ES 集群部署在逻辑隔离的私有网络 VPC 中,我们提供了丰富的能力来切实保证云上资源的安全性,包括
对腾讯云账户下资源的 CAM 访问管理(参见 CAM 访问控制配置)
ES 集群访问密码 / ES 集群用户登录认证
设置 Kibana 和 Cerebro 外网访问 IP 黑白名单,或限制 Kibana 和 Cerebro 仅能通过内网访问
对 ES 集群有限开启外网访问和设置 IP 白名单
开启内网访问 HTTPS 协议
提供的基于角色的访问控制(RBAC)
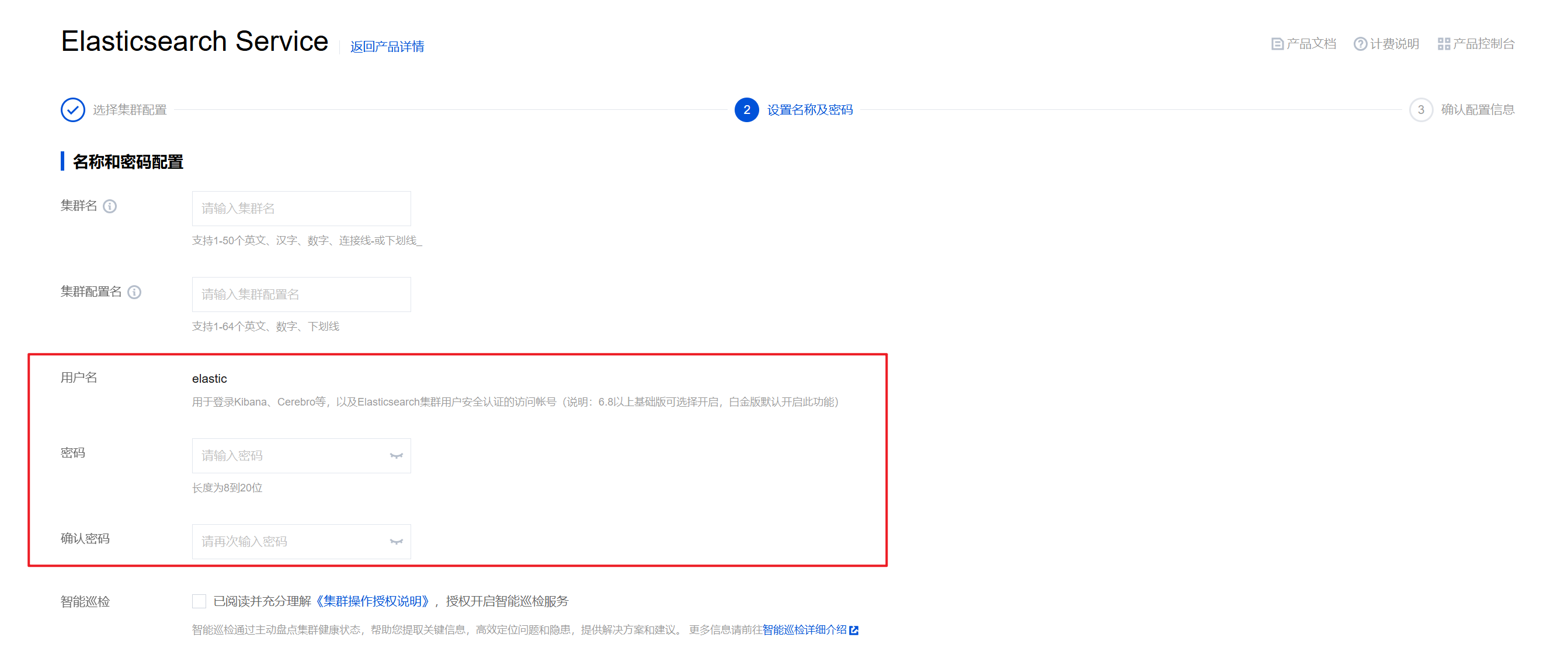
设置 ES 集群访问密码
