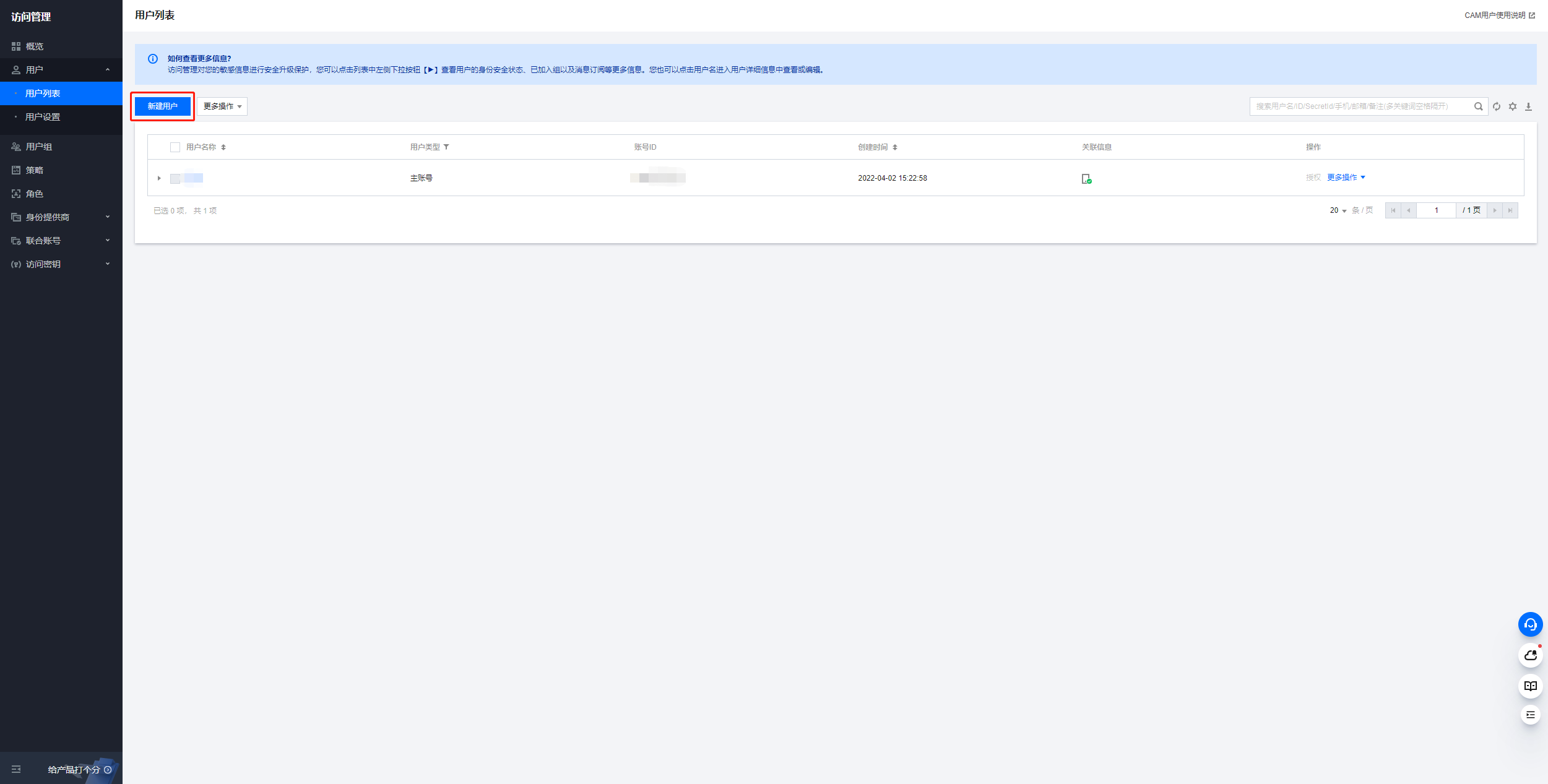
选择快速创建
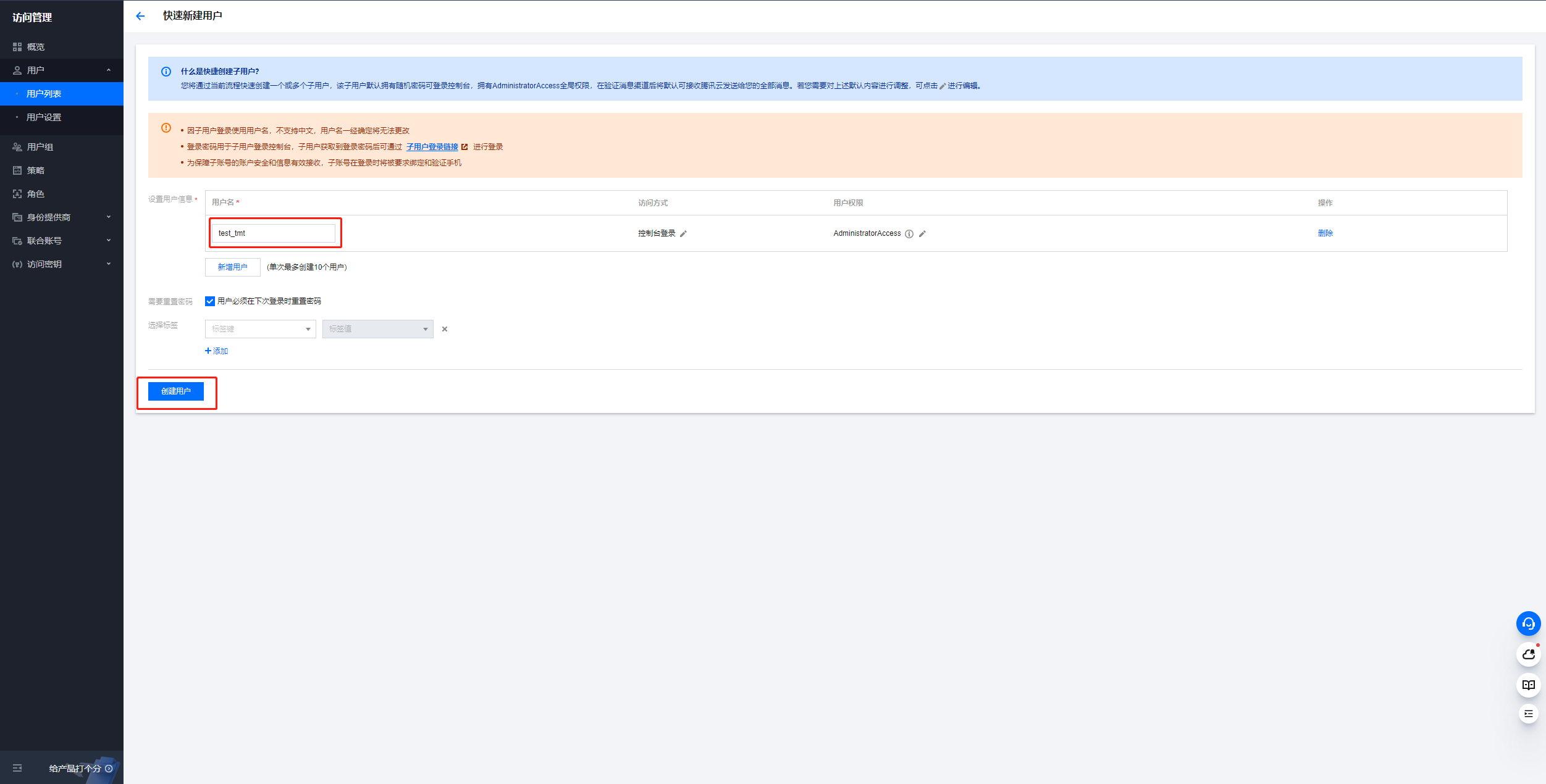
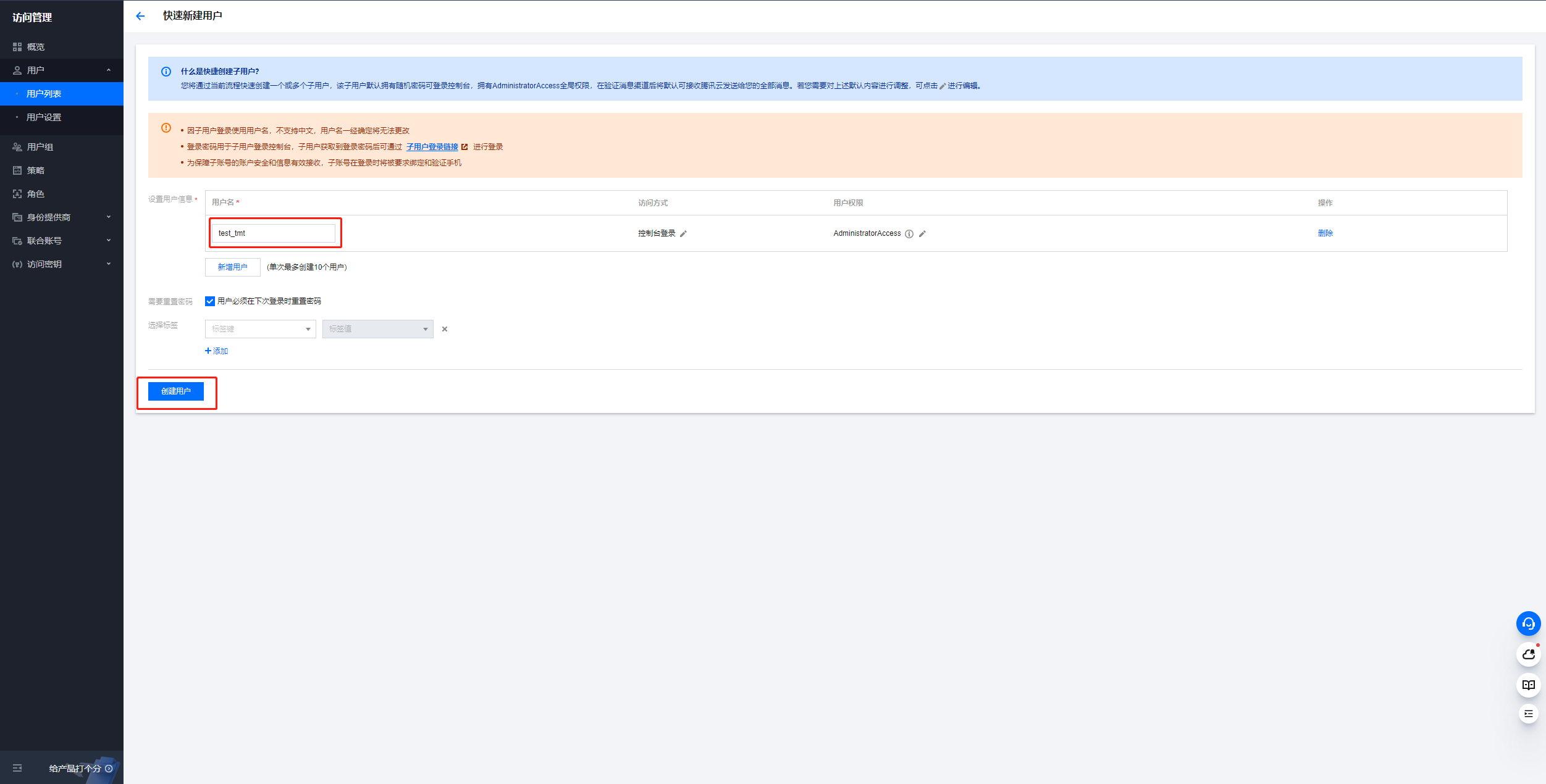
第二步: 填写创建信息
填写用户名,单击创建用户完成创建。
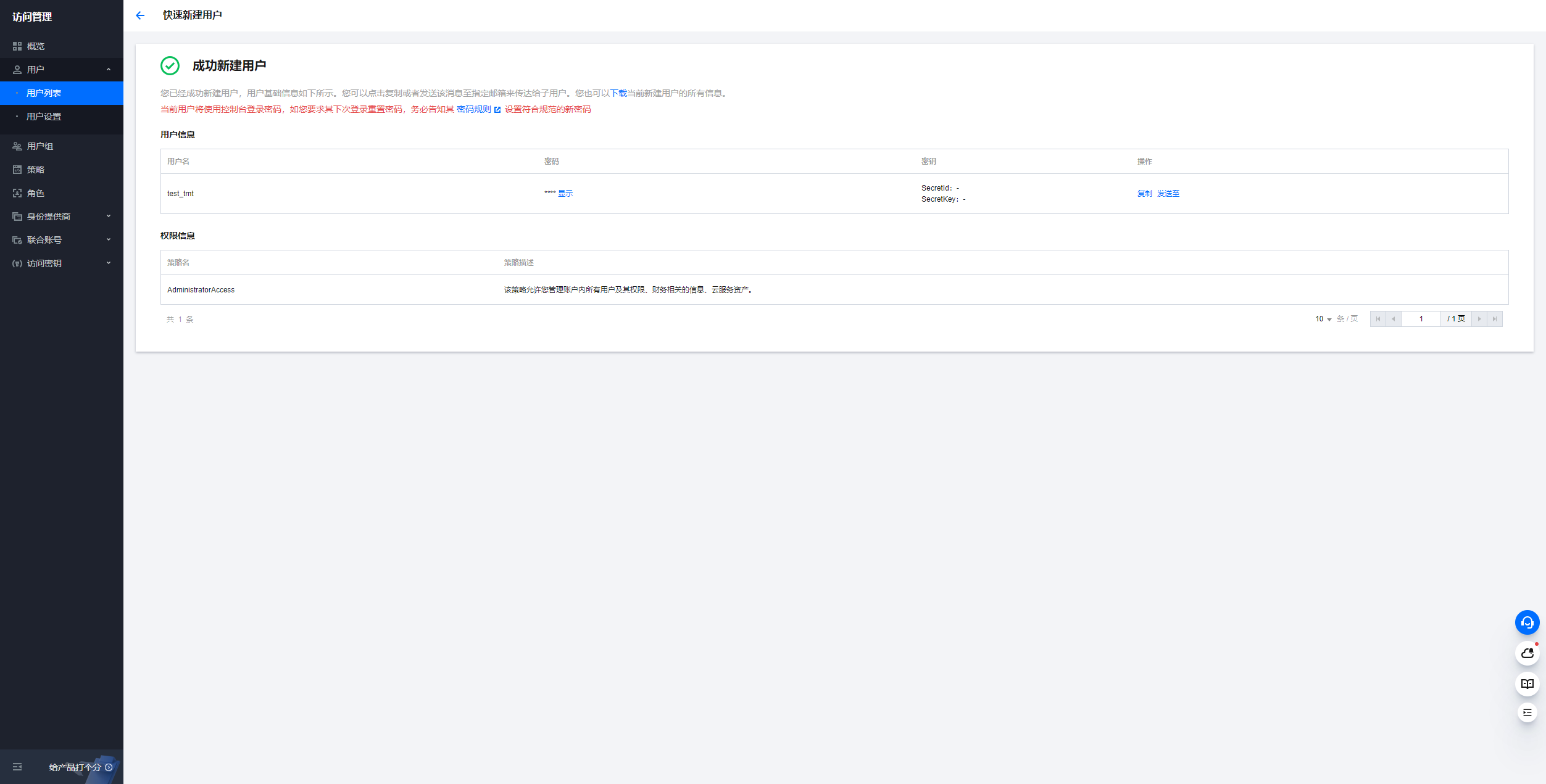
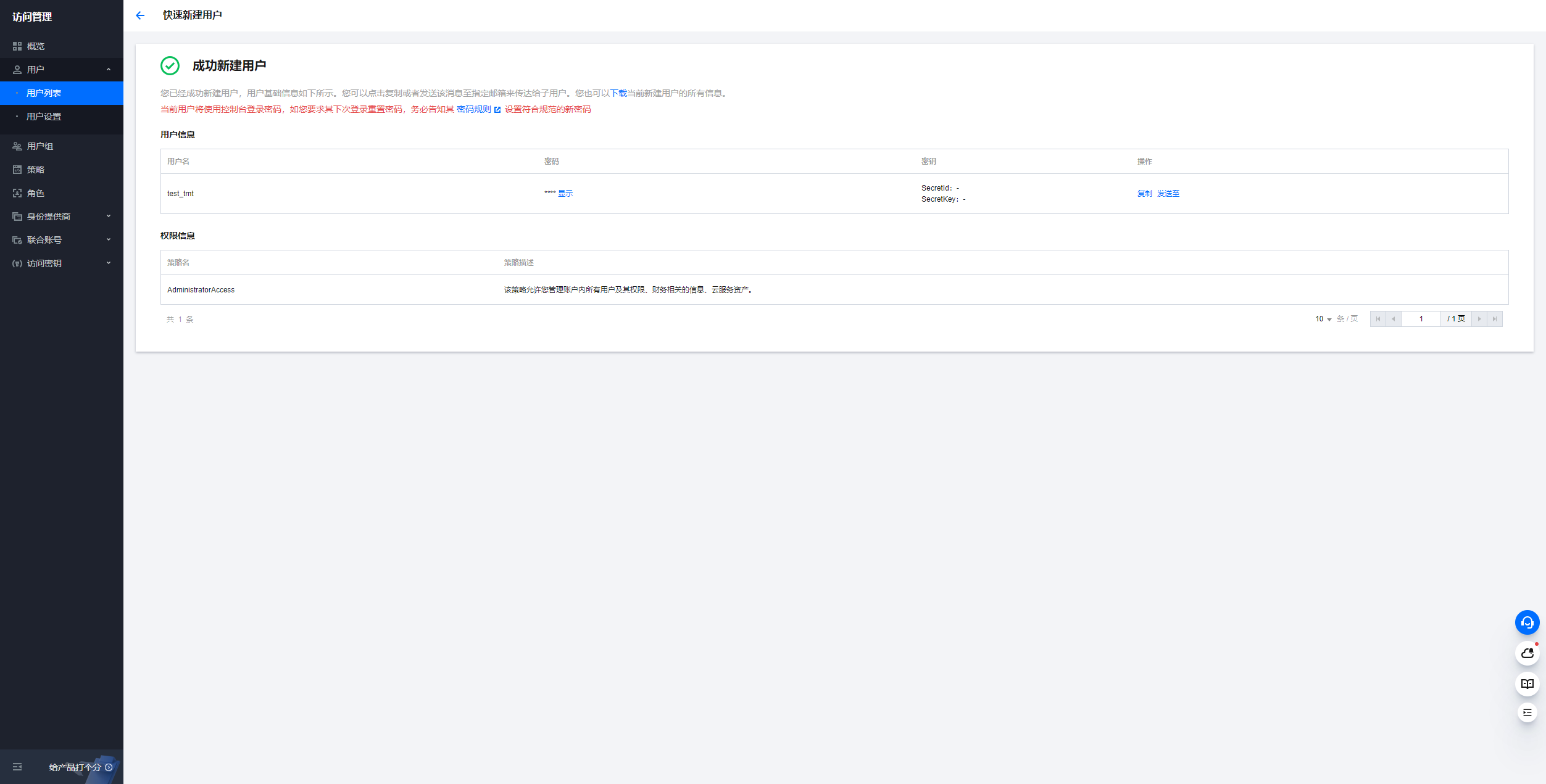
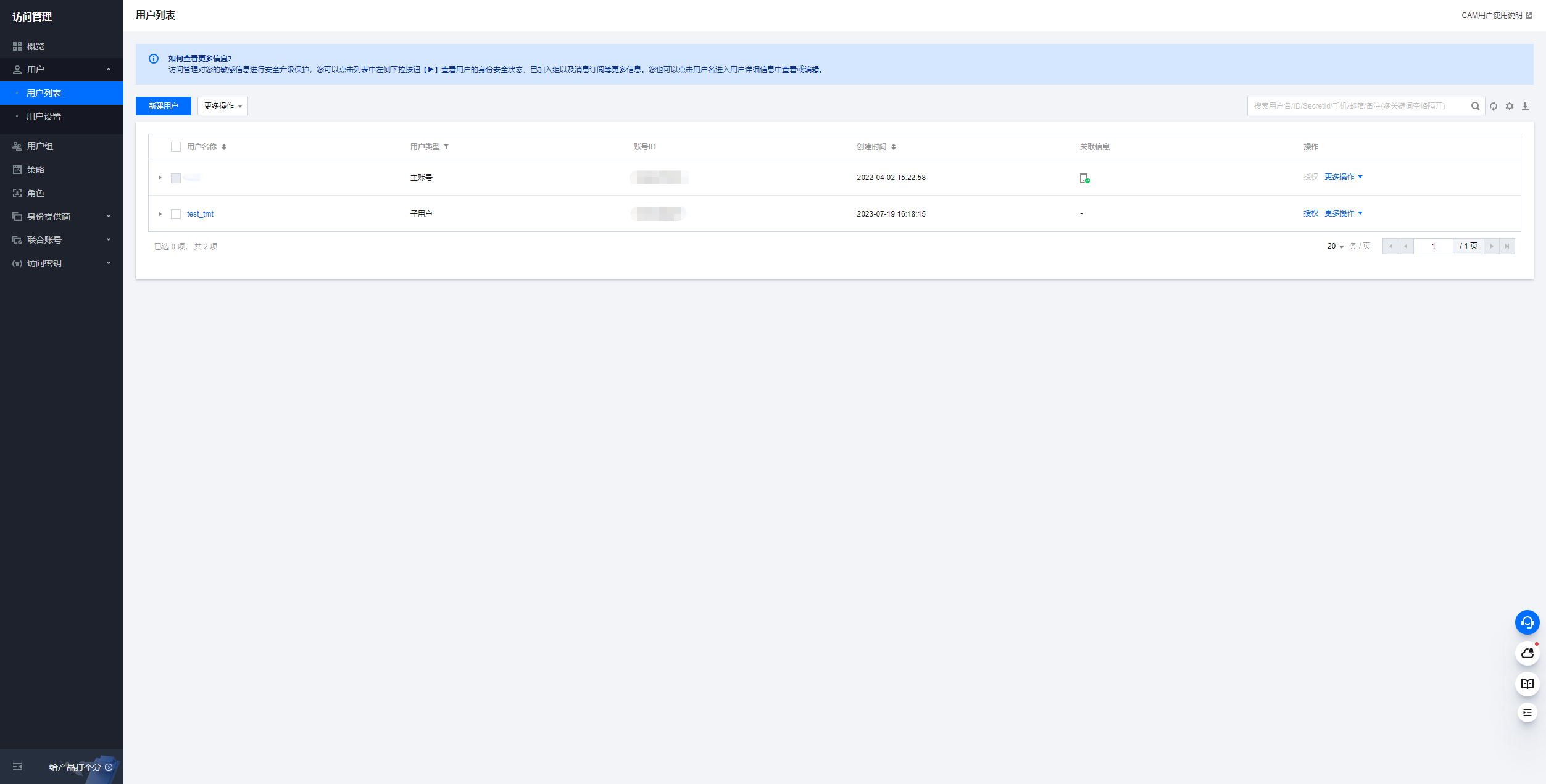
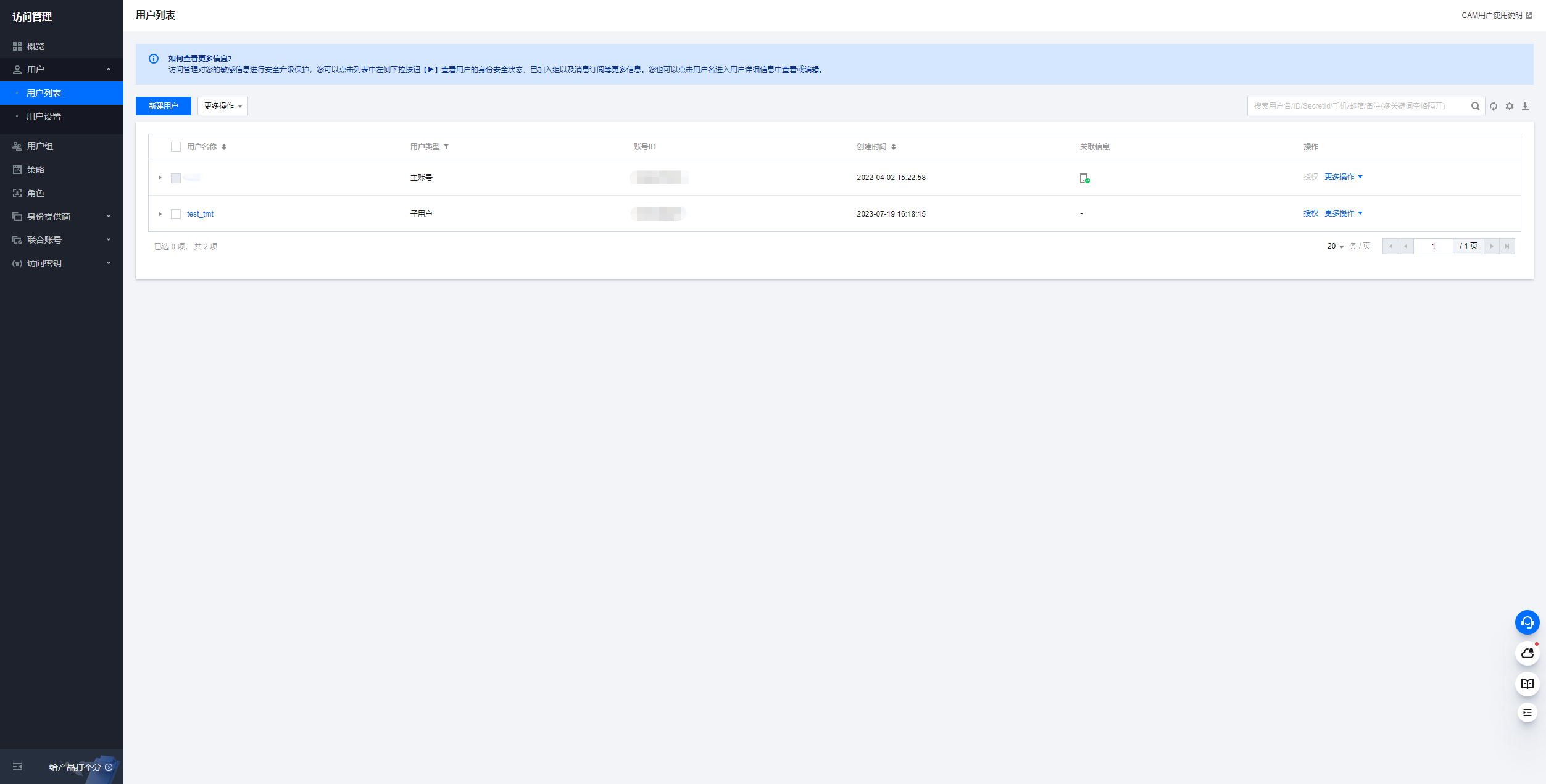
