说明:
本文档为您介绍如何通过 Web 应用防火墙(WAF)设置防护规则和恶意文件检测配置,以防护 Web 攻击。
背景信息
腾讯云 Web 应用防火墙(WAF)使用基于正则的规则防护引擎和基于机器学习的 AI 防护引擎,进行 Web 漏洞和未知威胁防护。
腾讯云 WAF 规则防护引擎,提供基于腾讯安全 Web 威胁和情报积累的专家规则集,自动防护 OWASP TOP10 攻击。目前防护 Web 攻击包括:SQL 注入、XSS 攻击、恶意扫描、命令注入攻击、Web 应用漏洞、WebShell 上传、不合规协议、木马后门等17类通用的 Web 攻击。
WAF 规则防护引擎,支持规则等级划分,用户可根据实际业务需要进行规则防护等级设置,并支持对规则集规则或单条规则进行开关设置,可以对 WAF 预设的规则进行禁用操作,同时提供基于指定域名 URL 和规则 ID 白名单处置策略,进行误报处理。
操作步骤
规则管理
1. 登录 Web 应用防火墙控制台,在左侧导航栏顶部,将控制台切换至实例所在区域(中国大陆/非中国大陆)。
2. 在左侧导航栏中,选择防护策略 > 基础安全。
3. 在基础安全页面,单击 WEB 安全,在“规则引擎”页签内,可基于域名实现对单条规则的开通设置,决定在规则引擎中是否启用该规则,所有规则默认开启。
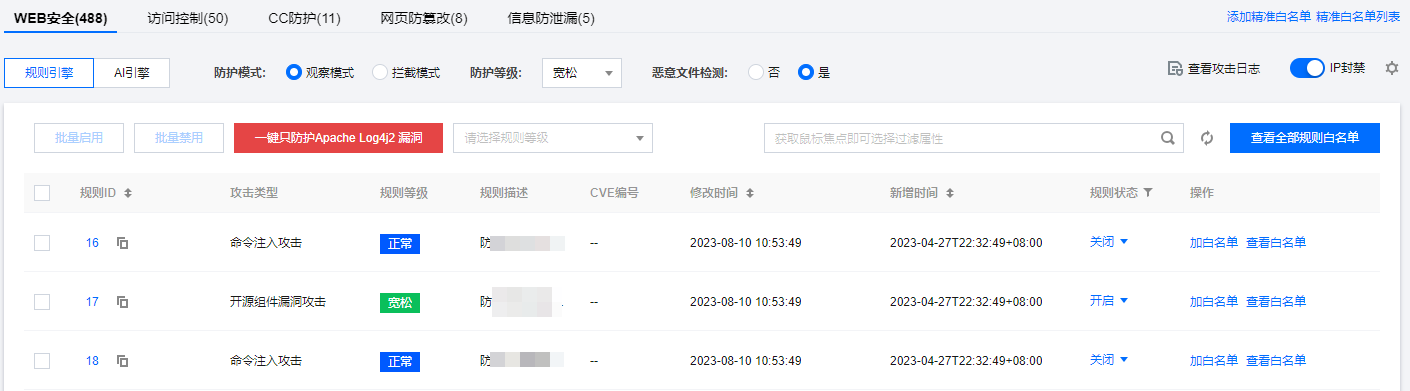