在创建腾讯云 ES 集群时,会要求用户设置默认用户 elastic 的密码,该账号和密码用于 Kibana 页面登录,若集群已开启 ES 集群用户登录认证,则此用户名和密码还会用于 ES 集群的登录认证,提供进一步的安全防护,详情如下。
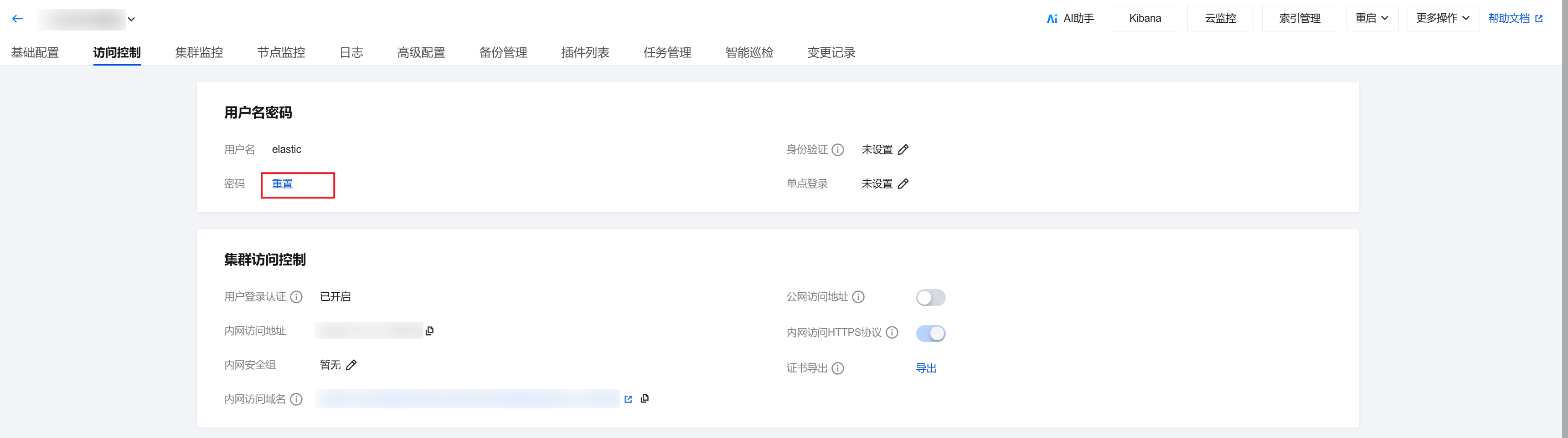
重置 ES 集群访问密码
用户需要调整 ES 集群访问密码时,可以通过集群详情页的密码重置功能对 ES 集群 elastic 账号的密码进行重置,操作页面如下图所示。
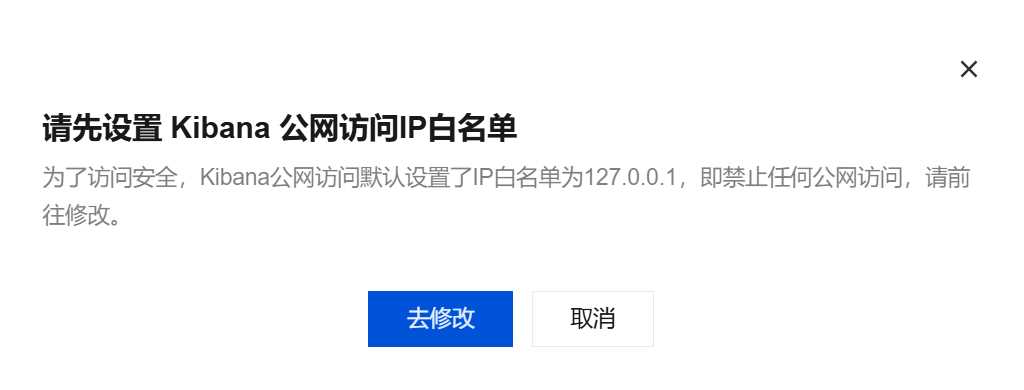
