日志分析是主机安全防护解决方案的重要组成,提供主机相关安全事件日志,支持 SQL 检索与查询,并提供可视化报表与统计,帮助用户快速排查入侵、溯源定位等安全运营工作。本文档将为您介绍如何使用日志分析功能。
限制说明
可收集日志数据,受主机防护版本限制如下。
日志大类 | 日志类型 | 日志描述 | 支持版本 |
主机资产日志 | 主机信息 | 包含主机实例 ID、IP、操作系统、地域、VPC、实例状态、是否安装主机安全客户端等主机信息。 说明: 仅主机的“同步时间”变更,其余信息不变,不会产生日志流水。 | 全部主机 |
| 资产指纹 | 包含资源监控、账号、端口、软件应用、进程、数据库、Web 应用、Web 服务、Web 框架、Web 站点、Jar 包、启动服务、计划任务、环境变量、内核模块、系统安装包。 说明: 仅资产指纹的“数据更新时间”变更,其余信息不变,不会产生日志流水。 | 专业版、旗舰版 |
客户端上报日志 | 客户端上报 | 主机原始日志(包含如:系统认证和授权信息、系统安全信息、系统消息、系统审计信息等内容);DNS 日志、进程快照日志、网络五元组日志、文件监控日志、登录流水日志。 | 专业版、旗舰版 |
告警日志 | 入侵检测 | 文件查杀(恶意文件)、文件查杀(异常进程)、异常登录、密码破解、恶意请求、高危命令、本地提权、反弹 Shell。 | 专业版、旗舰版 |
