为应对可能出现的误操作、策略变更需求或紧急故障恢复场景,特提供策略备份与回滚功能,确保您的网络防护策略稳定可靠。
通过策略备份与回滚,可以快速撤销近期的修改,使互联网边界防火墙、NAT 边界防火墙、VPC 边界防火墙、企业安全组的策略配置回到之前保存的状态。
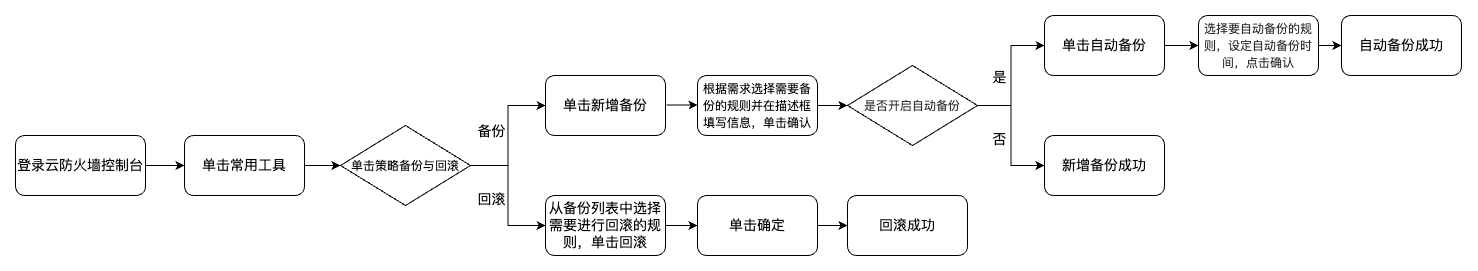
流程图
策略备份
1. 登录 云防火墙控制台,在左侧导航中,单击常用工具。
2. 在常用工具页面,单击策略备份与回滚的前往配置。


3. 在策略备份与回滚页面,单击新增备份。
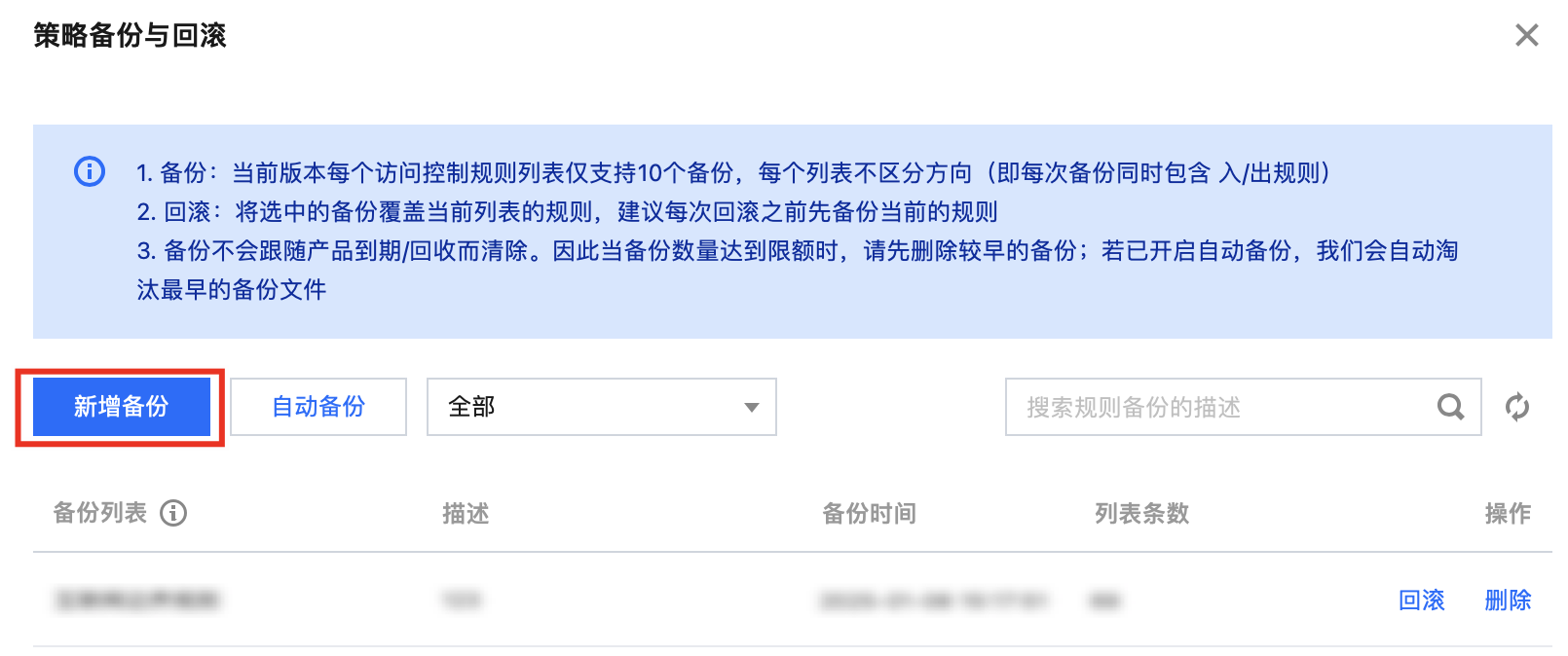
