操作场景
安全组 是一种有状态的包含过滤功能的虚拟防火墙,用于设置单台或多台云数据库的网络访问控制,是腾讯云提供的重要的网络安全隔离手段。安全组是一个逻辑上的分组,您可以将同一地域内具有相同网络安全隔离需求的云数据库实例加到同一个安全组内。云数据库与云服务器等共享安全组列表,安全组内基于规则匹配,具体规则与限制请参见 安全组详细说明。
说明:
云数据库 SQL Server 安全组目前仅支持私有网络 VPC 内网访问和外网访问的网络控制,暂不支持对基础网络的网络控制。
由于云数据库没有主动出站流量,因此出站规则对云数据库不生效。
云数据库 SQL Server 安全组支持主实例、只读实例。
为云数据库配置安全组
步骤一:创建安全组
1. 登录 控制台。
2. 在左侧导航选择安全组页,选择地域,单击新建。
3. 在弹出来的对话框中,完成如下配置,确认后单击确定。
模板:根据安全组中的数据库实例需要部署的服务,选择合适的模板,简化安全组规则配置。如下表所示:
模板 | 说明 | 场景 |
放通全部端口 | 默认放通全部端口到公网和内网,具有一定安全风险。 | - |
放通22,80,443,3389端口和ICMP协议 | 默认放通22,80,443,3389端口和 ICMP 协议,内网全放通。 | 此模板对云数据库不生效。 |
自定义 | 安全组创建成功后,按需自行添加安全组规则。具体操作请参见下文“添加安全组规则”。 | - |
名称:自定义设置安全组名称。
所属项目:默认选择“默认项目”,可指定为其他项目,便于后期管理。
备注:自定义,简短地描述安全组,便于后期管理。
步骤二:添加安全组规则
1. 在 安全组页,在需要设置规则的安全组行中,单击操作列的修改规则。
2. 在安全组规则页面,选择入站规则 > 添加规则。
3. 在弹出的对话框中,设置规则。
类型:默认选择“自定义”,您也可以选择其他系统规则模板,推荐选择 SQL Server(1433) 模板。
来源:流量的源(入站规则) 或目标(出站规则),请指定以下选项之一:
指定的源/目标 | 说明 |
单个 IPv4 地址或 IPv4 地址范围 | 用 CIDR 表示法(如203.0.113.0、203.0.113.0/24或者0.0.0.0/0,其中0.0.0.0/0代表匹配所有 IPv4 地址)。 |
单个 IPv6 地址或 IPv6 地址范围 | 用 CIDR 表示法(如FF05::B5、FF05:B5::/60、::/0或者0::0/0,其中::/0或者0::0/0代表匹配所有 IPv6 地址)。 |
引用安全组 ID,您可以引用以下安全组的 ID: 安全组 ID 其他安全组 | 当前安全组表示与安全组关联的云服务器。 其他安全组表示同一区域中同一项目下的另一个安全组 ID。 |
- |
协议端口:填写协议类型和端口范围,您也可以引用 参数模板 中的协议端口或协议端口组。
说明:
连接云数据库 SQL Server 须开通1433协议端口。
策略:默认选择“允许”。
允许:放行该端口相应的访问请求。
拒绝:直接丢弃数据包,不返回任何回应信息。
备注:自定义,简短地描述规则,便于后期管理。
4. 单击完成,完成安全组入站规则的添加。
案例
场景:您创建了一台云数据库 SQL Server,并希望通过云服务器 CVM 访问云数据库 SQL Server。