| 漏洞管理 | 应急漏洞、Linux 软件漏洞、Windows 系统漏洞、Web-CMS 漏洞、应用漏洞。 | 专业版、旗舰版 |
| 基线管理 | 安全基线。 | 专业版、旗舰版 |
| 高级防御 | Java 内存马、核心文件监控。 | 旗舰版 |
| | 网络攻击。 | 专业版、旗舰版 |
| 客户端相关 | 客户端离线、客户端卸载。 | 基础版及以上 |
使用日志投递功能,须先 购买腾讯云消息队列 Ckafka 实例,按照需要投递的日志量来选购对应 Ckafka 实例规格。
日志投递功能,仅支持使用一个消息队列 Ckafka 账号进行投递。
根据《网络安全法》规定,日志存储时长不少于6个月,推荐每台服务器配置20-40GB存储容量,以便采集和留存日志数据。
操作指南
1. 登录 主机安全控制台。
2. 在左侧导航栏,选择日志分析,可进行日志存储设置、日志查询、日志投递等操作。
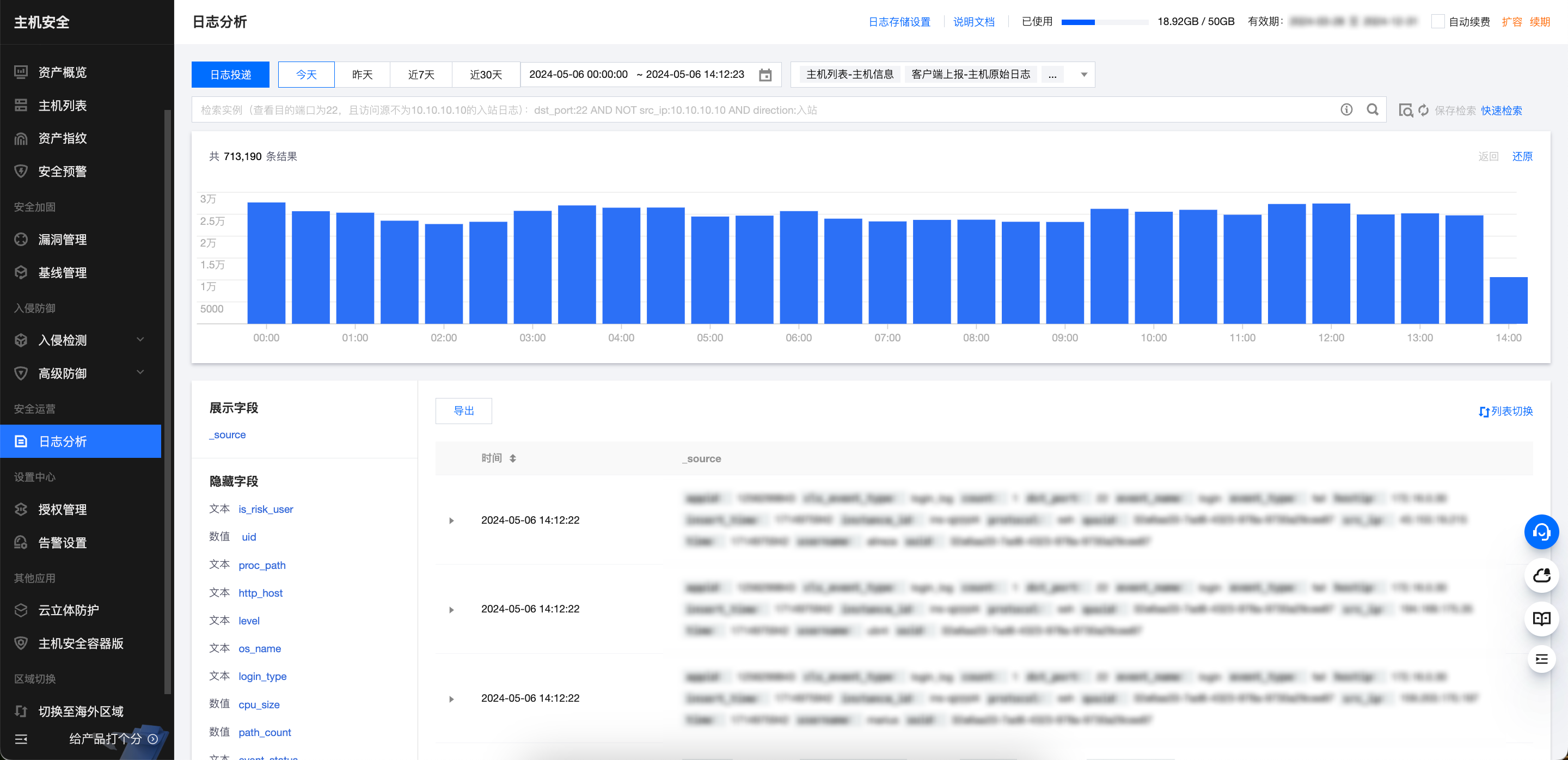
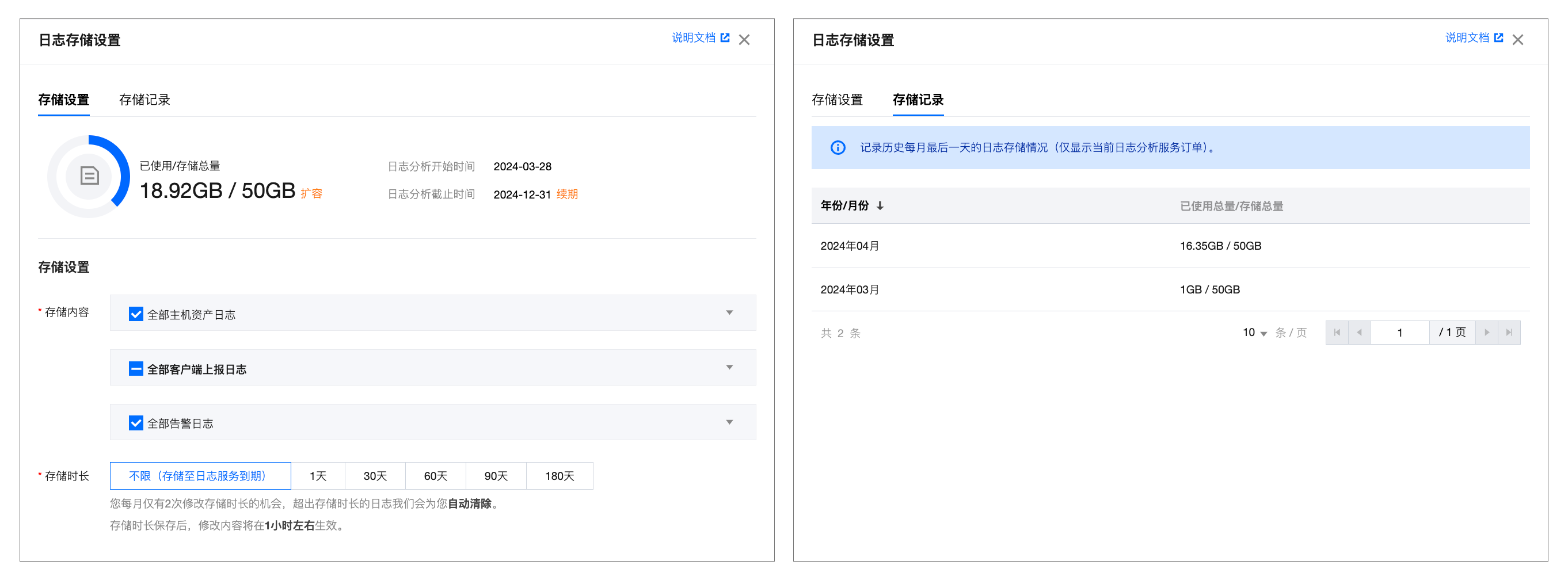
日志存储
单击日志存储设置,弹窗如下,在存储设置中,可查看当前日志存储情况,可对存储内容、存储时长进行配置。在存储记录中,可查看历史每月最后一天零点日志存储的情况,默认倒序展示。
查看日志
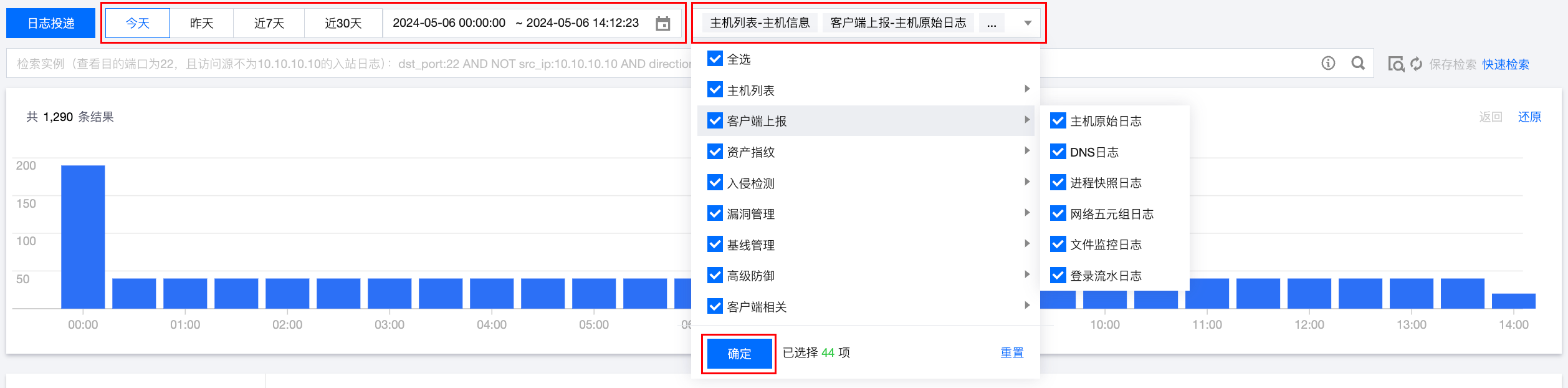