第三步:查看创建的用户
创建 JSON 策略
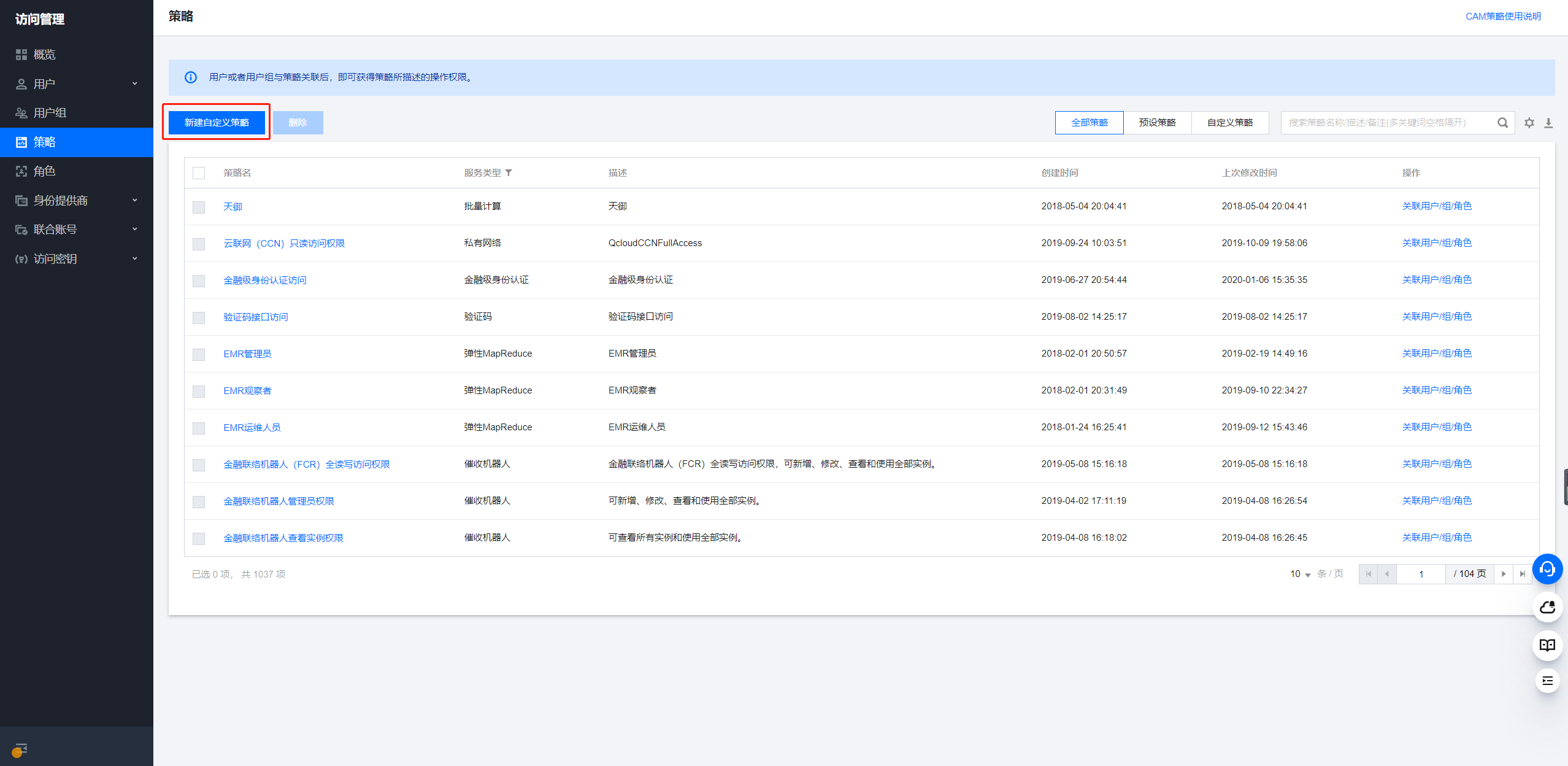
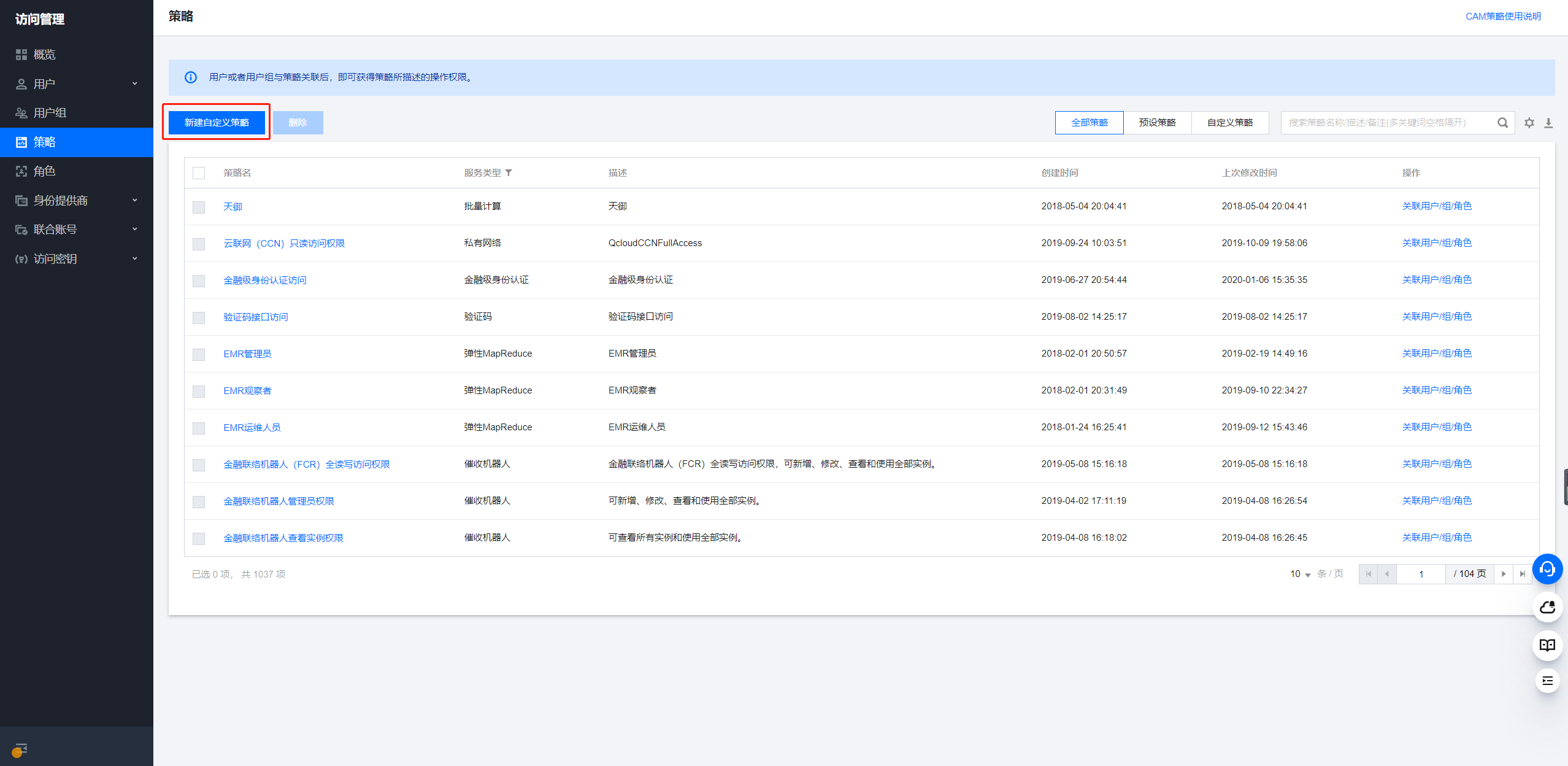
第一步:新建自定义策略
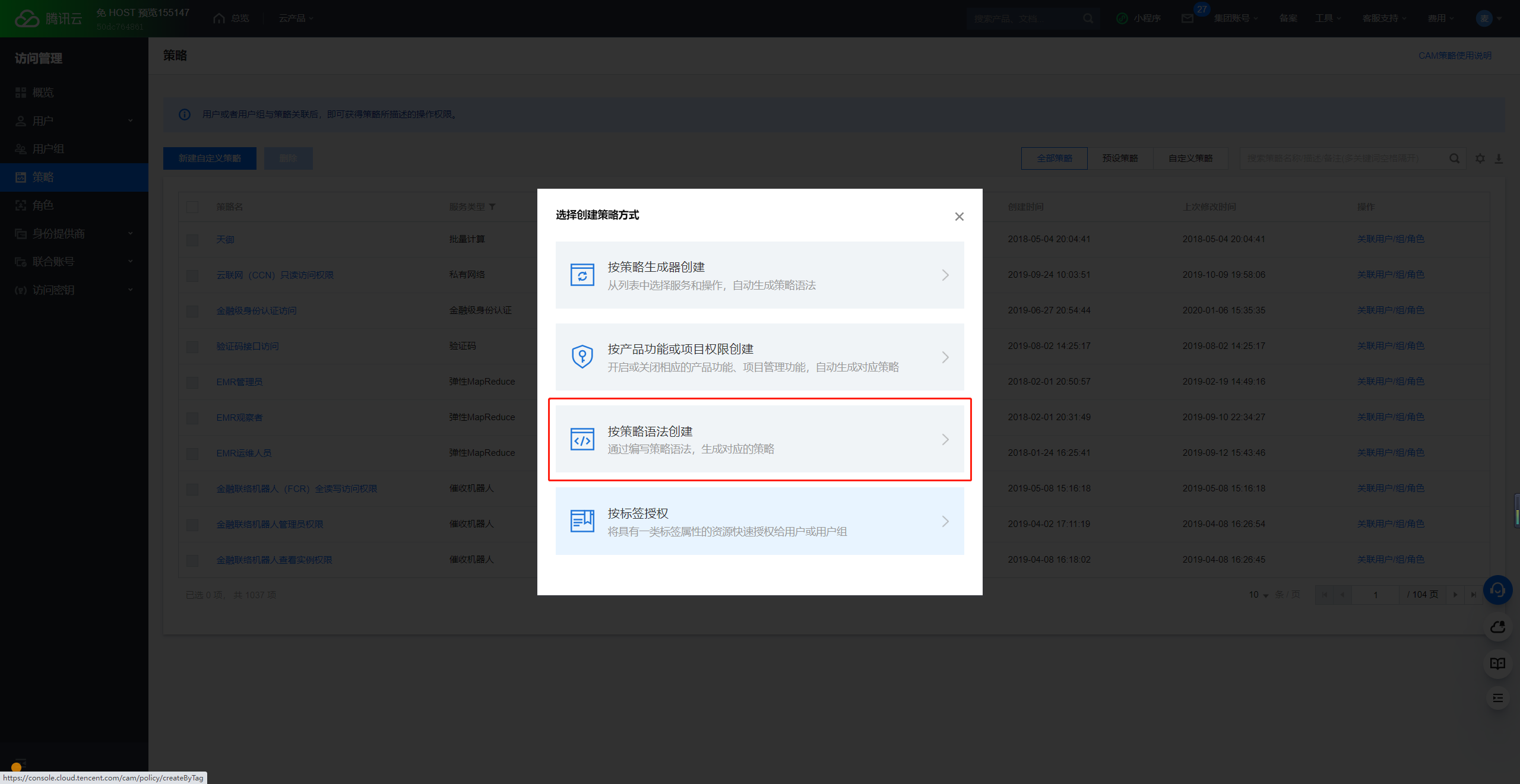
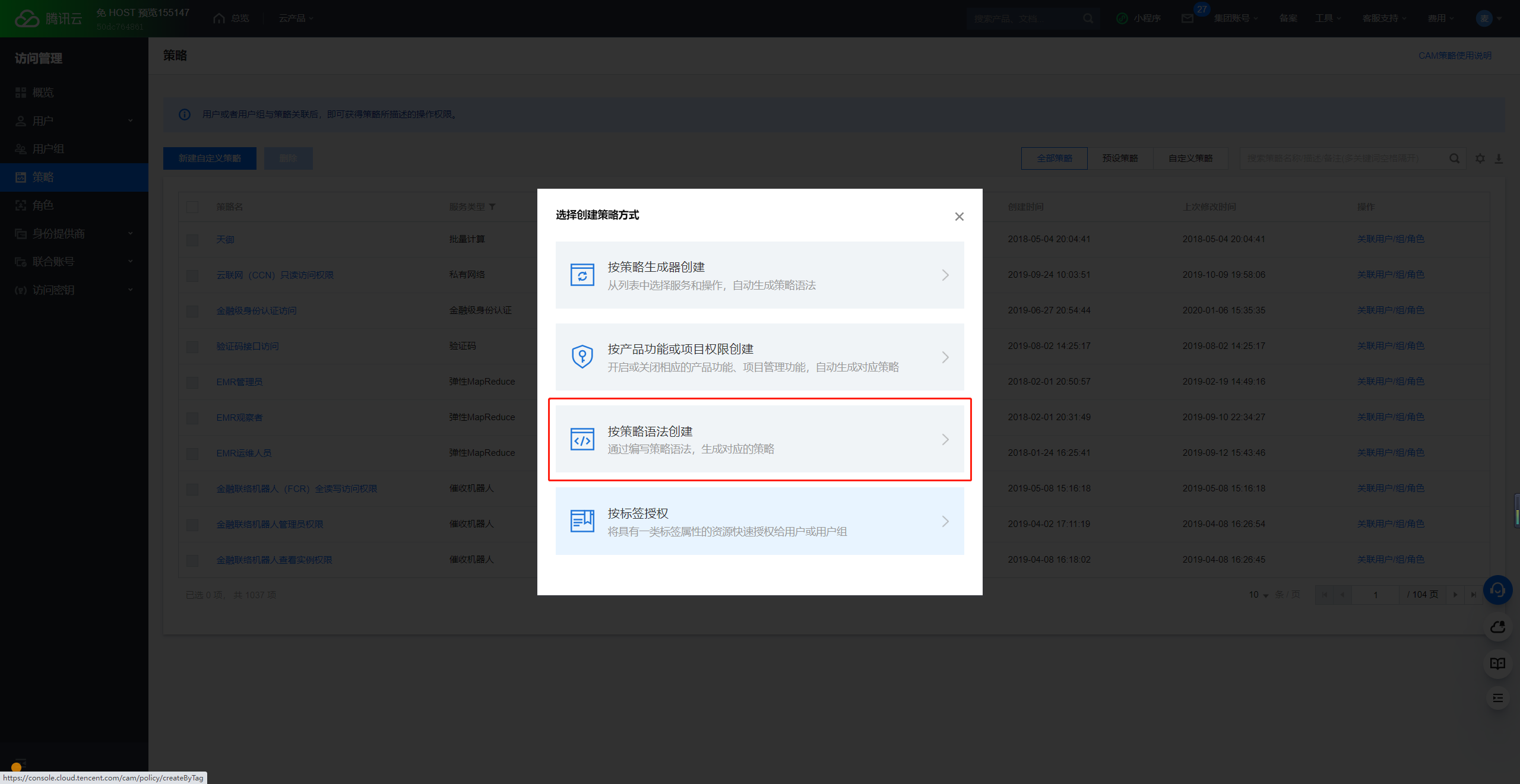
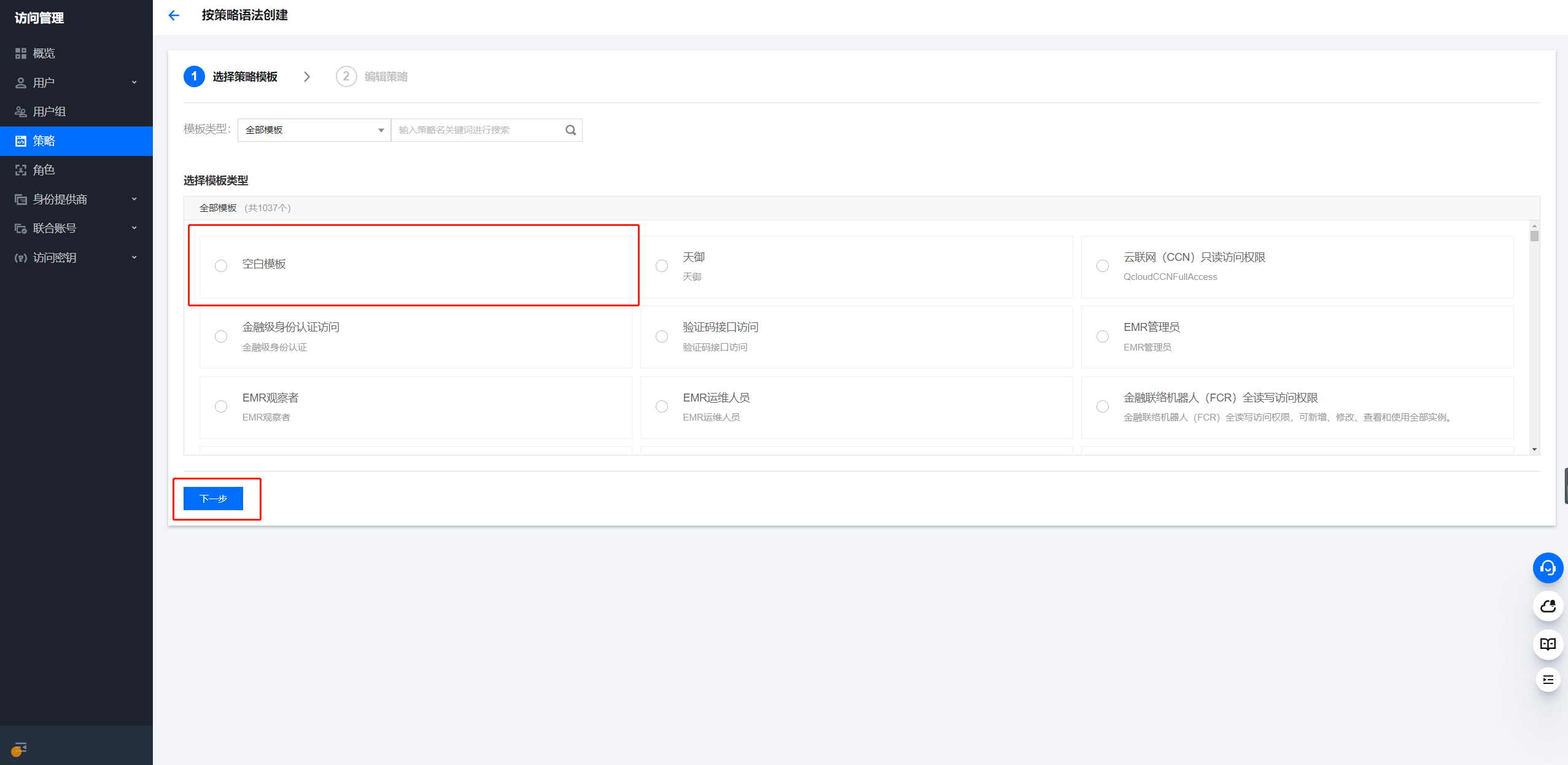
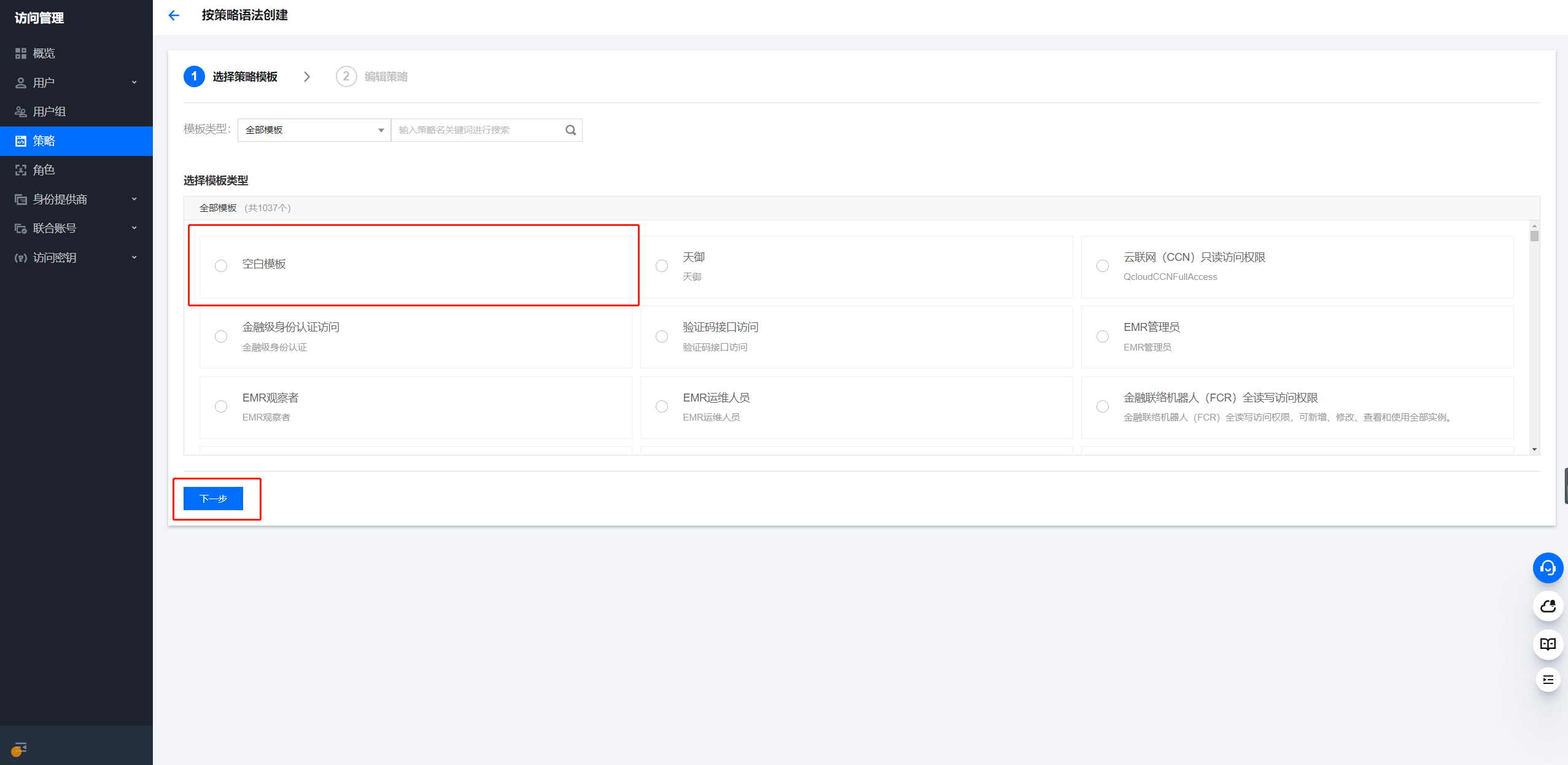
第二步:选择策略类型