设置可视化组件公网访问 IP 黑白名单
由于 Kibana 和 Cerebro 工具是默认通过公网访问,在进行密码校验的基础上,ES 还为其访问提供了 IP 黑白名单功能,进一步保障用户集群的访问安全性。公网访问白名单默认为127.0.0.1,表示不允许所有 IPv4 和 IPv6 地址访问,此时单击 Kibana 访问入口时,会弹窗引导用户去进行白名单设置,如下图所示。
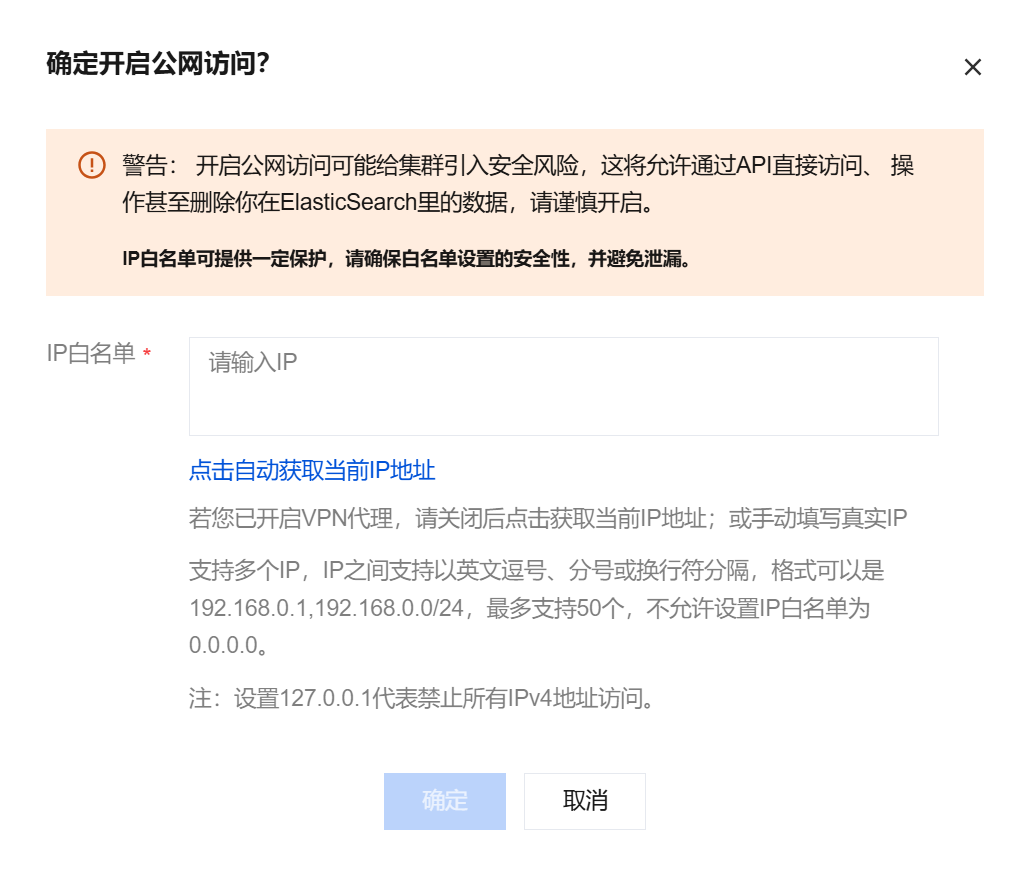
在 ES 集群管理的访问控制中,用户可以在可视化访问控制界面设置公网访问 IP 黑白名单:
