漏洞管理旨在帮助客户扫描系统中存在的安全漏洞,提供漏洞信息和处置方案,支持忽略、手动修复、一键修复。本文档将为您介绍如何进行漏洞管理。
说明:
限制说明
解锁漏洞管理功能,须至少存在1台专业版/旗舰版主机。
漏洞管理范围说明如下:(‘✓’表示支持,‘-’表示暂不支持)。
漏洞管理功能 | 漏洞类型 | Linux 系统 | Windows 系统 |
漏洞扫描 专业版、旗舰版主机适用 | Linux 软件漏洞 | ✓ | - |
| Windows 系统漏洞 | - | ✓ |
| Web-CMS 漏洞 | ✓ | ✓ |
| 应用漏洞 | ✓ | ✓ |
漏洞一键修复 旗舰版主机适用 | Linux 软件漏洞 | ✓ 仅支持部分漏洞 | - |
| Windows 系统漏洞 | - | ✓检出补丁均支持修复 |
| Web-CMS 漏洞 | ✓ 仅支持部分漏洞 | ✓ 仅支持部分漏洞 |
| 应用漏洞 | - | - |
漏洞扫描和一键修复支持的操作系统,详情如下:
操作系统 | 系统版本 | 系统漏洞 | 应用漏洞/Web-CMS 漏洞 |
CentOS | CentOS 5 | ✓ | ✓ |
| CentOS 6 | ✓ | ✓ |
| CentOS 7 | ✓ | ✓ |
| CentOS 8 | ✓ | ✓ |
Debian 说明: 仅支持漏洞扫描,不支持漏洞一键修复。 | Debian 8 | - | ✓ |
| Debian 9 | - | ✓ |
| Debian 10 | - | ✓ |
| Debian 11 | - | ✓ |
| Debian 12 | - | ✓ |
Windows | Windows Server 2008 | ✓ | ✓ |
| Windows Server 2012 | ✓ | ✓ |
| Windows Server 2016 | ✓ | ✓ |
| Windows Server 2019 | ✓ | ✓ |
| Windows Server 2022 | ✓ | ✓ |
| Windows Server 2025 | ✓ | ✓ |
Ubuntu | Ubuntu 16.04 | ✓ | ✓ |
| Ubuntu 18.04 | ✓ | ✓ |
| Ubuntu 20.04 | ✓ | ✓ |
| Ubuntu 21.04 | ✓ | ✓ |
| Ubuntu 22.04 | ✓ | ✓ |
| Ubuntu 24.04 | ✓ | ✓ |
Tlinux/Tencentos | Tlinux | - | ✓ |
Rocky Linux | Rocky Linux | - | ✓ |
OpenCloudOS | OpenCloudOS | - | ✓ |
说明:
操作系统生命周期限制。针对已进入停更状态的操作系统(即官方已停止更新的操作系统的版本),主机安全将不再提供停更时间之后新出现漏洞的扫描和修复支持。停更时间前出现的漏洞仍会得到支持,已支持漏洞的范围也不受影响,停更系统列表如下:
操作系统版本 | 官方停止更新时间 |
Windows Server 2003 | 2015年07月14日 |
Windows Server 2008 | 2020年01月14日 |
Windows Server 2008 R2 | 2020年01月14日 |
Windows Server 2008 SP2 | 2020年01月14日 |
Windows Server 2012 | 2023年10月10日 |
Windows Server 2012 R2 | 2023年10月10日 |
Ubuntu 12.04 LTS | 2017年04月28日 |
Ubuntu 14.04 LTS | 2019年04月 |
Ubuntu 16.04 LTS | 2021年04月 |
Ubuntu 18.04 LTS | 2023年04月 |
CentOS 5 | 2017年03月31日 |
CentOS 6 | 2020年11月30日 |
CentOS 7 | 2024年6月30日 |
CentOS 8 | 2021年12月31日 |
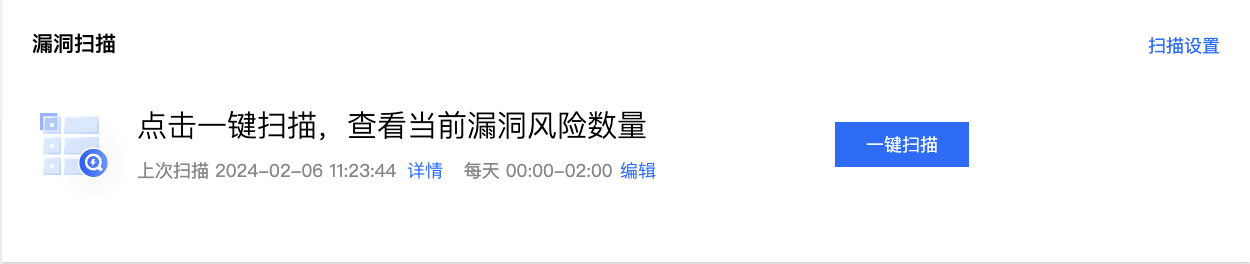
漏洞扫描
1. 登录主机安全控制台,单击左侧导航中的漏洞管理。
2. 在漏洞扫描模块中,支持一键扫描、定时扫描设置。
单击一键扫描,将打开一键扫描设置弹窗,您可对本次扫描的漏洞类别、威胁等级、扫描方式、超时时长、主机范围进行设置。