选择按策略语法创建
第三步:选择模板类型
选择空白模板 > 单击下一步
第四步:填写策略信息并保存
填写策略名称、填写描述,将需要的 预设 JSON 策略 复制粘贴至策略内容,单击完成创建策略。
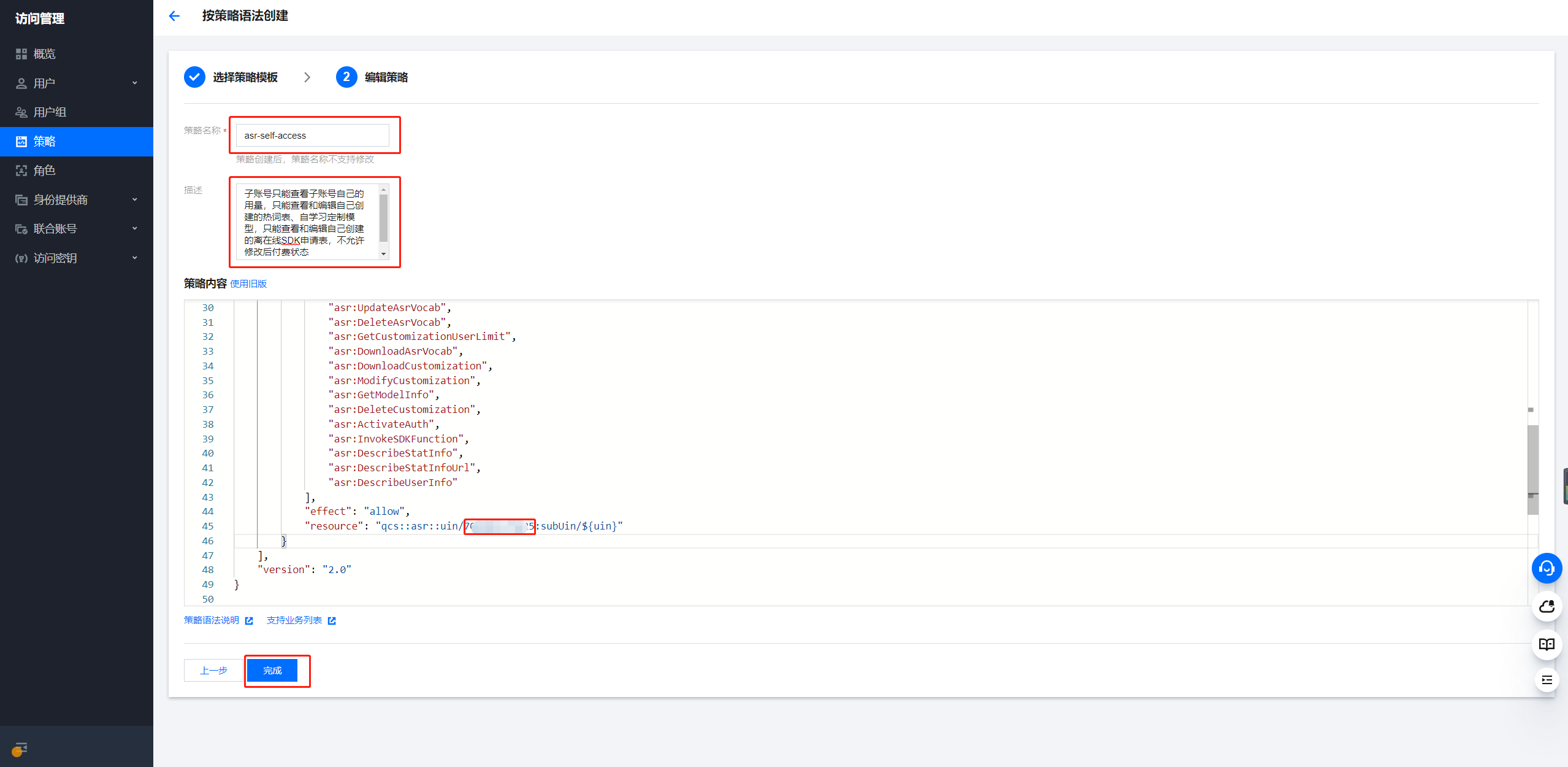
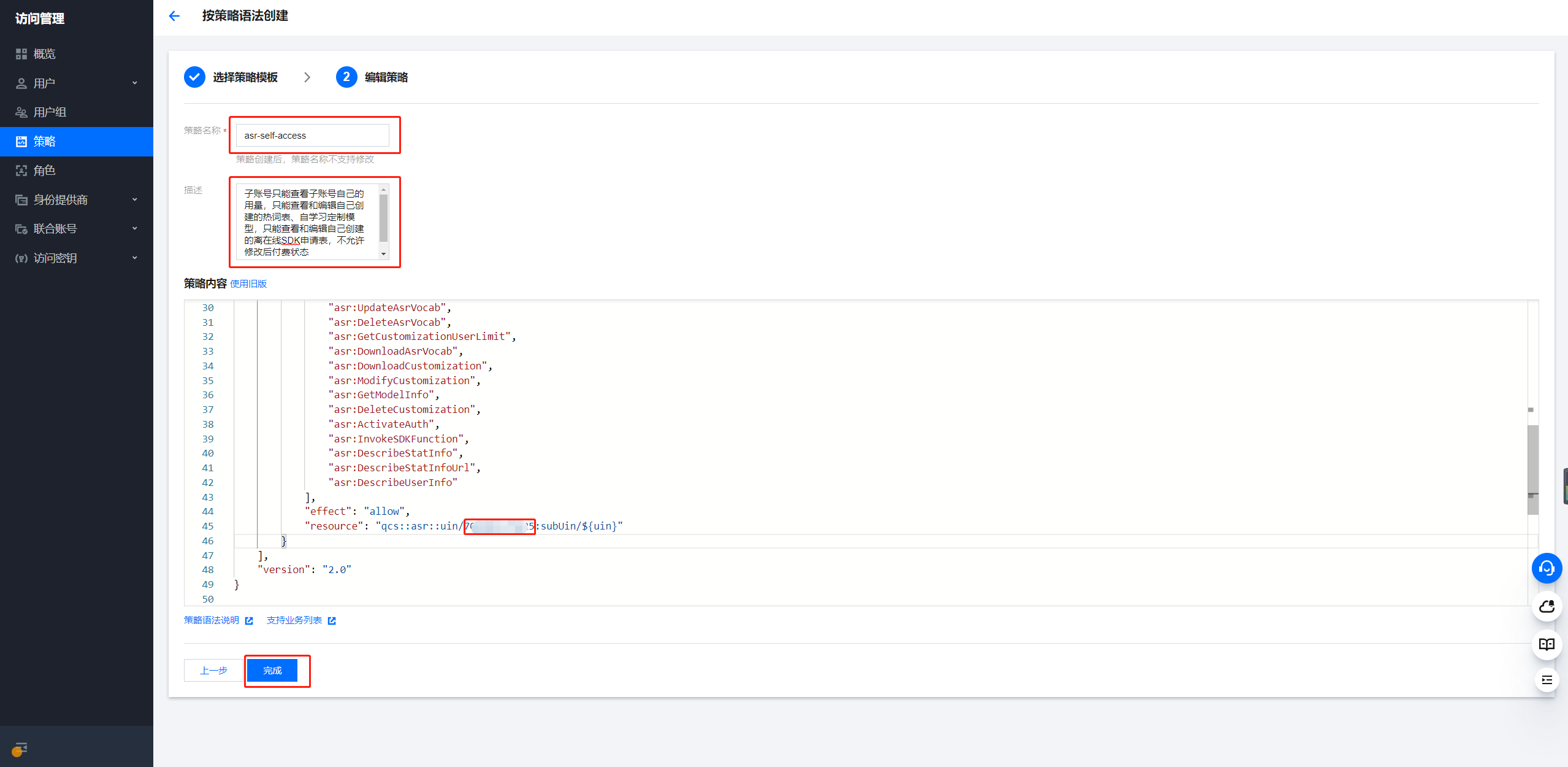
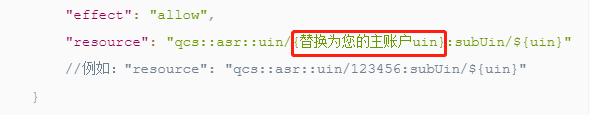
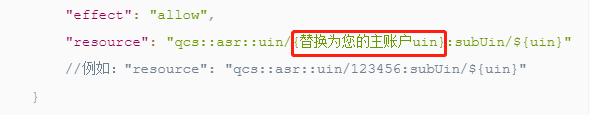
策略内容(注意:resource中的条件需要替换成主账号的uin,如下图)
