基本概念
访问管理(Cloud Access Management,CAM)是腾讯云提供的 Web 服务,主要用于帮助客户安全管理腾讯云账户下的资源的访问权限。用户可以通过访问管理创建、管理和销毁用户(组),并使用身份管理和策略管理控制其他用户使用腾讯云资源的权限。
访问授权
授予访问权限,指的是用户可以决定什么人、在何种条件下、对哪些资源、执行具体操作的控制能力组合。因此描述一个访问权限行为,通常包括四个元素:身份、资源、操作、条件(可选)。
访问授权元素说明
腾讯云身份
用户申请腾讯云账号时,系统会创建一个用于登录腾讯云服务的主账号身份。腾讯云主账号可通过用户管理功能对具有不同职责的分类用户进行管理。用户类型包括协作者、消息接收人、子用户和角色等,具体定义可参见 身份管理 和 词汇表。
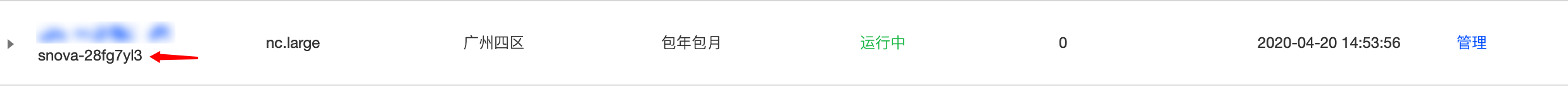
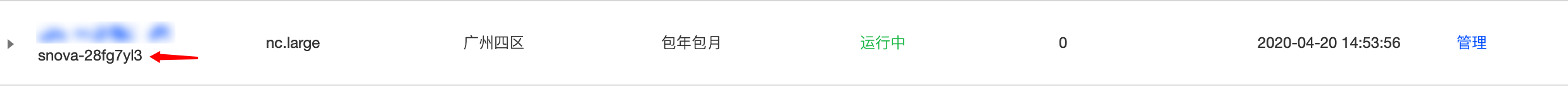
腾讯云数据仓库 TCHouse-P 集群资源
腾讯云数据仓库 TCHouse-P 的资源是指腾讯云数据仓库 TCHouse-P 集群,访问控制也是针对腾讯云数据仓库 TCHouse-P 集群进行控制,通常在控制台我们能看到腾讯云数据仓库 TCHouse-P 的标识,示例如下:
腾讯云数据仓库 TCHouse-P 集群的操作
集群的操作是指用户在腾讯云数据仓库 TCHouse-P 的控制台进行的操作行为,基本上每一个操作行为都可以映射到一个云 API,例如删除集群,或者查看集群详细信息,都拥有一个 action 标识,可以在访问控制时针对 action(读,写)进行访问控制。
最小权限原则
授权时,请务必明确权限范围,需要明确授予指定用户在何种条件下,执行何种操作,访问何种资源的权限。