本文档旨在指导用户如何进行告警设置,以便及时获取主机安全告警、日志容量预警、客户端运行情况、安全播报等消息。
告警目录
告警大类 | 告警类型 | 告警项 | 告警主机范围 | 站内信/短信/邮件等 | 机器人通知 |
| | | | 告警时间 | 告警时间 |
资产指纹 | 高危端口暴露 | 服务器存在高危端口暴露风险。 | 全部主机 | 9:00 ~ 18:00 | 暂不支持 |
入侵检测 | 文件查杀-恶意文件 | 严重、高危、中危、低危、提示。 | 全部/自选主机 | 全天/自定义 说明: 为减少对用户的打扰,告警已做如下限制: 告警周期开始时,前 3 条安全告警实时通知,后续每 2 小时汇总通知 1 次。 非告警时间段内产生的告警,将在告警时间开始时统一汇总通知。 | 实时 |
| 文件查杀-异常进程 | 检测到内存中存在正在运行的异常进程。 | | | |
| 异常登录 | 高危、可疑。 | | | |
| 密码破解 | 登录密码被破解成功。 | | | |
| 恶意请求 | 服务器请求了恶意域名。 | | | |
| 高危命令 | 高危、中危、低危。 | | | |
| 本地提权 | 系统中出现低权限用户试图提高权限。 | | | |
| 反弹 Shell | 服务器上出现 Shell 反向连接。 | | | |
漏洞管理 | 应急漏洞 | 严重、高危、中危、低危。 | | | |
| Linux 软件漏洞 | 严重、高危、中危、低危。 | | | |
| Windows 系统漏洞 | 检出未修复的补丁 | | | |
| Web-CMS 漏洞 | 严重、高危、中危、低危。 | | | |
| 应用漏洞 | 严重、高危、中危、低危。 | | | |
基线管理 | 安全基线 | 存在检测不通过的基线项(账号相关、弱口令、未授权类的基线)。 | | | |
高级防御 | 网络攻击 | 攻击成功、尝试攻击。 | | | |
| 勒索监测 | 检测到诱饵文件被篡改。 | | | |
| 应用防护-漏洞防御 | 仅告警、已防御。 | | | |
| 应用防护-内存马扫描 | 检测到 JavaWeb 服务进程中存在内存马 | | | |
| 应用防护-内存马注入 | 仅告警、已防御。 | | | |
| 核心文件监控 | 高危、中危、低危、无。 | | | |
客户端相关 | 客户端离线 | 检测到客户端异常离线,且达到一定时间未重新上线。 | | | |
| 客户端卸载 | 检测到客户端被卸载。 | | | |
日志分析 | 日志分析存储-自定义 | 当日志存储达到自定义阈值时触发告警。 | 不涉及 | 实时 | |
| 日志分析存储-全量 | 当日志存储达到 100% 时触发告警。 | 不涉及 | 实时 | |
资讯相关 | 安全报告 | 提供免费高价值安全线索及行业安全新动态 | 不涉及 | 每周一次 | 暂不支持 |
| 安全播报 | 安全公告、版本发布、功能更新、实践教程、行业荣誉。 | 不涉及 | 实时 | 暂不支持 |
站内信/短信/邮件等
1. 在配置告警规则前,需要先在 消息中心 > 消息订阅 中完成主机安全基础订阅设置:
在 消息中心 > 消息订阅 中找到主机安全,确保其消息免打扰开关处于关闭状态。
单击编辑,打开订阅编辑弹窗,接收渠道勾选站内信、邮件、短信、微信、企业微信(主机安全暂不支持语音通知,即便勾选也不会生效),按需配置消息接收人后,单击确定完成主机安全通知的基础订阅设置。
说明:
2. 在主机安全控制台 设置中心 > 通知设置 中,选择站内信/短信/邮件等进行告警规则配置即可。
机器人通知
在站内信/短信/邮件等中,消息接收人仅支持用户或用户组;如需将告警通知发送到 IM 群,请使用机器人通知方式进行配置。您还可以按不同机器人分别设置告警策略,实现差异化通知。
说明:
1. 登录 主机安全控制台,在左侧导航栏,选择设置中心 > 通知设置。
2. 在通知设置页面,选择机器人通知 > 接收机器人管理。
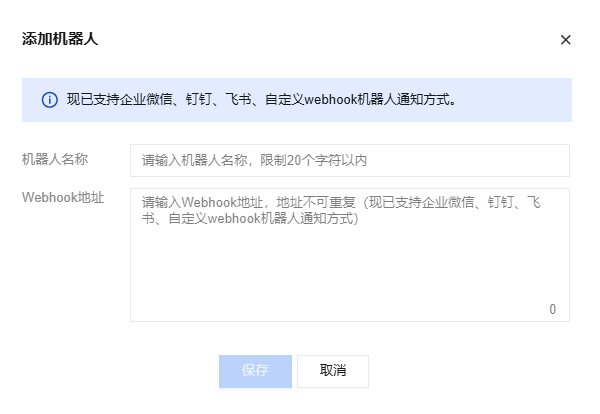
3. 单击添加机器人,填写机器人名称和 Webhook 地址,单击保存。
4. 选择告警策略配置,单击新建告警策略,配置策略名称、启用状态、告警范围等信息并关联刚刚创建的接收机器人。

5. 单击保存,后续主机安全将按您配置的策略进行消息通知。