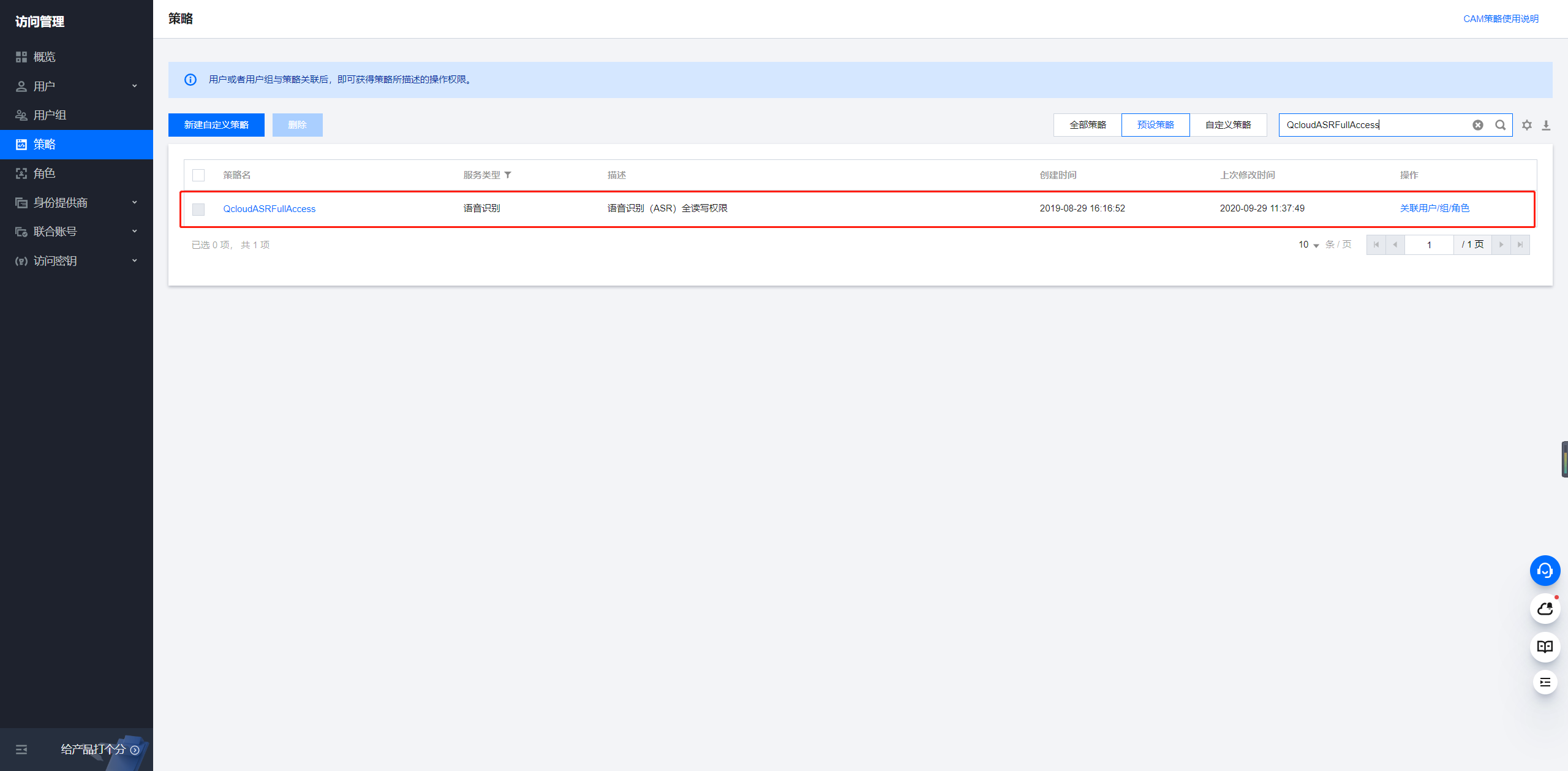
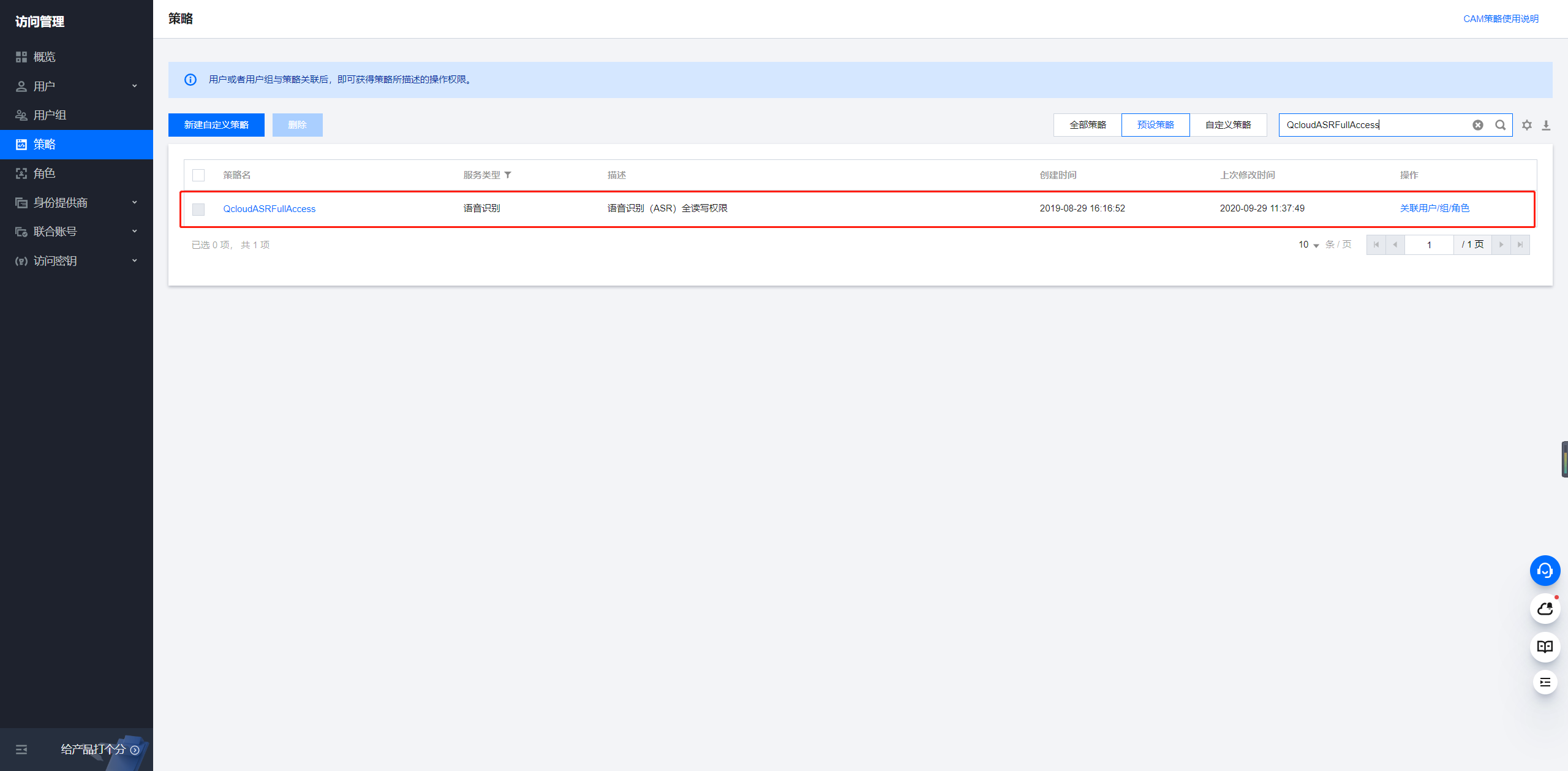
关联或授予策略
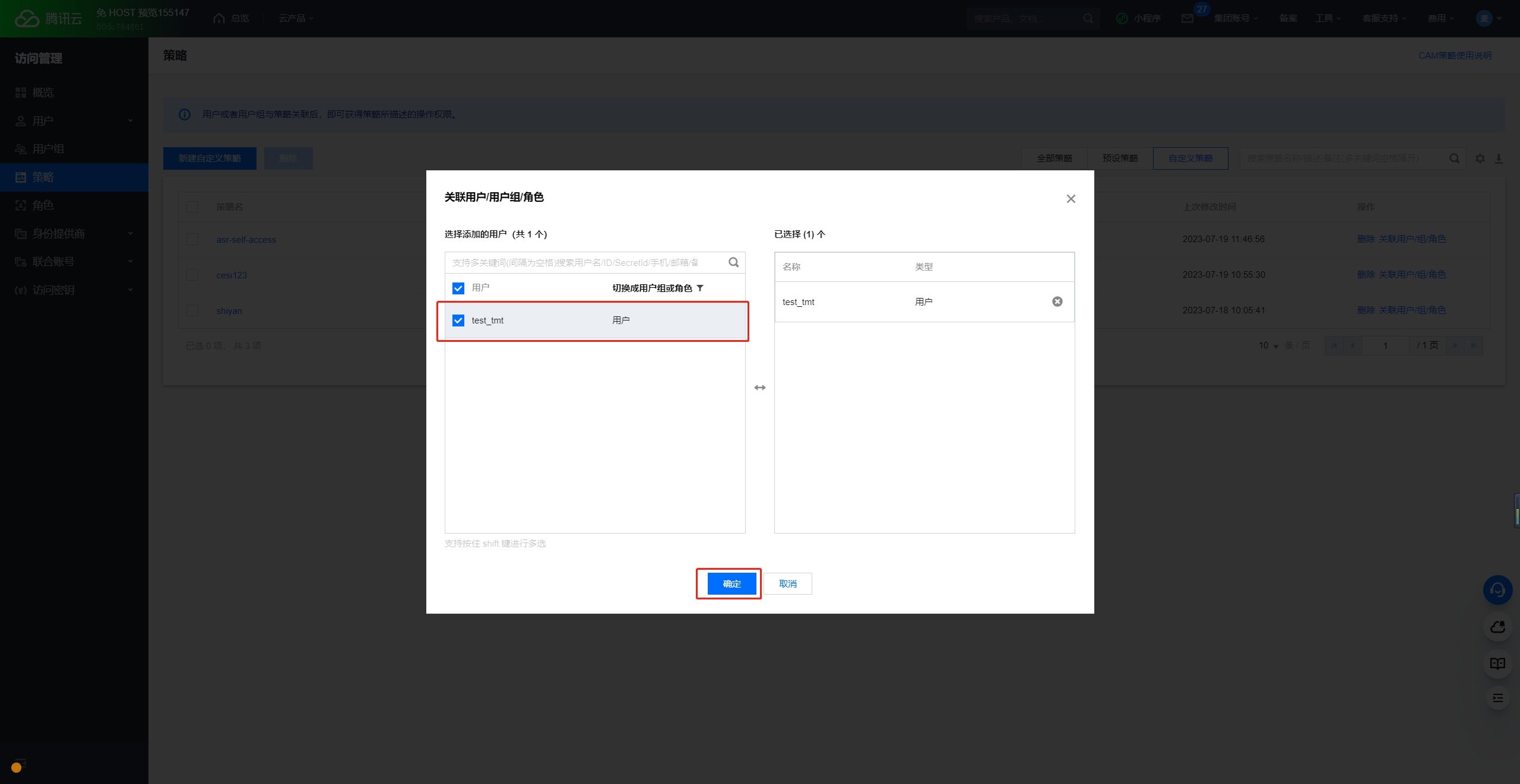
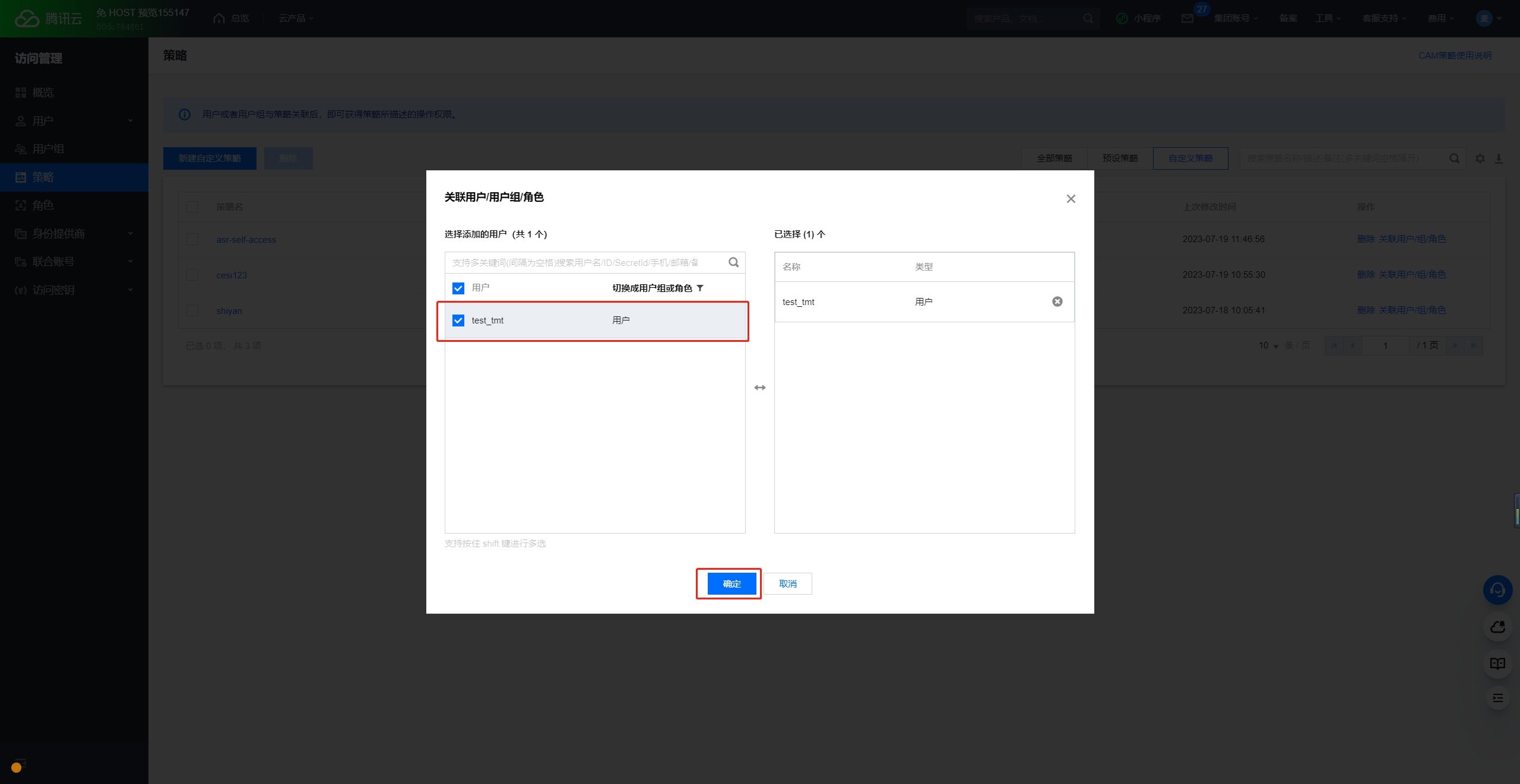
方式一:在策略列表关联相关用户
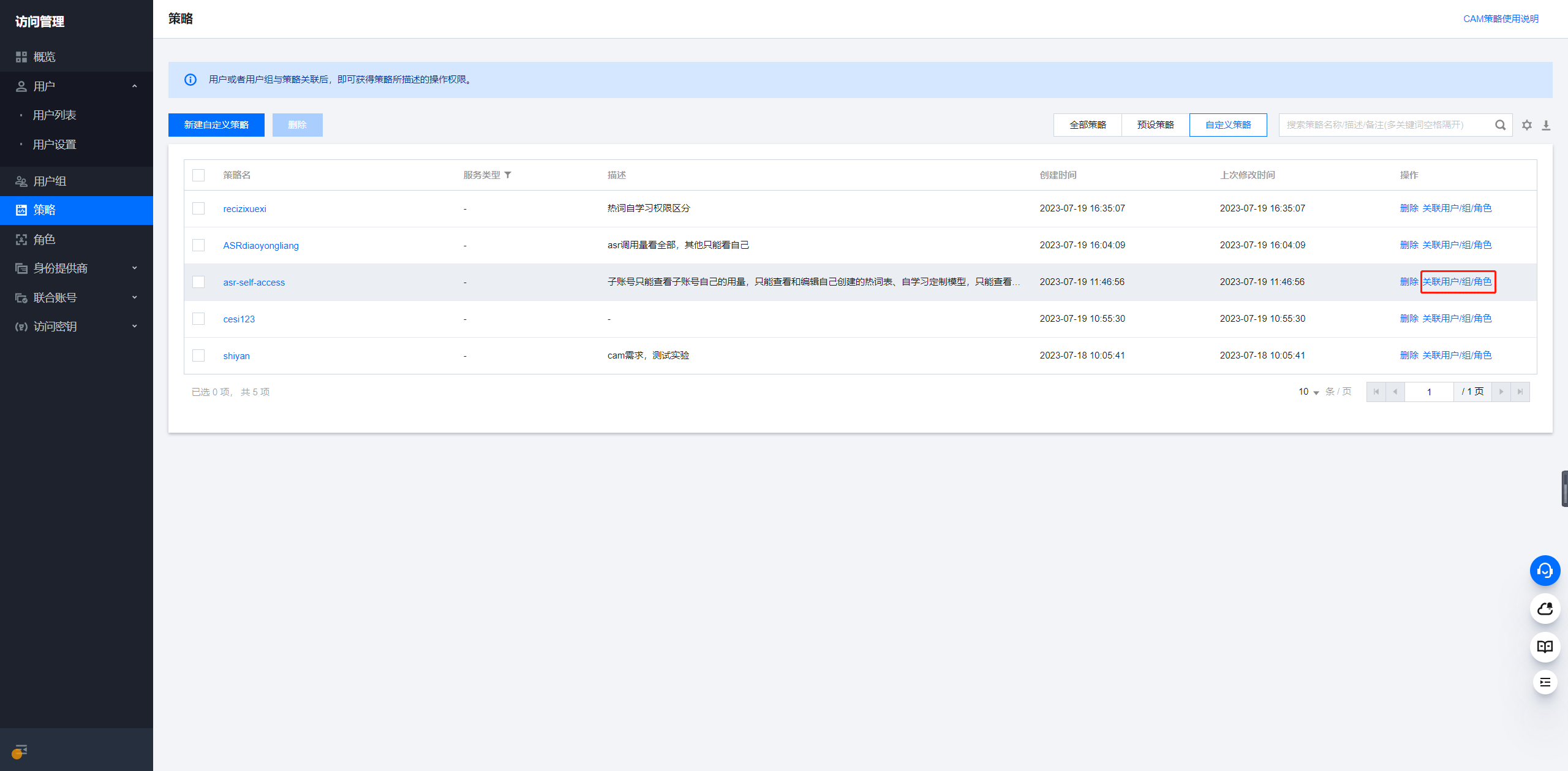
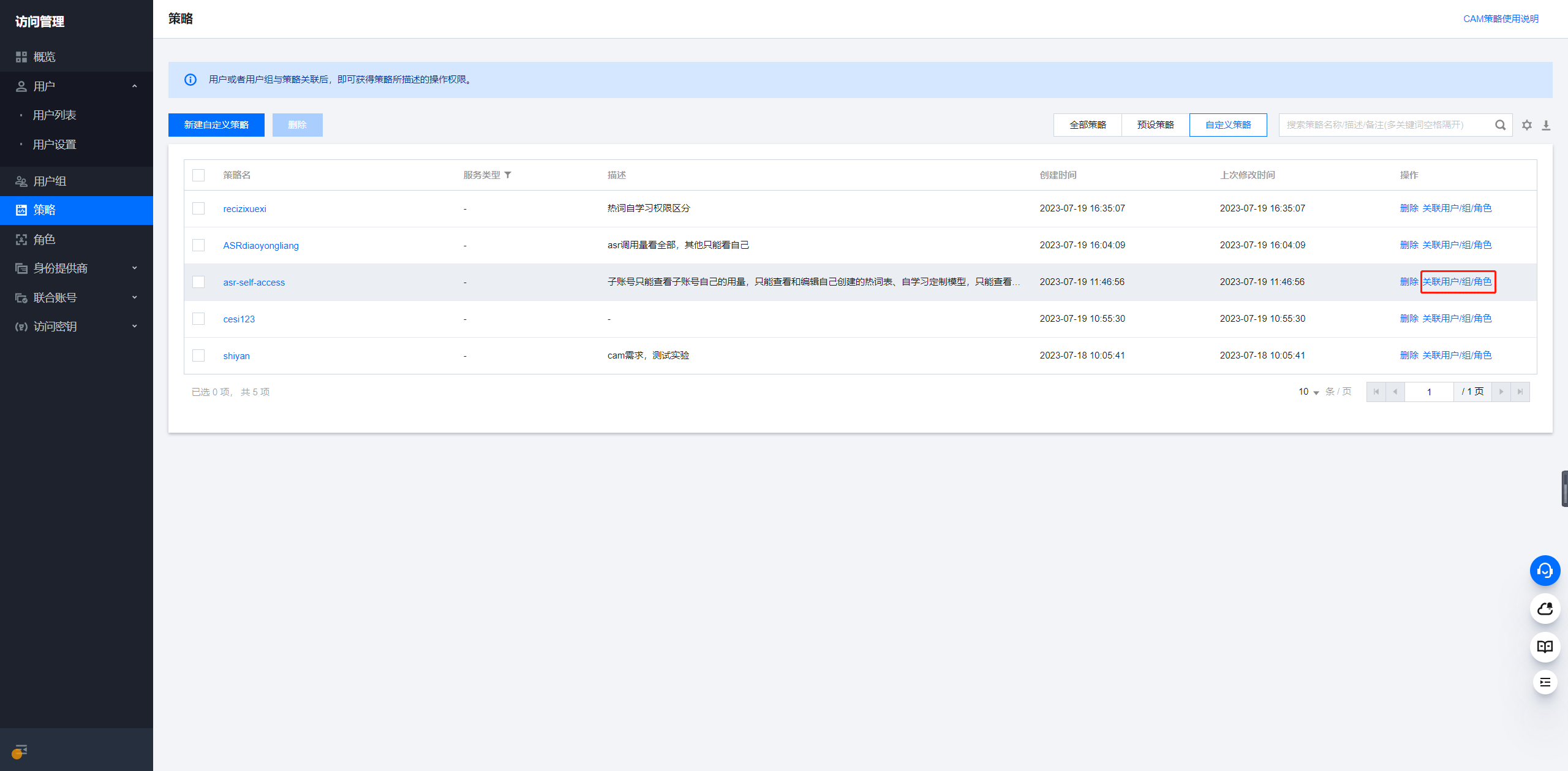
第二步:选择需要授权的用户/用户组/角色,单击确定完成策略关联。
