相关概念
角色
角色(Role)是腾讯云 访问管理(Cloud Access Management,CAM)提供的拥有一组权限的虚拟身份,角色也可被授予策略,主要用于对 角色载体 授予腾讯云中服务、操作和资源的访问权限,这些权限附加到角色后,通过将角色赋予腾讯云的服务,允许服务代替用户完成对授权资源的操作。腾讯云云函数 SCF 的角色分为配置角色和运行角色,您可以通过使用配置角色使 SCF 在服务配置流程中访问用户资源;也可以通过使用运行角色,为运行代码申请临时授权,便于代码通过角色的授权机制实现权限打通和资源访问。
策略
策略 是定义和描述一条或多条权限的语法规范。CAM 支持两种类型的策略,预设策略和自定义策略。预设策略是由腾讯云创建和管理的一些常见的权限集合,如超级管理员、云资源管理员等,这类策略只读不可写。自定义策略是由用户创建的更精细化的描述对资源管理的权限集合。预设策略不能具体描述某个资源,粒度较粗,而自定义策略可以灵活的满足用户的差异化权限管理需求。
权限
权限 是描述在某些条件下允许或拒绝执行某些操作访问某些资源。默认情况下,主账号是资源的拥有者,拥有其名下所有资源的访问权限。子账号没有任何资源的访问权限。资源创建者不自动拥有所创建资源的访问权限,需要资源拥有者进行授权。
操作场景
您在创建云函数 SCF 时,可能会操作部分 SCF 以外的云产品,不同的操作可能需要不同的权限,例如 COS 触发器创建和删除所需的 COS 权限、API 网关触发器创建和删除所需的 API 网关权限、COS 代码文件的 zip 包读取权限等,通过角色的配置和选择可以实现授权。
配置角色
配置角色用于提供 SCF 配置对接其他云上资源的相关权限,在已关联策略的权限范围内访问您的其他云服务资源,包括但不限于代码文件访问、触发器配置。配置角色的预设策略可支持函数执行基本操作,基本覆盖了 SCF 常用场景所需要的权限。
角色详情
SCF 默认的配置角色为
SCF_QcsRole,其角色详情如下:角色名:
SCF_QcsRole角色载体:
产品服务-scf.qcloud.com角色描述:SCF 默认配置角色。该服务角色用于提供 SCF 配置对接其他云上资源的权限,包括但不限于代码文件访问、触发器配置。配置角色的预设策略可支持函数执行的基本操作。
角色已关联策略:此角色所拥有
QcloudAccessForScfRole 策略,具备以下功能:配置 COS 对象存储触发器时向 Bucket 配置中写入触发配置信息。
读取 COS 对象存储 Bucket 中的触发器配置信息。
在使用 COS 对象存储更新代码时,从 Bucket 完成代码 zip 包的读取操作。
配置 API 网关触发器时,完成 API 网关的服务、API 创建,以及服务发布等操作。
配置和使用日志服务 CLS 的读写访问等操作。
配置和使用消息队列 CMQ 的读写访问等操作。
配置和使用消息队列 Ckafka 的创建、列表等操作。
注意:
服务授权
1. 如果您是首次使用 SCF,打开 Serverless 控制台 时会提示您进行服务授权。如下图所示:
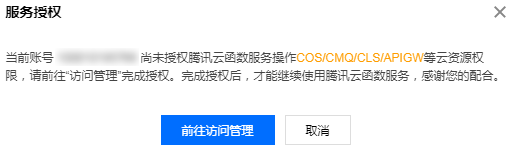
2. 选择前往访问管理进入角色管理页面,单击同意授权确认授权。如下图所示:


3. 确认授权后,将会为您自动创建角色
SCF_QcsRole。可在 角色 中查看。如下图所示:

运行角色
运行角色服务于用户代码,角色载体为
产品服务-scf.qcloud.com。用户为函数添加对应的运行角色后,SCF 在运行角色已关联策略的权限范围内为用户的运行代码申请临时授权,便于代码通过角色的授权机制实现权限打通和其他云上资源访问。
以 SCF_QcsRole 为例,用户也可以选择 SCF_QcsRole 作为函数的运行角色,这意味着将 SCF_QcsRole 关联策略对应的权限授权给 SCF,使 SCF 获得为用户代码申请访问其他云上资源的权利。创建运行角色
1. 登录 Serverless 控制台,单击左侧导航栏的函数服务。
2. 在函数服务列表页面,单击需创建运行角色的函数名,进入函数配置页。
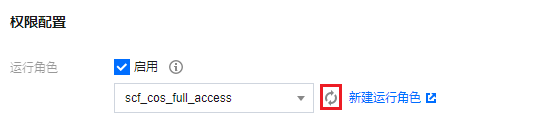
3. 选择函数配置页右上角的编辑,勾选“运行角色”中的启用,并单击新建运行角色。如下图所示:
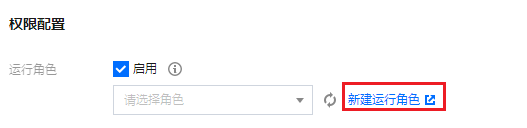
4. 在“输入角色载体信息”步骤中勾选云函数(scf),并单击下一步。
5. 在“配置角色策略”步骤中,选择函数所需策略并单击下一步。如下图所示:
说明:
本文以选择
QcloudCOSFullAccess 对象存储(COS)全读写访问权限为例,请根据实际需求进行选择。

6. 按需配置角色标签后,在“审阅”步骤中填写角色名称,并单击完成。本文以
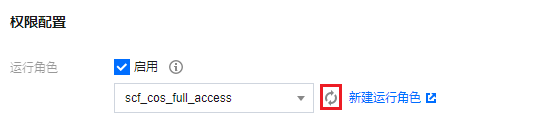
scf_cos_full_access 角色名称为例。 7. 返回函数配置页,单击“运行角色”右侧的

注意:
获取运行角色临时密钥信息
在函数运行时,SCF 服务将会使用选定的运行角色完成临时 SecretId、SecretKey、SessionToken 的申请。
对于非镜像创建的函数:
将以环境变量的形式将相关内容传递到运行环境中。如下图所示:
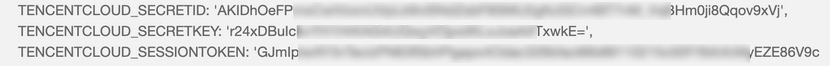
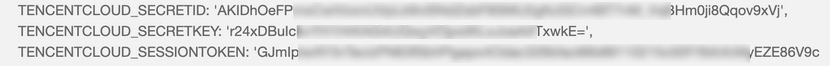
main函数中增加下述代码将临时密钥信息传递到函数运行环境中,并以环境变量的方式获取。def main_handler(event, context);secret_id = os.environ.get('TENCENTCLOUD_SECRETID')secret_key = os.environ.get('TENCENTCLOUD_SECRETKEY')token= os.environ.get('TENCENTCLOUD_SESSIONTOKEN')
对于镜像创建的函数:
将以 http header 的形式将相关内容传递到入参 context 中,具体请参见 镜像函数入参说明。