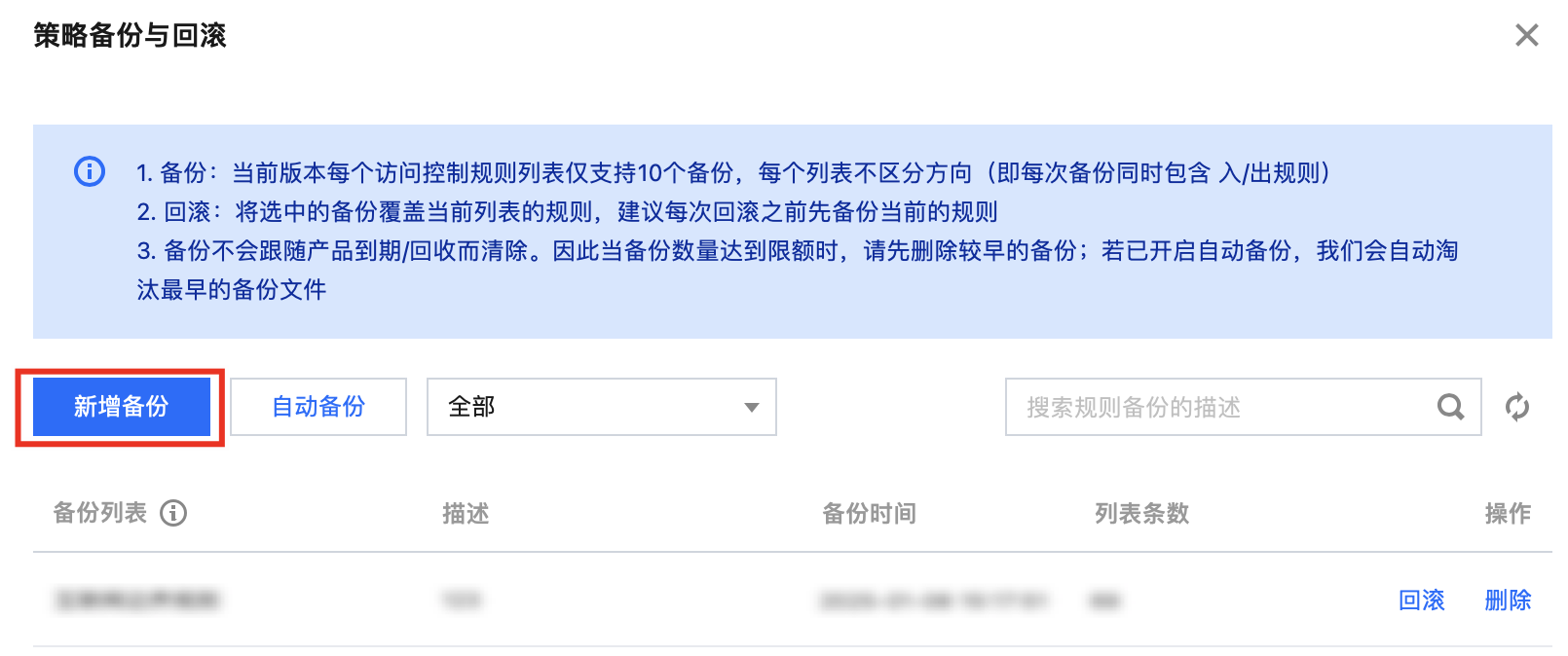
4. 展开备份列表选项框,系统会列出当前可备份的规则列表,您可根据需求选择。同时,为方便后续识别备份用途,请在描述栏填写清晰、简洁的描述信息。


5. 完成上述规则选择与描述信息填写后,单击确定,系