解决方法:添加安全组规则时,在“类型”中选择 SQL Server(1433),开通1433号协议端口。
您还可以根据实际需求,放通全部 IP 或指定 IP(IP 段),配置可通过 CVM 访问云数据库 SQL Server 的 IP 来源。
方向 | 类型 | 来源 | 协议端口 | 策略 |
入方向 | SQL Server(1433) | 全部 IP:0.0.0.0/0 指定 IP:输入您指定的 IP 或 IP 段 | TCP:1433 | 允许 |
步骤三:配置安全组
安全组是腾讯云提供的实例级别防火墙,可以对云数据库进行入流量控制。您可以在购买实例时绑定安全组,也可以购买实例后在控制台绑定安全组,以下分别介绍两种场景下配置安全组的操作。
注意:
目前云数据库 SQL Server 安全组仅支持私有网络云数据库配置。
场景一:购买实例时绑定安全组
场景一:购买实例时绑定安全组
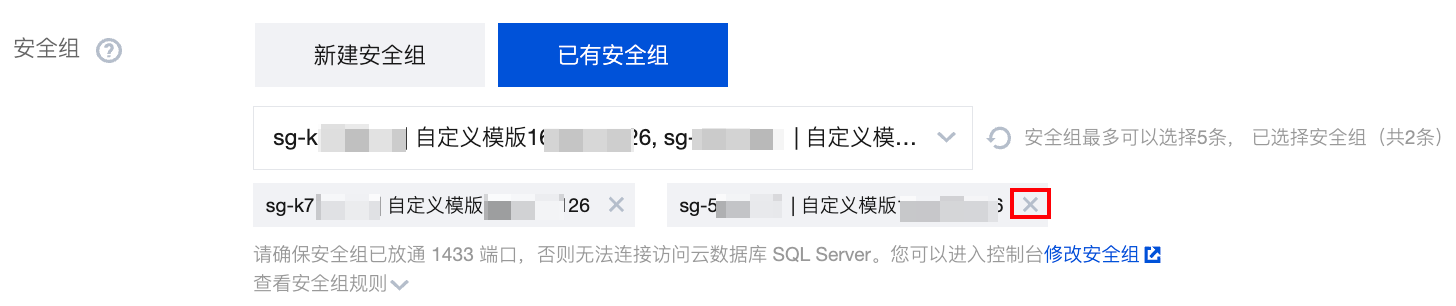
创建安全组后,支持在新购实例时绑定安全组,可选择该腾讯云账号下同一地域内的所有安全组,并支持多选安全组和通过模糊搜索快速找到目标安全组。
1. 登录 SQL Server 购买页。
2. 单击参数安全组>选择已有安全组下面的方框,在方框内勾选目标安全组,支持多选,支持通过模糊搜索安全组名称快速找到目标安全组。

3. 完成其他购买页参数配置后,单击立即购买。
说明:
支持在勾选多个安全组后单击删除多余绑定的安全组,默认至少保留一个安全组。
场景二:购买实例后在控制台绑定安全组
1. 登录 SQL Server 控制台, 在实例列表,选择需要配置安全组的实例,单击操作列的管理,进入实例管理页面。
2. 选择安全组页签,单击配置安全组。
3. 在弹出的对话框中选择需要绑定的安全组,单击确认,即可完成安全组绑定云数据库的操作。
导入安全组规则
1. 在 安全组页,选择需要的安全组,单击安全组 ID/名称。
2. 在入/出站规则页签上,单击导入规则。
3. 在弹出的对话框中,选择已编辑好的入站/出站规则模板文件,单击开始导入。
说明:
如果需要导入规则的安全组下已存在安全组规则,建议您先导出现有规则,否则导入新规则时,将覆盖原有规则。
克隆安全组
1. 在 安全组页,在列表的操作列选择更多 > 克隆。
2. 在弹出的对话框中,选定目标地域、目标项目后,单击确定。若新安全组需关联 CVM,请重新进行管理安全组内云服务器。
删除安全组
1. 在 安全组页,选择需要删除的安全组,在操作列选择更多 > 删除。
2. 在弹出的对话框中,单击确定。若当前安全组有关联的 CVM 则需要先解除安全组才能进行删除。
相关 API
API | 描述 |
接口(DescribeDBSecurityGroups)用于查询实例的安全组详情。 | |
接口(DescribeProjectSecurityGroups)用于查询项目的安全组详情。 | |
接口(ModifyDBInstanceSecurityGroups)用于修改实例绑定的安全组。 | |
接口(AssociateSecurityGroups)用于安全组批量绑定实例。 | |
接口(DisassociateSecurityGroups)用于安全组批量解绑实例。 |