在日志分析页面,支持按照如下方式筛选日志。
按时间或类型筛选:在日志分析页面上方,支持按时间和日志类型筛选日志,选定时间范围或日志类型,单击确定即可。
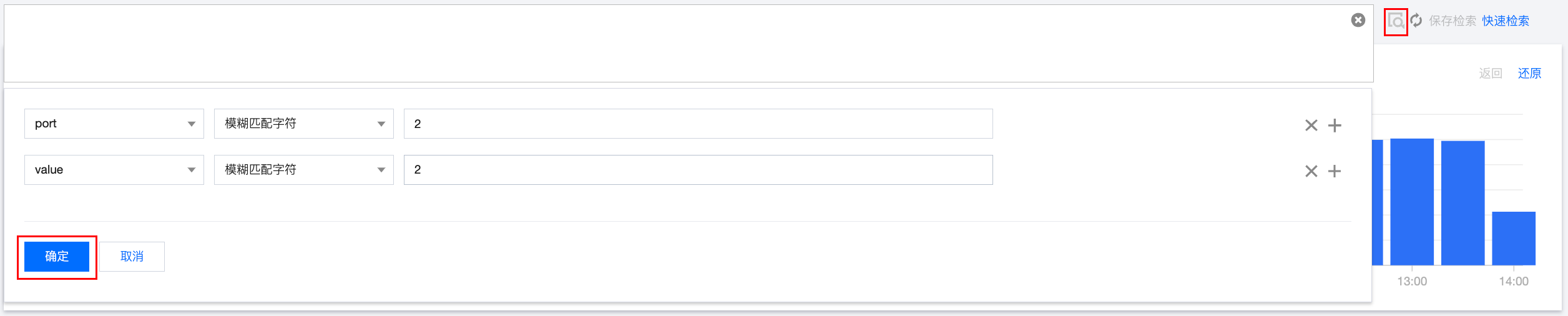
按字段值筛选:在日志分析页面上方,支持搜索框输入字段值筛选、选择字段匹配筛选两种方式。
搜索框输入字段值筛选:参考下图示例,在搜索框中输入想要搜索的字段和字段值,单击

语法 | 语义 | 示例 |
key:value | 键值搜索,value 支持模糊搜索,支持 key:(value1 OR value2) | src_ip:10.0.0.1;src_ip:(10.0.0.1 OR 10.10.0.1) |
A AND B | “与”逻辑,返回 A 与 B 的交集结果 | src_ip:10.0.0.1 AND protocol:TCP |
A OR B | “或”逻辑,返回 A 或 B 的并集结果 | src_ip:10.0.0.1 OR protocol:TCP |
NOT B | “非”逻辑,返回不包含 B 结果 | NOT src_ip:10.0.0.1 |
A NOT B | “减”逻辑,返回符合 A 但不符合 B 的结果,即 A-B | src_ip:10.0.0.1 NOT protocol:TCP |