4. 勾选规则并单击规则引擎页面左上角批量启用或批量禁用,支持一键批量启用/禁用规则。

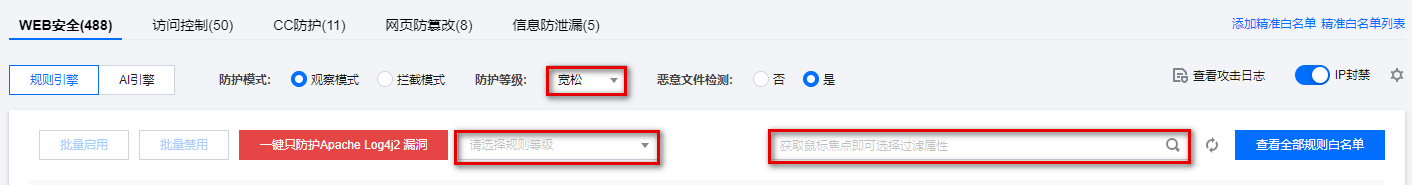
5. 用户可以通过“规则等级”或输入“规则 ID、攻击类型、CVE 编号”搜索规则集,查看特定规则并进行操作。
说明:
超严格规则等级包含所有规则,严格规则等级包含正常和宽松规则,正常规则等级包含宽松规则。
规则白名单或误报处理
1. 登录 Web 应用防火墙控制台,在左侧导航栏顶部,将控制台切换至实例所在区域(中国大陆/非中国大陆)。
2. 在左侧导航栏中,选择防护策略 > 基础安全。
3. 在基础安全页面,单击 WEB 安全,在规则引擎页签内,可以实现基于域名 URL 和规则 ID 的加白名单及误报处理。
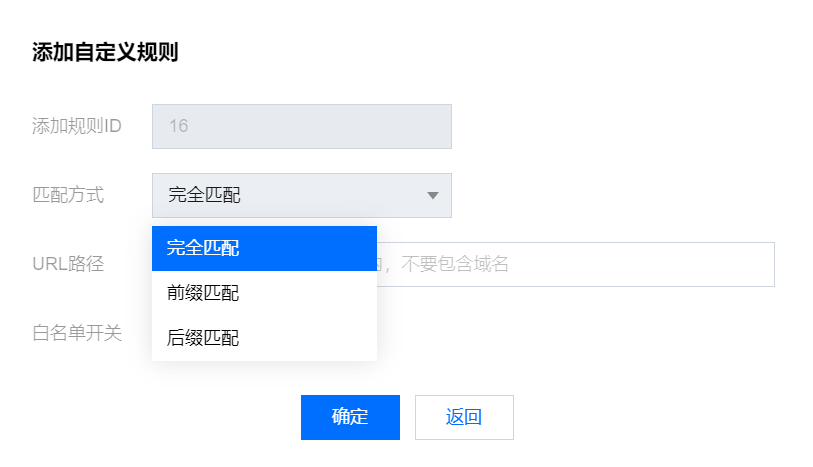
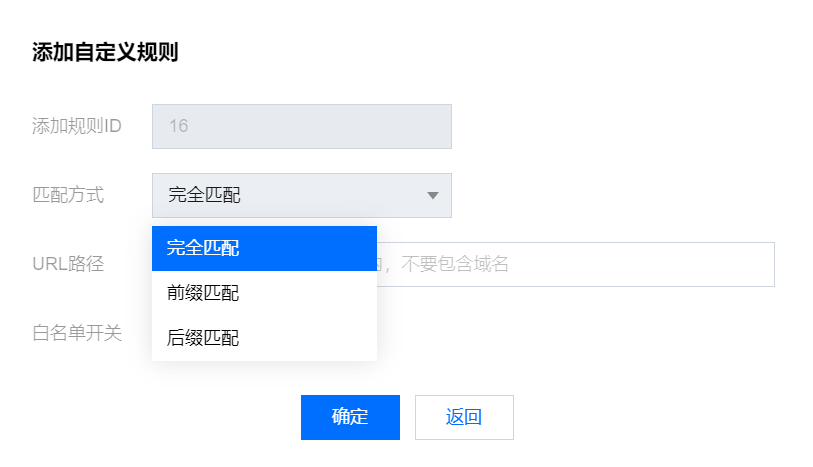
4. 在“规则引擎”页签,选择所需规则,单击加白名单,弹出添加自定义规则弹窗。

5. 在添加自定义规则弹窗中,配置相关参数,单击确定。
字段说明
添加规则 ID:填写需要加白的规则 ID,一条策略可添加1个规则 ID。
匹配方式:加白 URL 路径的匹配方式,支持完全匹配(默认)、前缀匹配和后缀匹配。
URL 路径:需要加白的 URL 路径,同一个域名下 URL 不可重复添加。
白名单开关:白名单策略生效开关,默认为开启。