统将立即启动备份程序,备份完成后,会有‘备份成功’的提示信息,告知您此次备份已顺利完成并妥善存储。


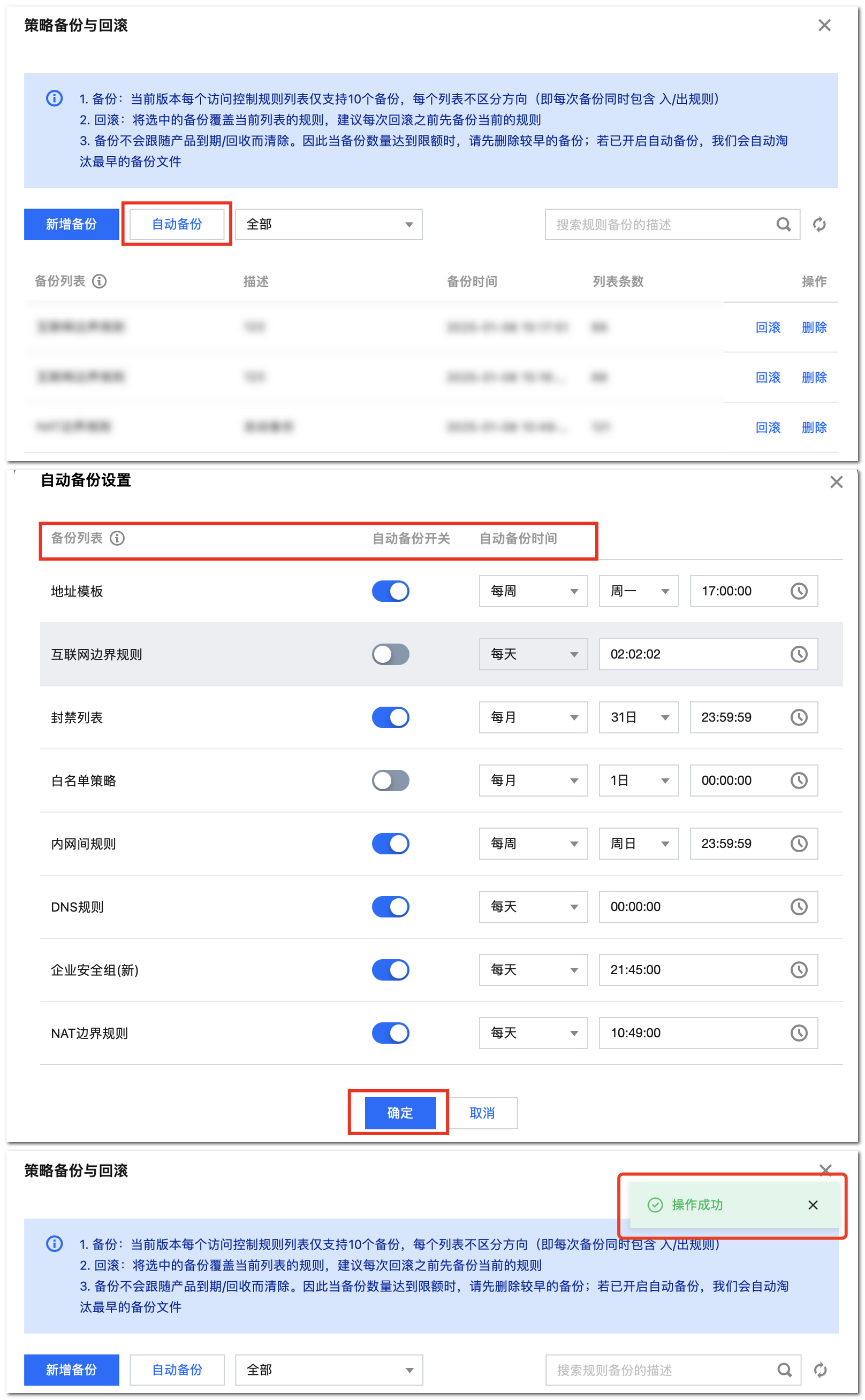
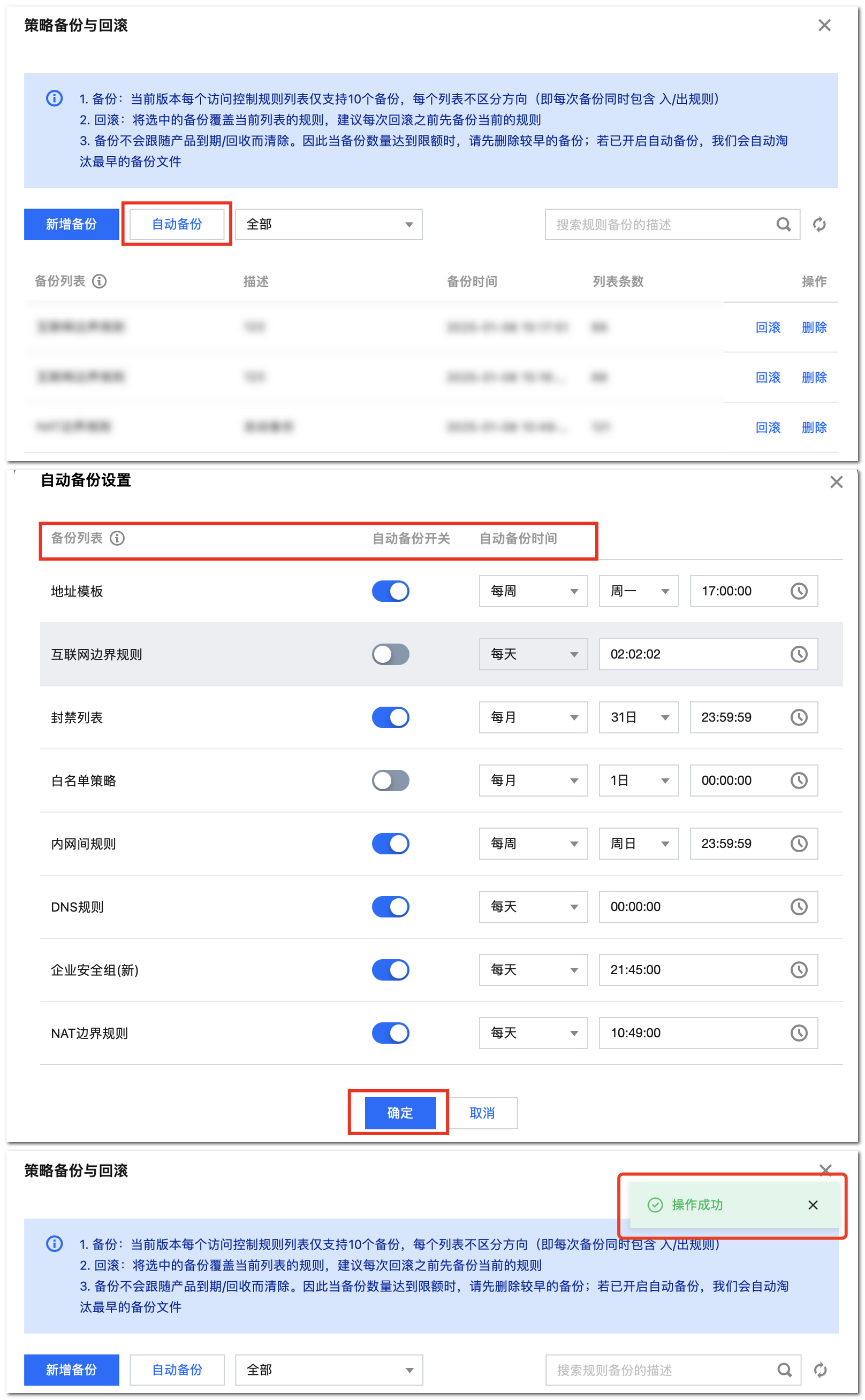