* | 模糊搜索关键字,匹配零个、单个或多个任意字符,不支持开头*,输入 abc*,返回以 abc 开头的结果 | src_ip:10.10* |
? | 模糊搜索关键字,特定位置匹配单个字符,输入 ab?c*,返回以 ab 为开头, 以 c 为结尾的结果,且两者间有且只有一个字符 | src_ip:10.1?.0.1 |
> < >= <= | 大于、小于、大于等于、小于等于,针对数值类型的字段 | src_ip:>=100;src_ip:(>=10 AND <20) |
[] {} | 范围查询,中括号[]表示闭区间,{}表示开区间 | src_ip:[1 TO 5} |
() | 布尔运算符不遵循优先级规则,当使用多个运算符时,使用括号指定优先级 | src_ip:10.0.0.1 AND (protocol:TCP OR src_port:80) |
注意:
语法关键词区分大小写。
选择字段匹配筛选:单击

说明:
针对常用的检索可保存检索 ,下次直接单击快速检索,选中要原先保存的检索内容进行筛选即可。
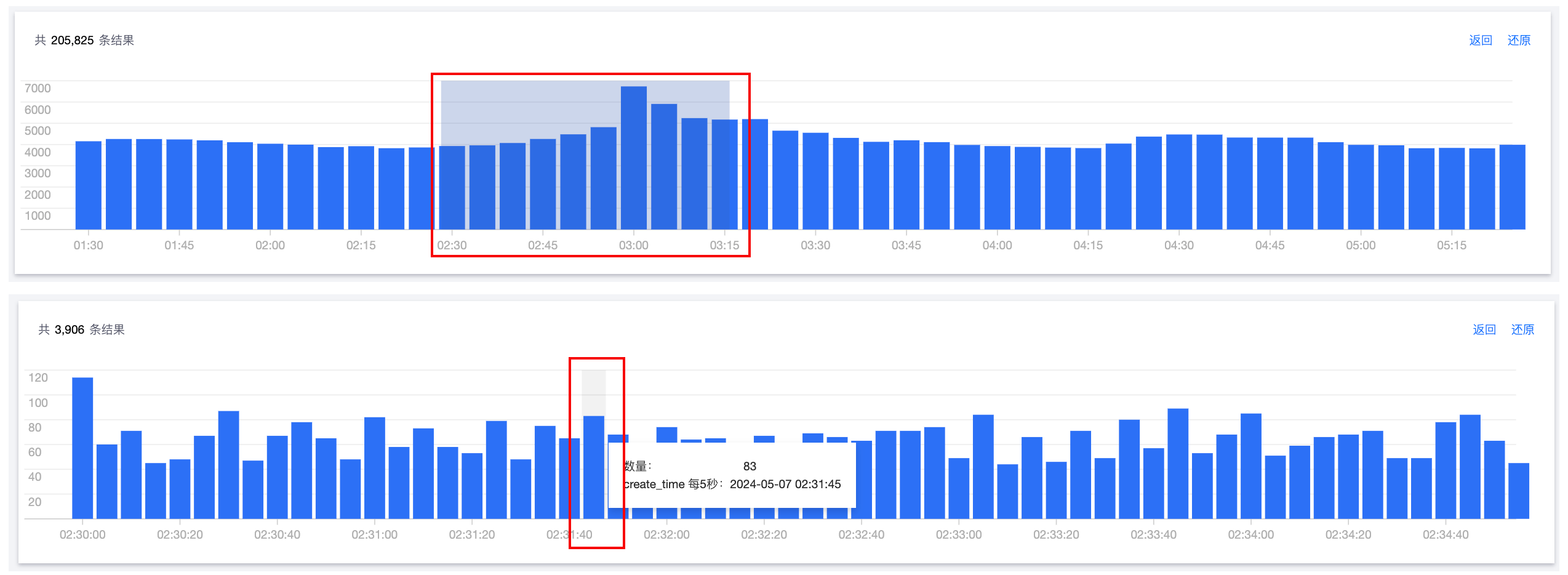
在日志分析页面,鼠标单击柱状图或单击后滑动,可快速选定时间范围,进行下钻查看。
在日志分析页面,在列表左侧的字段导航中,可自定义展示字段和隐藏字段。

单击导出,可将满足检索条件的日志导出为文件,并通过浏览器下载到本地。
说明:
单次最多支持导出60000条日志,最大支持每种类型导出10000条数据。