6. 白名单添加完成后,单击查看白名单,查看该白名单规则,并进行相关操作。


字段说明:
匹配路径:需要加白的 URL 路径,同一个域名下 URL 不可重复添加。
匹配方式:加白 URL 路径的匹配方式,支持完全匹配(默认)、前缀匹配和后缀匹配。
加白规则 ID:所设置的加白规则 ID,可以通过攻击日志或规则管理获取。
开关:白名单策略生效开关。
修改时间:最近一次创建或修改策略的时间。
操作:对策略进行编辑或删除操作。
单击编辑,修改相关参数,单击确认,即可对规则参数进行修改。
单击删除,经过二次确认后,可删除该策略。
查看规则分类
1. 登录 Web 应用防火墙控制台,在左侧导航栏顶部,将控制台切换至实例所在区域(中国大陆/非中国大陆)。
2. 选择服务管理 > 系统设置 > Web 规则库。
3. 在 Web 规则库页面的“防护规则”标签内,可查看当前 WAF 支持防护的攻击分类描述和规则更新动态信息。
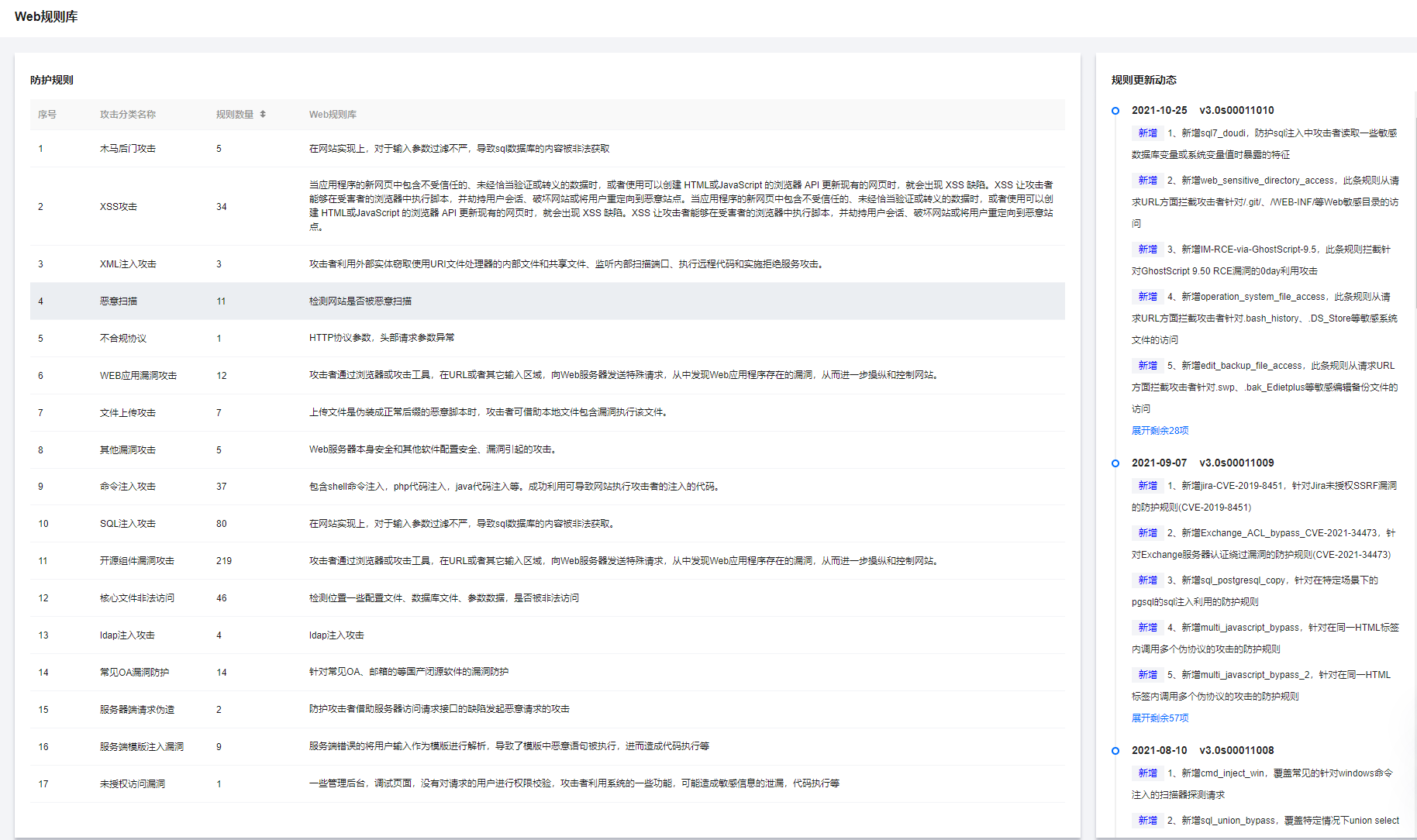
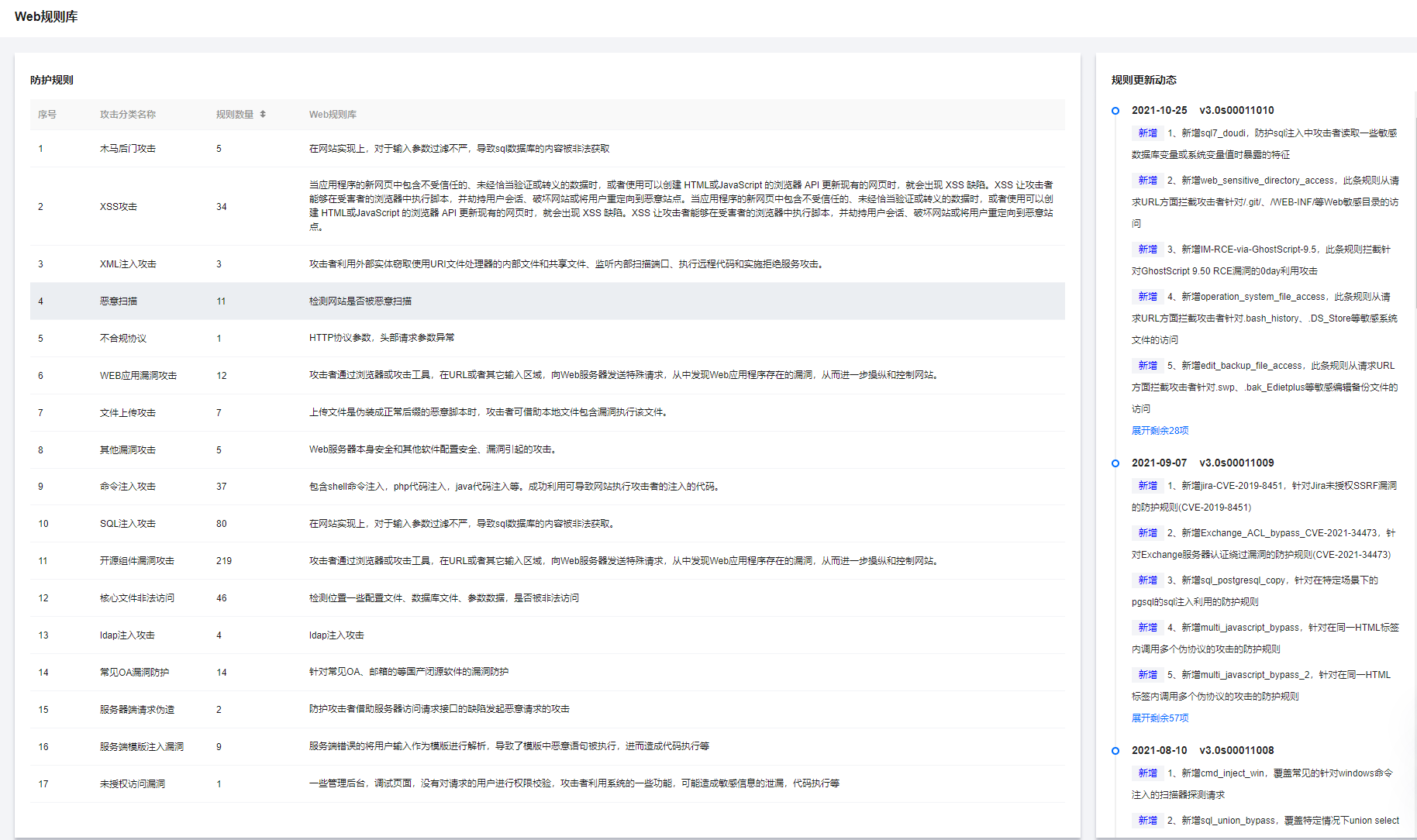
当前 WAF 支持防护的攻击分类如下:
攻击分类 | 攻击描述 |
SQL 注入攻击 | 在网站实现上,对于输入参数过滤不严,导致 SQL 数据库的内容被非法获取。 |