单击扫描设置将打开漏洞设置弹窗并锚点至定时扫描,您可对定时扫描开关、周期、主机范围和漏洞范围进行设置。
单击详情可查看上一次扫描的详情,并支持下载 PDF 扫描报告、Excel 扫描结果。
漏洞处置
1. 在漏洞管理页下方,您可查看当前检出漏洞的统计情况及详细漏洞列表。
2. 在漏洞概览模块中,展示了漏洞检出情况、网络攻击事件次数及今日新增情况,并展示了主机安全漏洞库总数。
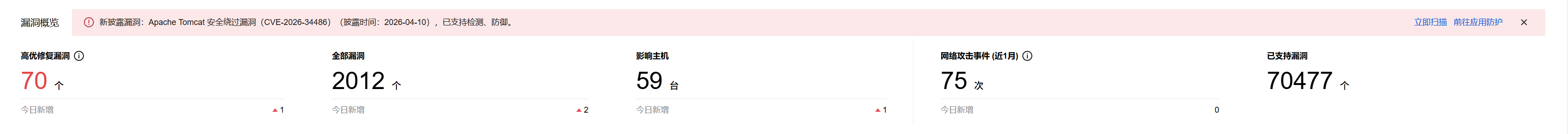
字段说明:
高优修复漏洞:该分类下展示热度攻击漏洞,以及严重/高危漏洞,需要优先修复处理,默认统计待修复漏洞数量。单击自定义规则可对高优修复漏洞进行自定义规则判定。
全部漏洞:检出 Linux 软件漏洞、Windows 系统漏洞、Web-CMS 漏洞、应用漏洞的数量总和。
影响主机:检出漏洞的主机数量。
网络攻击事件:统计近1个月内网络攻击事件的数量。
已支持漏洞:可查看主机安全支持检测的漏洞库,每日最多可检索25次,单次搜索最多可展示100条结果。
3. 在漏洞列表模块中,展示当前检出的具体漏洞,分为“全部漏洞”、“应急漏洞”。
模块 | 子模块 | 描述 |
漏洞列表 | 全部漏洞 | 汇总展示所有检测到的服务器漏洞,涵盖从低危到严重的全部威胁等级,包含已检测到的应急漏洞。全部漏洞根据扫描方式不同又分为了“漏洞”、“Windows 系统补丁”两类。 漏洞:扫描方式为版本对比、POC 验证。 Windows 系统补丁:扫描方式为补丁探测。 |
| 应急漏洞 | 专为新发现、影响广、危害高的紧急漏洞而设,相当于一份重点漏洞走查清单,用户可对其发起手动扫描或设置定期扫描,以确保及时响应高危风险。 |
4. “全部漏洞”与“应急漏洞”二者无太大差异,下面以全部漏洞-漏洞、Windows 系统补丁举例,为您介绍漏洞处置。
全部漏洞-漏洞

字段说明:
漏洞名称/标签:漏洞名称指当前检出的漏洞,标签指该漏洞的标签(如:远程利用、服务重启、存在 EXP 等)。
检测方式:版本对比、POC 验证。
漏洞类型:Linux 软件漏洞、Windows 系统漏洞、Web-CMS 漏洞、应用漏洞。
威胁等级:严重、高危、中危、低危。
全网攻击热度:高、中、低、无热度。
CVSS:指通用漏洞评分系统的评分,分数范围从0到10,0代表最不严重,10代表最严重。
CVE 编号:公共漏洞暴露库中,识别该漏洞的唯一编号。
漏洞修复/防御情况:可防御、可修复。
最后扫描时间:最近一次扫描到该漏洞的时间。
影响主机:存在该漏洞的主机数量。
处理状态:待修复、修复中、扫描中、已修复、已忽略、修复失败。
修复状态:暂无可修复资产、存在可修复资产。
操作
AI 漏洞分析:基于漏洞名称、风险信息生成 AI 解读与处置建议,可快速理解漏洞背景。
详情:查看漏洞详情,了解漏洞说明、影响主机、修复方案等信息。
一键修复:存在可修复资产场景下,对受影响主机一键触发修复,请参见漏洞一键修复。
开启防御:应用防护快捷开启入口。
更多
重新扫描:重新对该漏洞进行扫描,用于确认修复后状态或排查误报/环境变更带来的结果差异。
忽略漏洞:忽略后,受影响主机对该漏洞不再告警,可在漏洞设置中取消忽略或调整主机范围。
全部漏洞-Windows 系统补丁
Windows 系统补丁支持对 Windows 系统漏洞进行检测与修复,替代原有基于 POC 验证的 Windows 系统漏洞检测方式,便于客户按补丁批次统一修复。
说明:
原 Windows 系统漏洞检测方式已由 POC 方式升级为补丁方式,历史已扫描、已忽略、日志分析及各类统计告警中的 Windows 系统漏洞数据将不再展示,建议您评估后进行历史数据清理,并可通过控制台导出原 Windows 系统漏洞历史记录以便留档。

字段说明:
补丁名称/编号(包含多个漏洞):当前补丁包标题与 KB 编号,用于确认补丁归属与检索官方公告。
补丁披露时间:该补丁对应的披露/发布批次时间,用于判断补丁时效。
影响主机:受影响主机数量。
漏洞编号:漏洞唯一编号,用于对齐公告与外部漏洞库信息。
最后扫描时间:最近扫描该补丁的时间。
处理状态:待修复、修复中、扫描中、已修复、已忽略、修复失败。
操作:
一键修复:对受影响主机一键触发补丁修复,请参见漏洞一键修复。
详情:查看该补丁关联漏洞与受影响主机的信息。
重新扫描:重新对该补丁进行扫描,用于确认修复后状态或排查误报/环境变更带来的结果差异。