日志投递
投递至Ckafka
在日志分析页面,您可配置主机安全不同日志类型分别投递到指定 Ckafka 实例的不同 Topic 中。
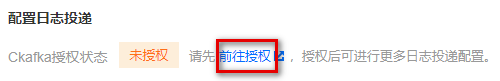
1. 单击左上角的日志投递,打开日志投递配置弹窗,首次若未授权 Ckafka 服务,须先单击前往授权,同意服务授权后才可进行更多日志投递配置。
2. 同意授权服务后,须选择消息队列实例、网络接入方式,输入所选消息队列实例的用户名和密码,并进行连通性测试。
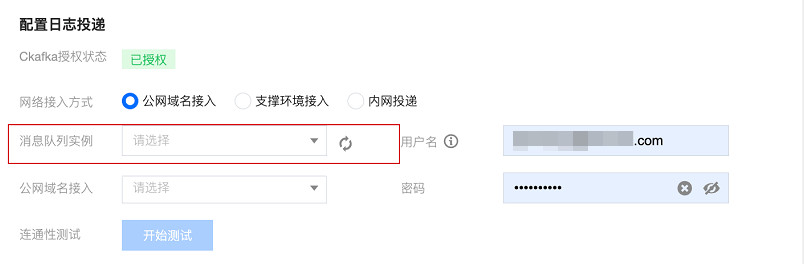
3. 选择网络接入方式。
网络接入方式 | 描述 | 可选路由说明 |
公网域名接入 | 通过公网进行日志投递。 | 是消息队列实例中所定的接入方式。 |
支撑环境接入 | 通过腾讯云内网进行日志投递,性能更高。 | 是消息队列实例中所定的接入方式,仅支持 SASL_PLAINTEXT 接入方式。 |
内网投递 | 通过腾讯云内网进行日志投递,但路由无需用户在 Ckafka 中进行配置,会自动创建一个不可见的内部路由来支持接入。 | - |
说明:
网络接入方式若选择“公网域名接入”、“支撑环境接入”,还需要选择接入路由,路由策略对应 Ckafka 实例列表 详情中的接入方式。
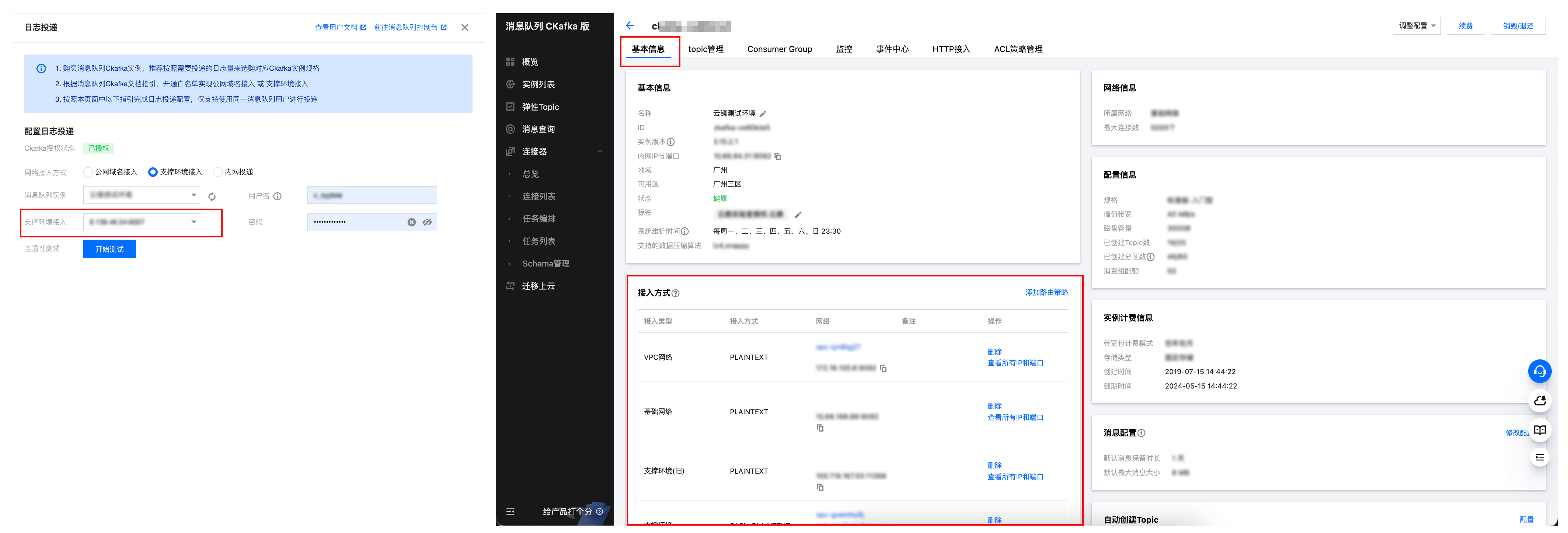