XSS 攻击 | 当应用程序的新网页中包含不受信任的、未经恰当验证或转义的数据,或者使用可以创建 HTML 或 JavaScript 的浏览器 API 更新现有的网页时,会出现 XSS 缺陷。XSS 让攻击者能够在受害者的浏览器中执行脚本,并劫持用户会话、破坏网站或将用户重定向到恶意站点。 |
恶意扫描 | 检测网站是否被恶意扫描。 |
核心文件非法访问 | 防护范围包括但不限于探测可能导致敏感信息泄露的 SVN、Git 敏感文件、数据库文件或其他访问路径的行为。 |
开源组件漏洞攻击 | 常见 Web 开源组件漏洞产生的攻击行为。 |
命令注入攻击 | 注入攻击的一种,包含 Shell 命令注入,PHP 代码注入,Java 代码注入等,若被攻击者成功利用,可导致网站执行攻击者注入的代码。 |
WEB 应用漏洞攻击 | Web 应用程序的安全性(在 Web 服务器上运行的 Java、 ActiveX、PHP、ASP 代码的安全)。 |
XXE 攻击 | 由于 XML 处理器在 XML 文件中存在外部实体引用。攻击者可利用外部实体窃取使用 URI 文件处理器的内部文件和共享文件、监听内部扫描端口、执行远程代码和实施拒绝服务攻击。 |
木马后门攻击 | 检测木马传播过程或木马上传后与控制端通信行为。 |
文件上传攻击 | 当上传文件伪装成正常后缀的恶意脚本时,攻击者可借助本地文件包含漏洞执行该文件。 |
其他漏洞攻击 | 由于Web 服务器本身安全和其他软件配置安全或漏洞引起的攻击。 |
不合规协议 | HTTP 协议参数,头部请求参数异常。 |