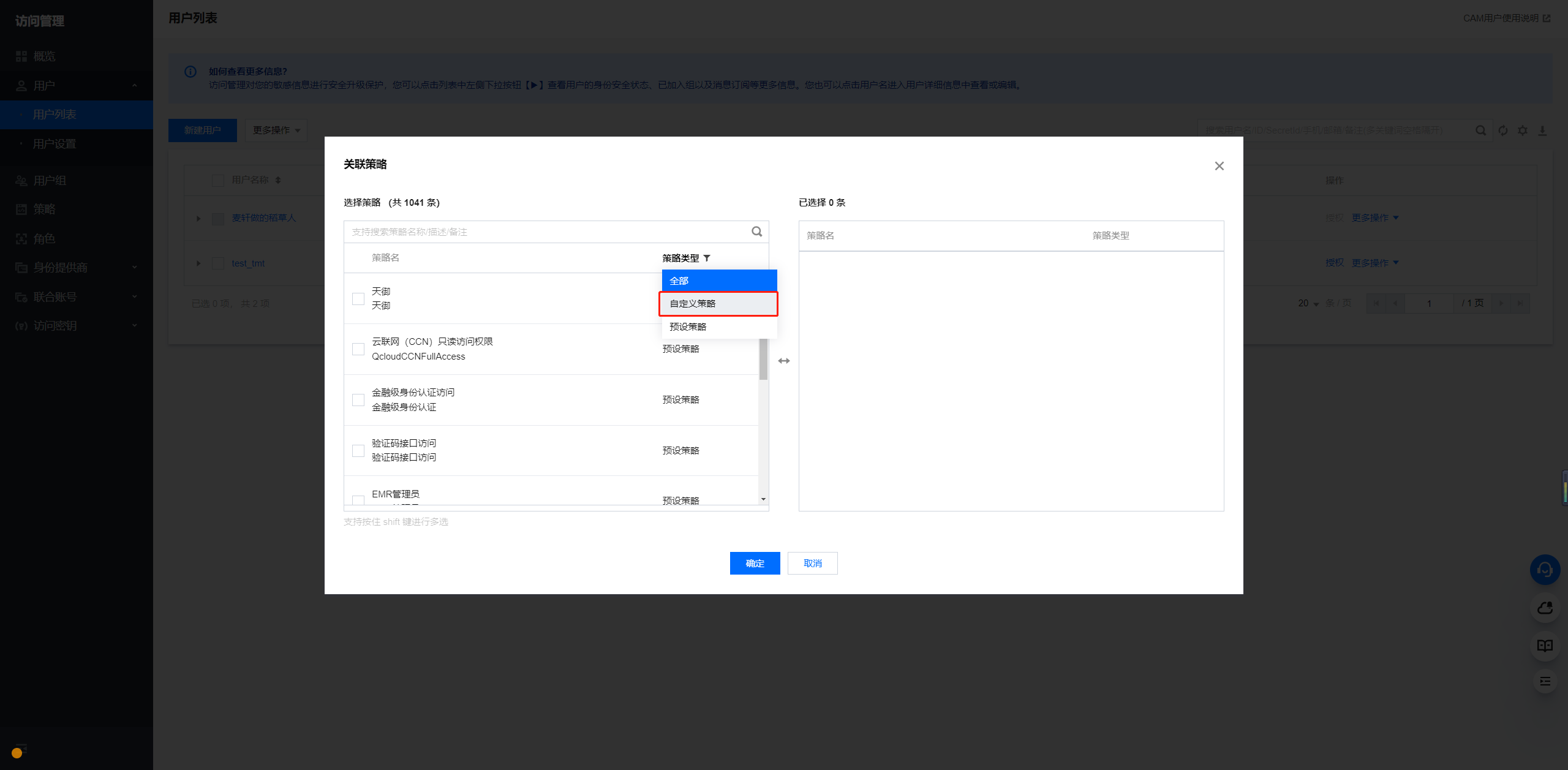
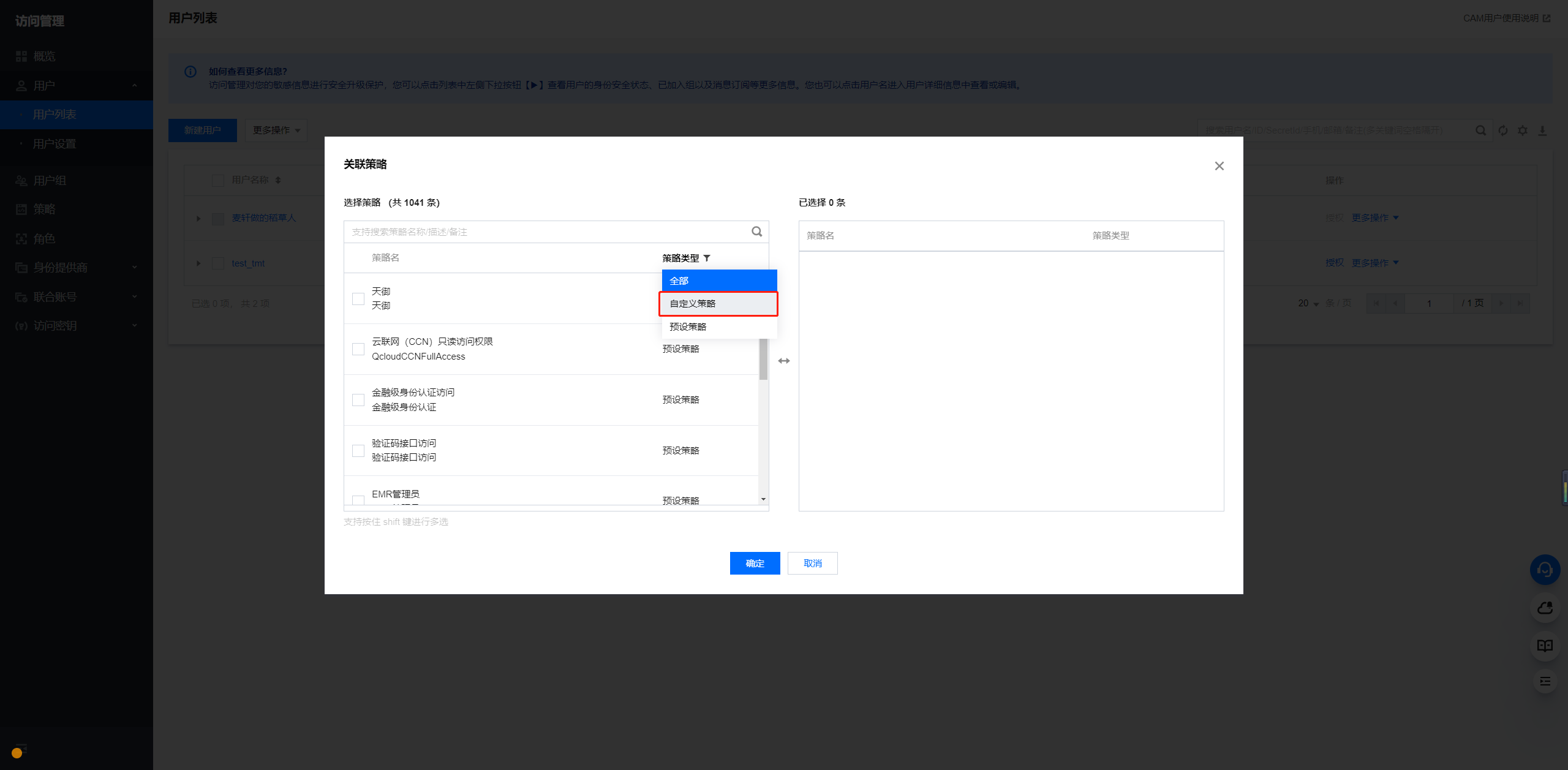
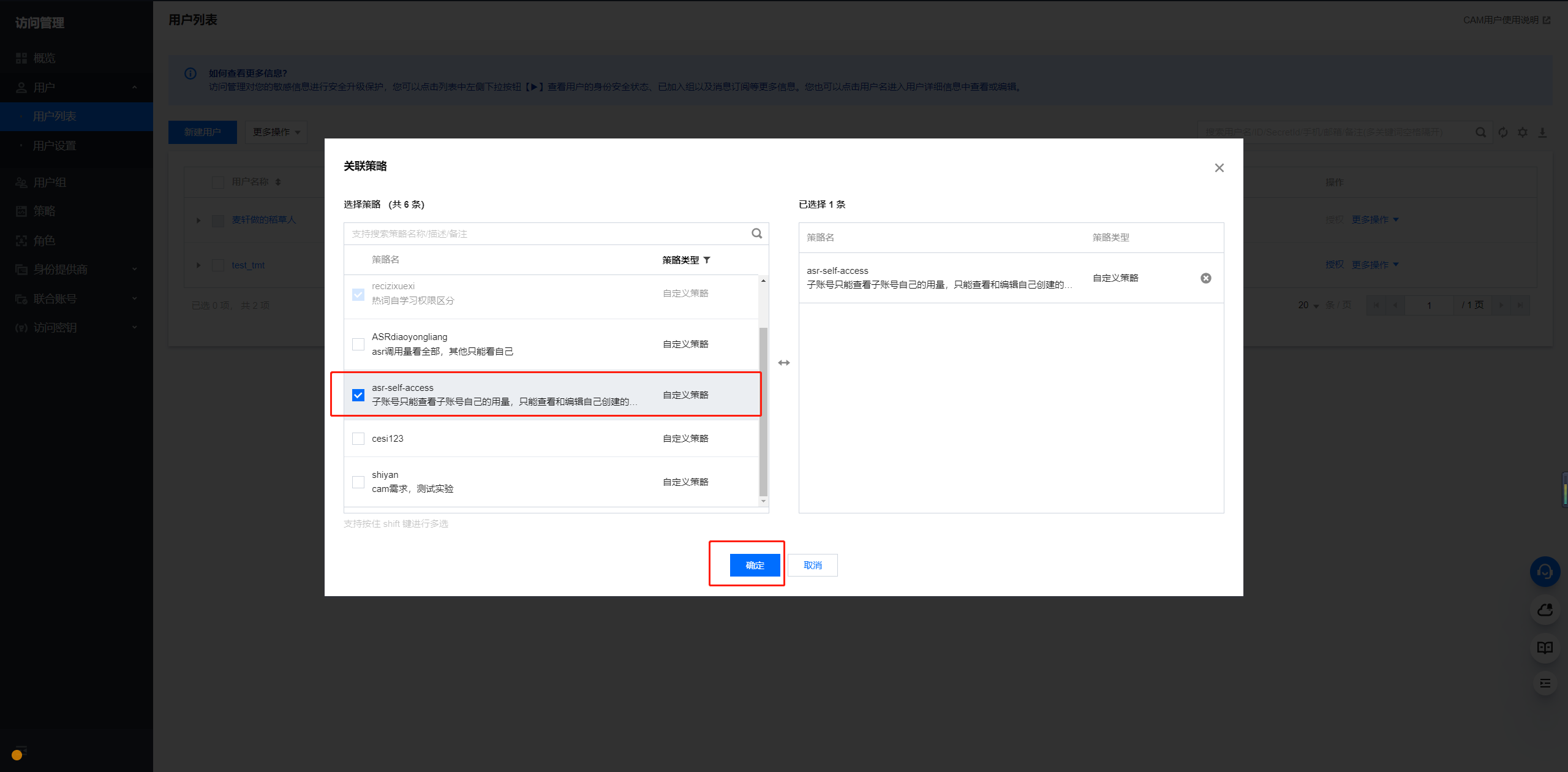
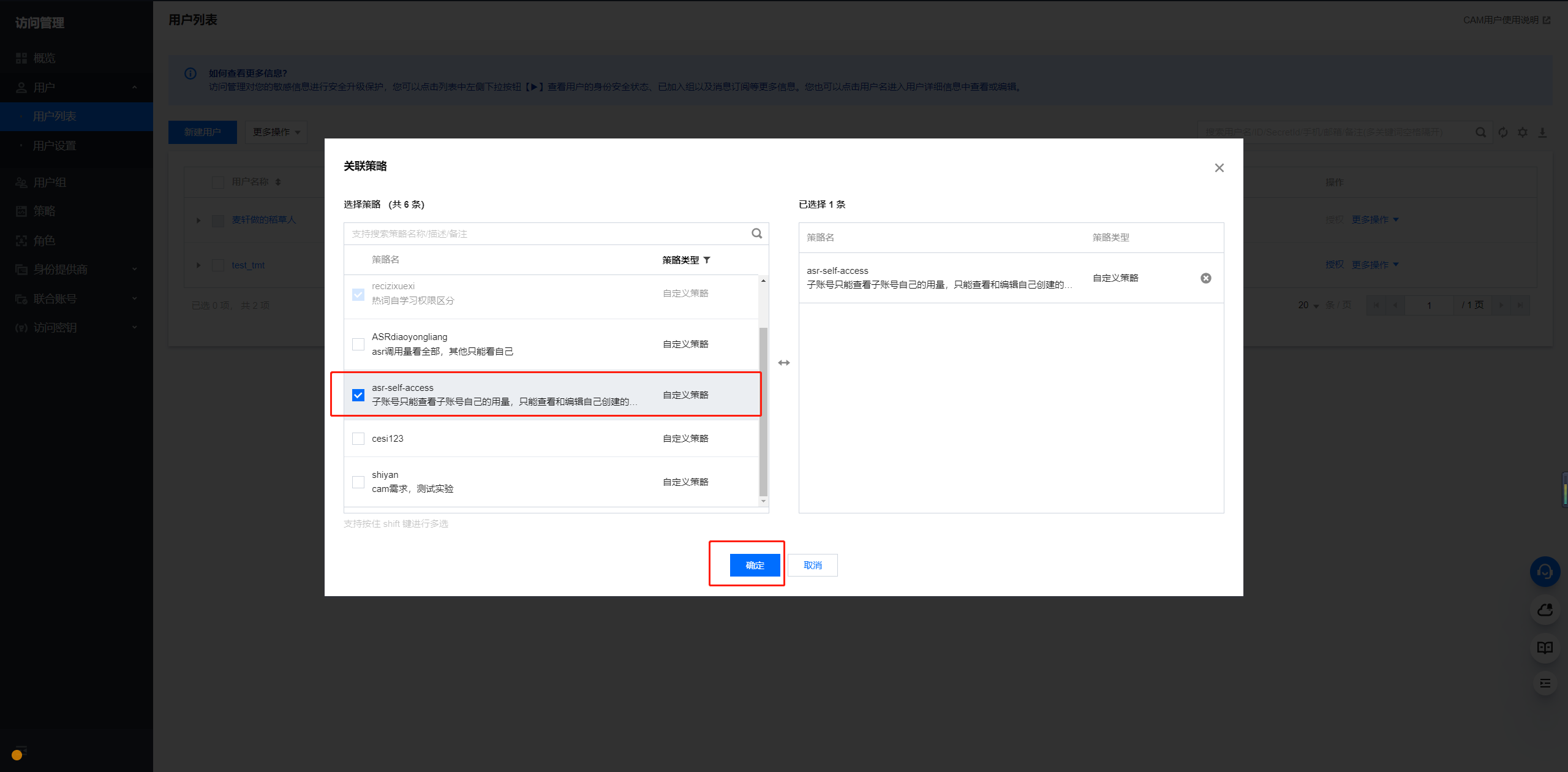
方式二:在用户列表授予策略
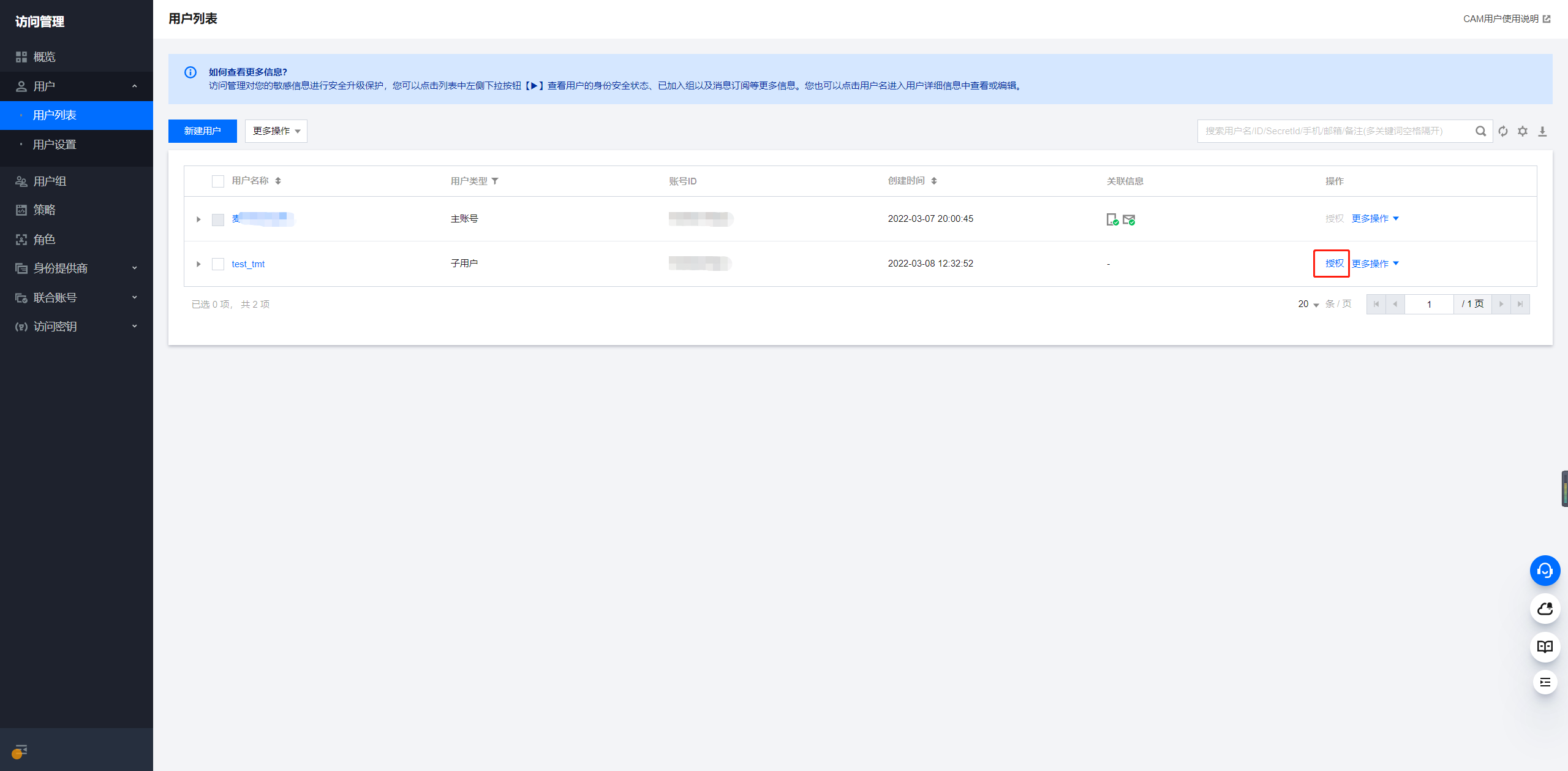
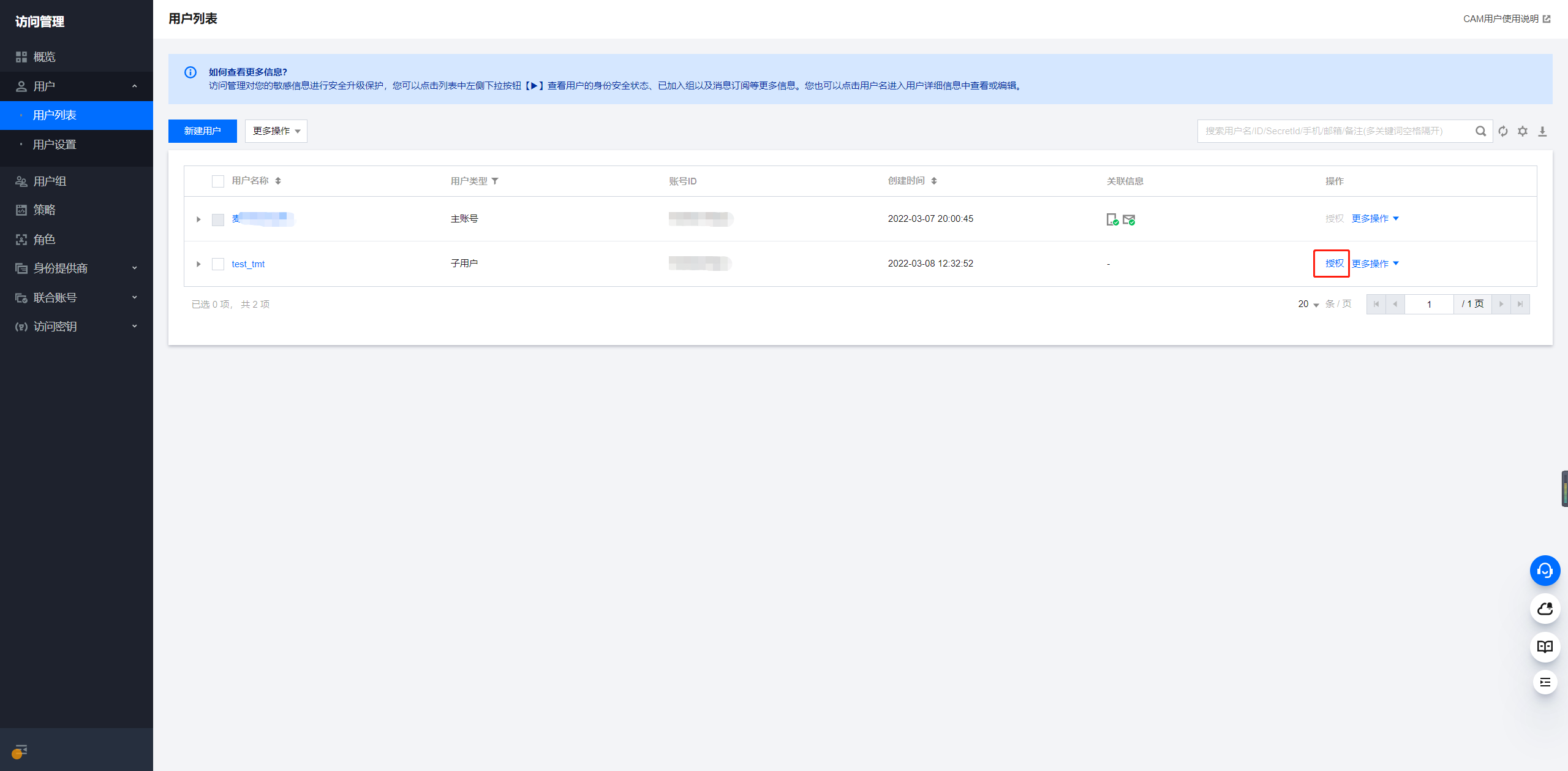
第二步:选择自定义策略,单击确定进入自定义策略列表。
第三步:选择此前配置好的自定义策略,单击确定完成策略授予。
预设 JSON 策略