网络接入方式若选择“公网域名接入”、“支撑环境接入”,还需要填写 Ckafka 实例的用户名和密码,用户名密码在 Ckafka 实例列表 详情中的 ACL 策略管理 > 用户管理 添加。(在配置日志投递时,仅填写#后的用户名即可,无需填写#及其前的 Ckafka 实例 ID。)

4. 完成上述 Ckafka 配置后,可进行连通性测试,测试通过后,您可对要进行投递的日志配置不同的 Topic(不进行投递的日志类型,可以不选择 Topic ID)。

5. 日志投递配置完成后,再次单击日志投递,可查看日志投递详情。

基本信息:展示 Ckafka 实例的基本信息。
说明:
您需要关注“状态”字段,当展示告警或异常时,请单击查看监控,查看 Ckafka 服务是否异常,或者是否配额不足。
投递开关:用于控制指定的日志类型,启动或停止日志投递任务,您可以在投递开关列,通过开关按钮控制日志投递任务。
投递状态:正常、异常(此状态会中止投递)、未开启。
编辑:单击编辑,可再次编辑要投递的日志类型和 Topic ID。
查看监控:单击查看监控,会跳转至消息队列 Ckafka 控制台的监控页面,您可以查看网络流量、峰值带宽、消息条数、磁盘占用等情况。
重新配置:在日志投递列表上方,单击重新配置,将回到已同意 Ckafka 授权服务后的状态,您可对消息队列实例、网络接入方式、日志类型、Topic ID 等进行重新配置。