配置规则:支持多个 IP,IP 之间以英文逗号分隔,格式为192.168.0.1,192.168.0.0/24,最多支持50个。
黑白名单设置:客户可以设置任意一个,如果黑白名单都配置,以白名单为准。

对 Kibana 进行访问控制
Kibana 默认开启公网访问,如果用户担心公网访问安全性,也可以关闭外网访问,设置仅允许内网访问。

对 Cerebro 进行访问控制
用户可以在可视化访问控制界面开启 Cerebro 工具。点击一键启用后集群运行状态会发生更改,恢复正常状态后即可进行设置。

Cerebro 启用后默认开启公网访问,同时用户也可以选择关闭外网访问,设置仅允许内网访问。

开启 ES 集群公网访问
开启内网访问 HTTPS 协议
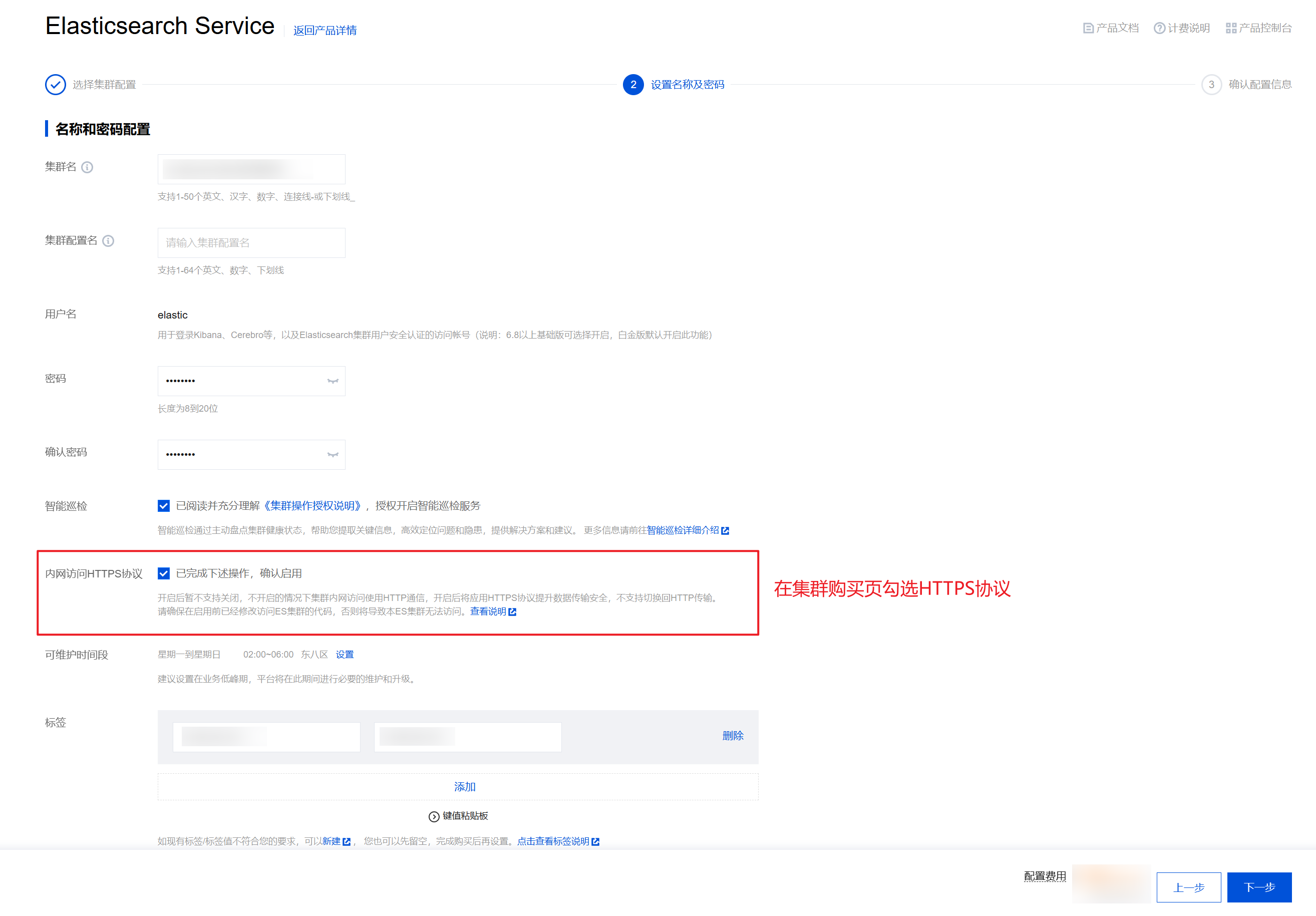
在集群购买页开启 HTTPS 协议。
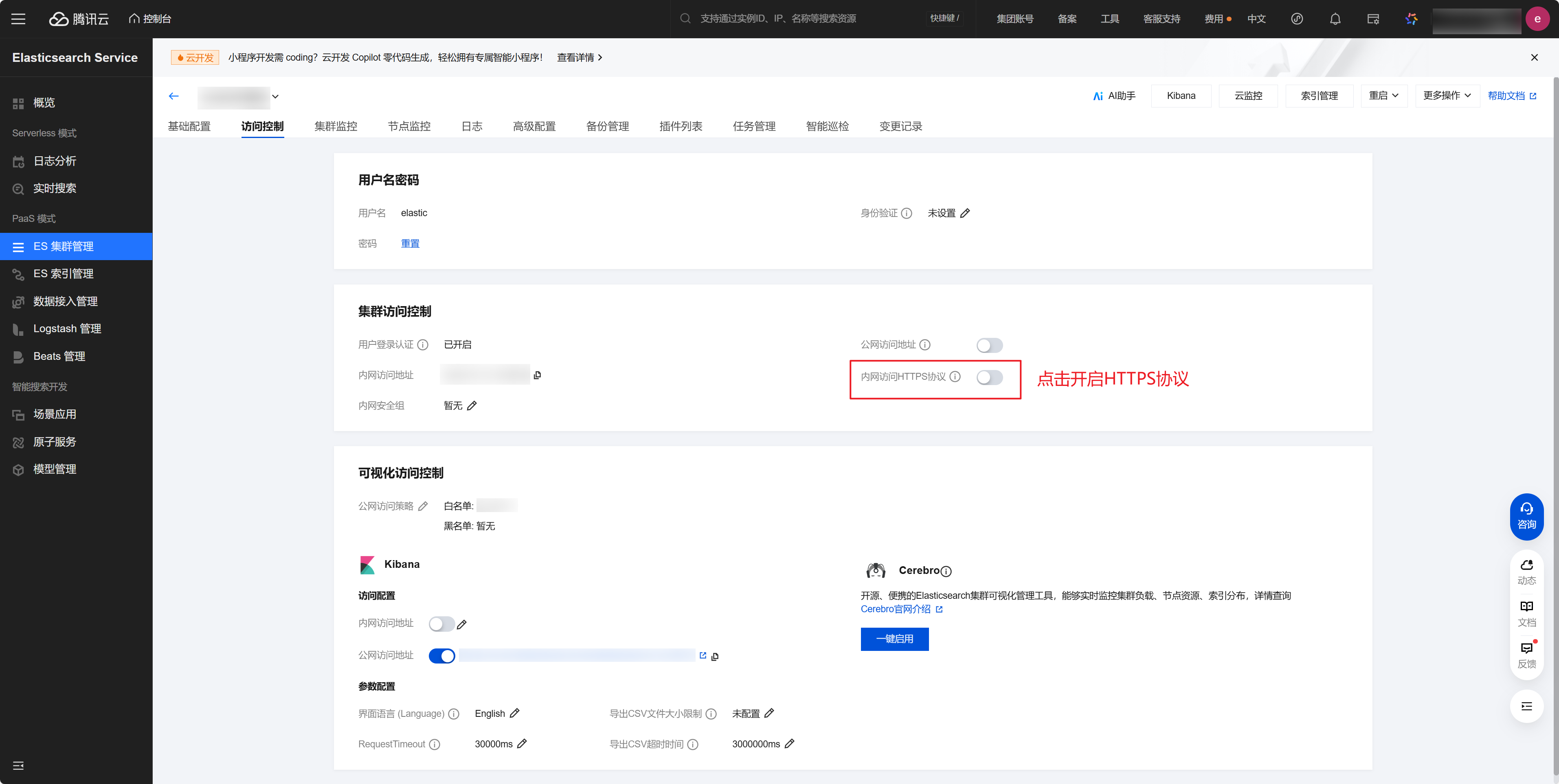
在集群管理界面开启 HTTPS 协议。
基于角色的访问控制(RBAC)
角色管理
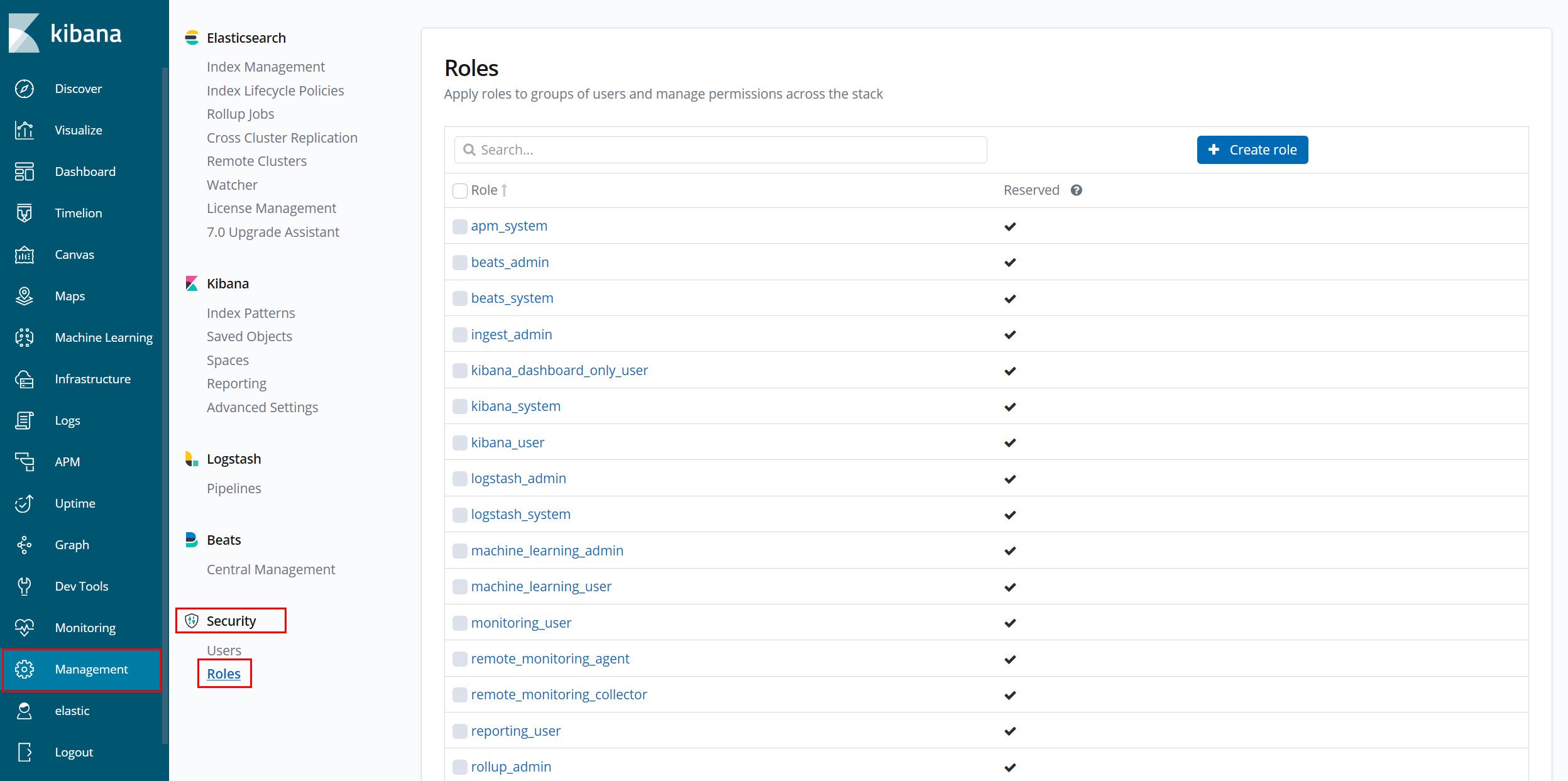
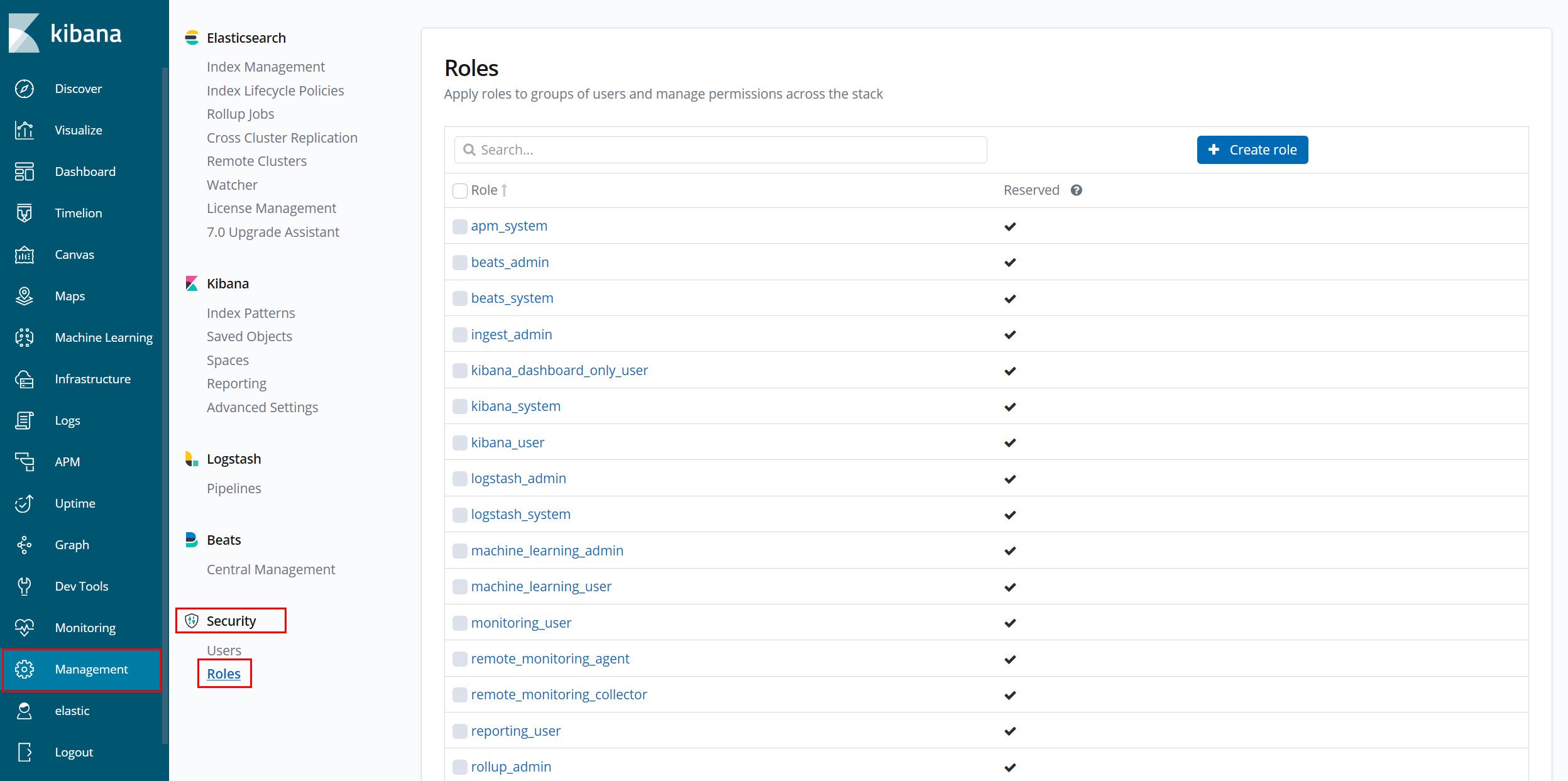
用户可以在 Kibana 的 Management > Security > Roles 中创建、修改和删除具有不同权限组合的角色,详情如下:
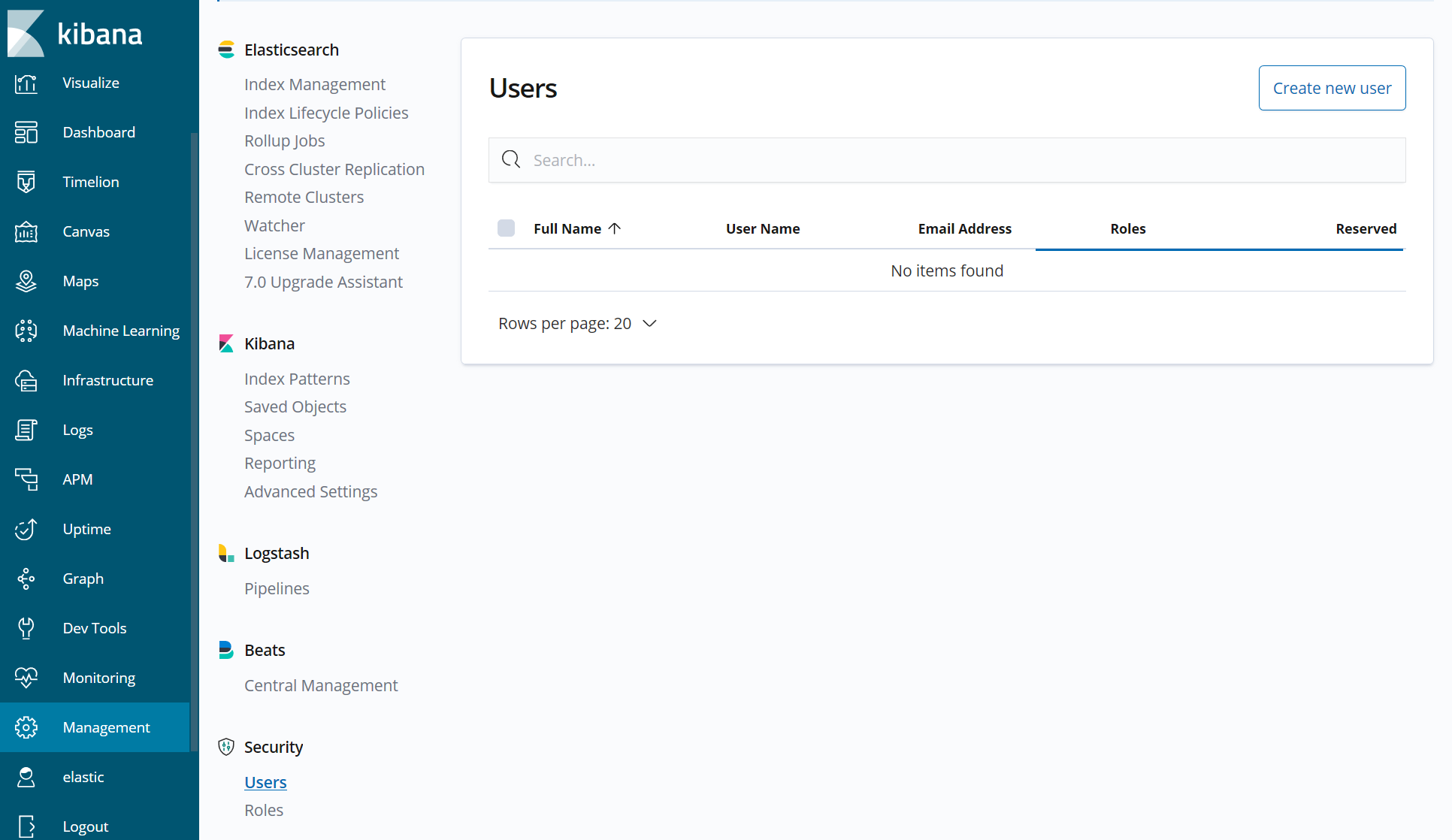
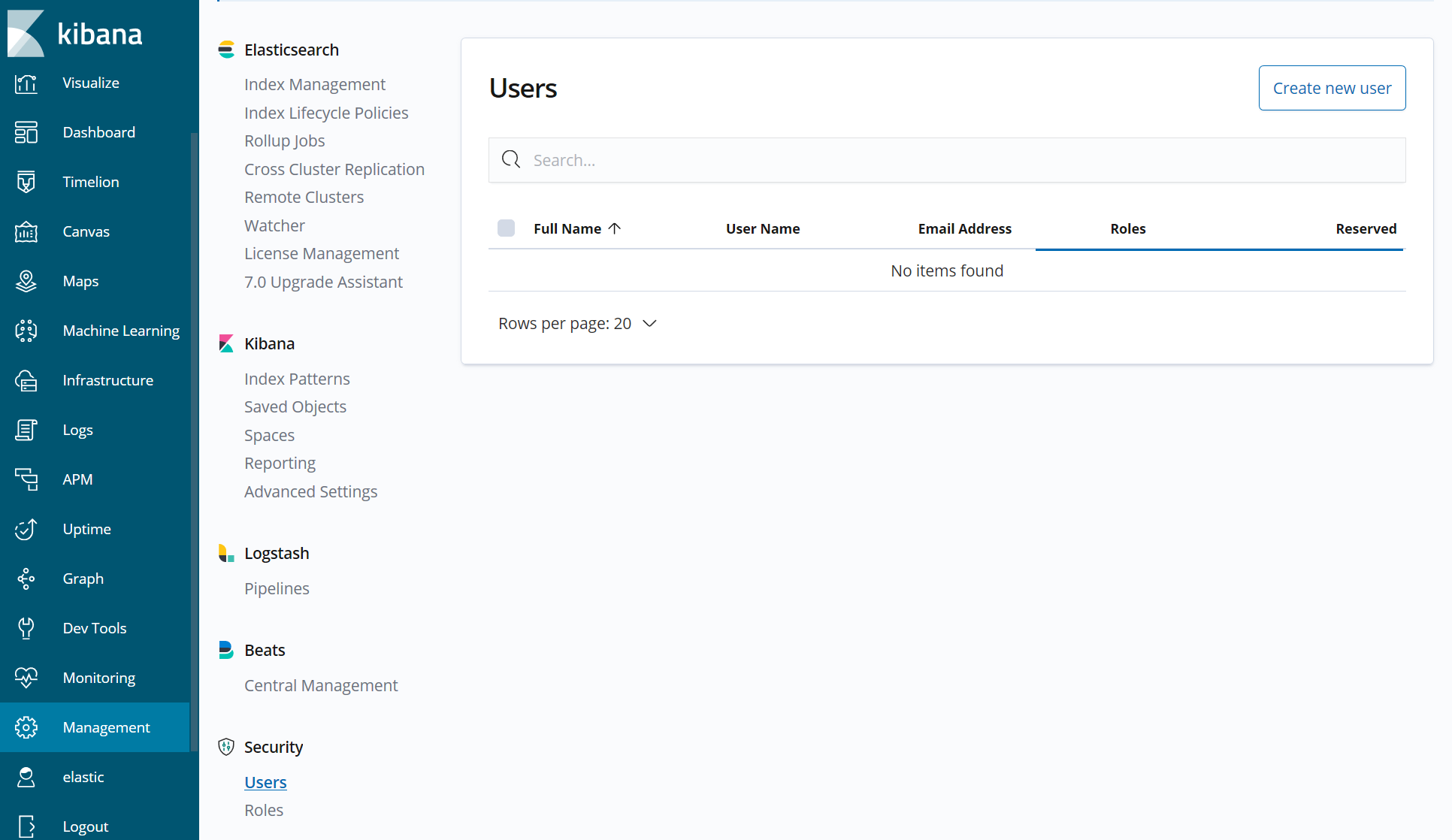
用户管理
用户可以在 Kibana 的 Management > Security > Users 中创建、修改(信息修改、密码修改等)和删除具有多个角色的用户,详情如下:
注意:
ES 内置用户 elastic 的密码只能在官网控制台进行重置。
更多相关安全功能使用可以参考:
关于无法禁用 elastic 用户的说明
Elasticsearch 无法禁用内置的 elastic 超级用户,这是由其安全架构的核心设计决定。elastic 本质是 Elasticsearch 的 “物理层后门账号”。保留它是分布式系统安全模型中的必要妥协——提供可控的恢复出口。
1. 设计意图
为集群提供最后一道恢复通道,如忘记所有管理员密码时可用 elastic 重置。
2. 若允许禁用 elastic,则会导致系统出现如下风险。
2.1 集群启动失败风险
如果安全索引损坏且无其他有效管理员账户,则 Elasticsearch 无法加载安全配置且所有用户均无法访问,最终将导致集群进入死锁状态。
2.2 恢复机制失效
elasticsearch-reset-password 工具依赖 elastic 用户权限重置其他用户密码。若无此账户,密码重置流程将断裂。
3. 内置角色不可修改
superuser 角色在代码中固化,ES 禁止删除或修改其权限。而 elastic 是唯一默认绑定此角色的内置用户。
4. API 层面的限制
删除 elastic 用户的请求会被 ES 明确拒绝,响应示例如下。
{"error": {"root_cause": [{"reason": "user [elastic] is reserved and cannot be modified","type": "validation_exception"}]}}