场景一:子账号只能读写自己
如果您需要限制 所有子账号 :
只能看自己的用量
只能查看和编辑自己申请的离在线SDK申请表
可使用以下 JSON 策略:
{"statement": [{"action": ["tts:DescribeStatInfo","tts:DescribeStatInfoUrl","tts:DescribeUserInfo","tts:ActivateAuth","tts:InvokeSDKFunction"],"effect": "allow","resource": ["qcs::tts::uin/{替换为您的主账户uin}:subUin/${uin}"]},{"action": ["tts:ActivateService","tts:DescribeOpenStatus","tts:GetQuotaConfig","tts:GetQpsStatistics","tts:DescribePidOrders","tts:DescribeQuotaPkgs","tts:CheckFreePackage","tts:DescribeVoices","tts:CreateShortSynthesizeTask","tts:DescribeLongSpeechTasks","tts:CreateSynthesizeLongSpeechTask","tts:SetPayMode","tts:TextToVoice","tts:DownloadLongSpeechTasks","tts:DeleteLongSpeechTasks","tts:ChangeTaskName","tts:SendFreePackage","tts:CreateTextFromUrl","tts:DescribeVrsUserInfo"],"effect": "allow","resource": ["*"]}],"version": "2.0"}
场景二:子账号拥有全读写权限(等同于主账号)
如果您需要允许 所有子账号 拥有与主账号同等的全读写权限
可用预设策略:QcloudTTSFullAccess 并关联 / 授权所有用户