说明:
重新配置,会中断当前的投递进程。
投递至CLS
在日志分析页面,您可配置主机安全不同日志类型分别投递到指定 CLS 的不同日志主题中。
1. 单击左上角的日志投递,打开日志投递配置弹窗,首次若未授权 CLS 服务,须先单击前往授权,同意服务授权且创建服务角色后才可进行更多日志投递配置。
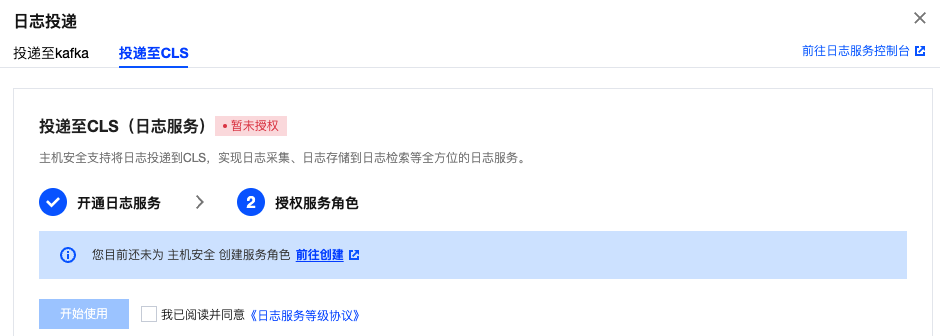
说明:
将日志投递到 CLS (日志服务)集中管理,需授权接入 CLS 并开启日志投递开关。
2. 完成上述授权后,可对要进行投递的日志配置不同的日志主题(不进行投递的日志类型,可以不进行配置)。

3. 单击立即配置,可在投递设置弹窗中选择需要投递的日志类型、目标地域、选择日志集和日志主题,单击确定。

4. 配置完成后,单击开启投递开关,该日志类型将投递至您配置的 CLS 日志集及日志主题中。
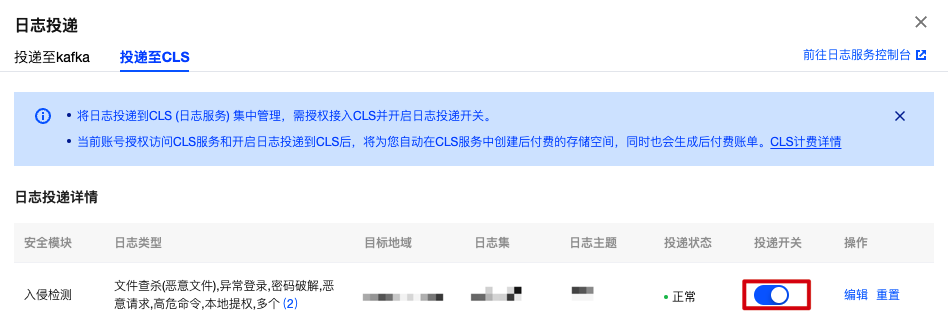
投递开关:用于控制指定的日志类型,启动或停止日志投递任务,您可以在投递开关列,通过开关按钮控制日志投递任务。
投递状态:正常、异常(此状态会中止投递)、未配置。
编辑:单击编辑,可再次编辑要投递的日志集和日志主题。
重置:操作列单击重置,该日志投递已配置内容将被清空,清空内容包含日志类型、投递日志集、投递日志主题,请谨慎操作。