6. 系统还可以按照需求定时自动备份您选定的规则。单击自动备份,系统会列出可备份的规则列表,选择需要开通自动备份配置的规则并为自动备份设定合适的时间,完成规则和时间的选择后,核对信息无误后,单击确定,系统将按照您设定的要求启动自动备份任务。
策略回滚
注意:
1. 登录 云防火墙控制台,在左侧导航中,单击常用工具。
2. 在常用工具页面,单击策略备份与回滚的前往配置。


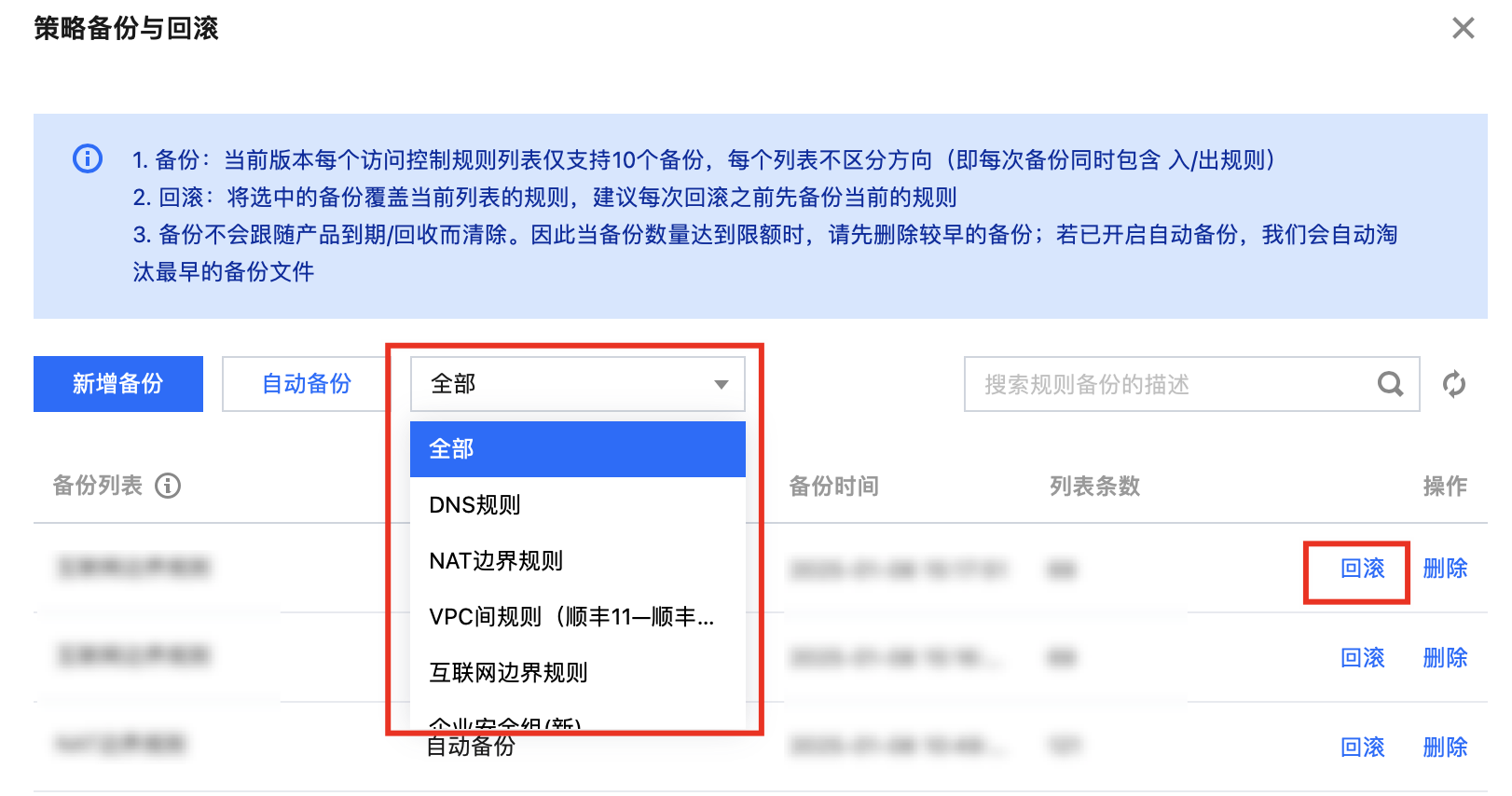
3. 在策略备份与回滚页面,弹窗里包括已备份的所有规则资源、描述和备份时间。
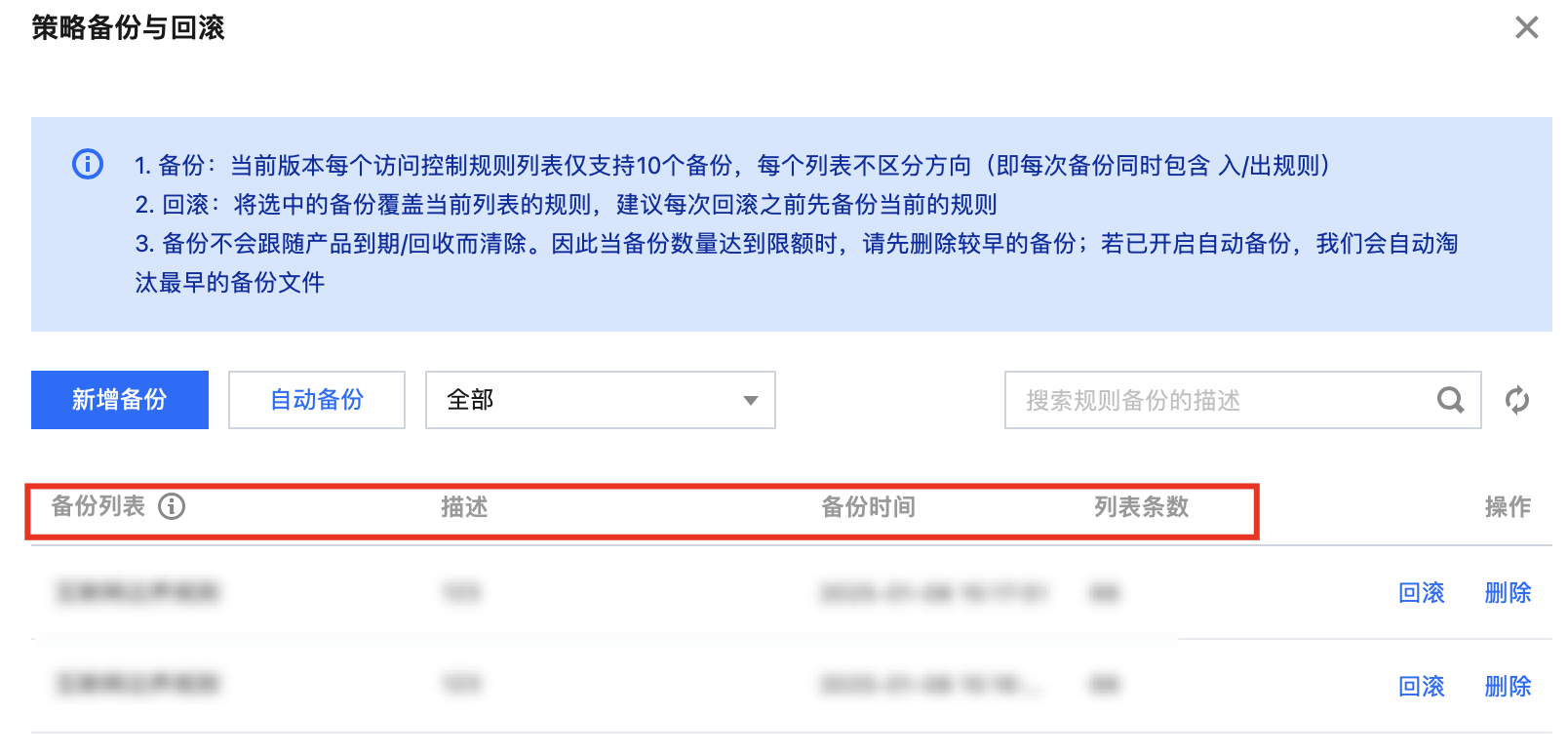
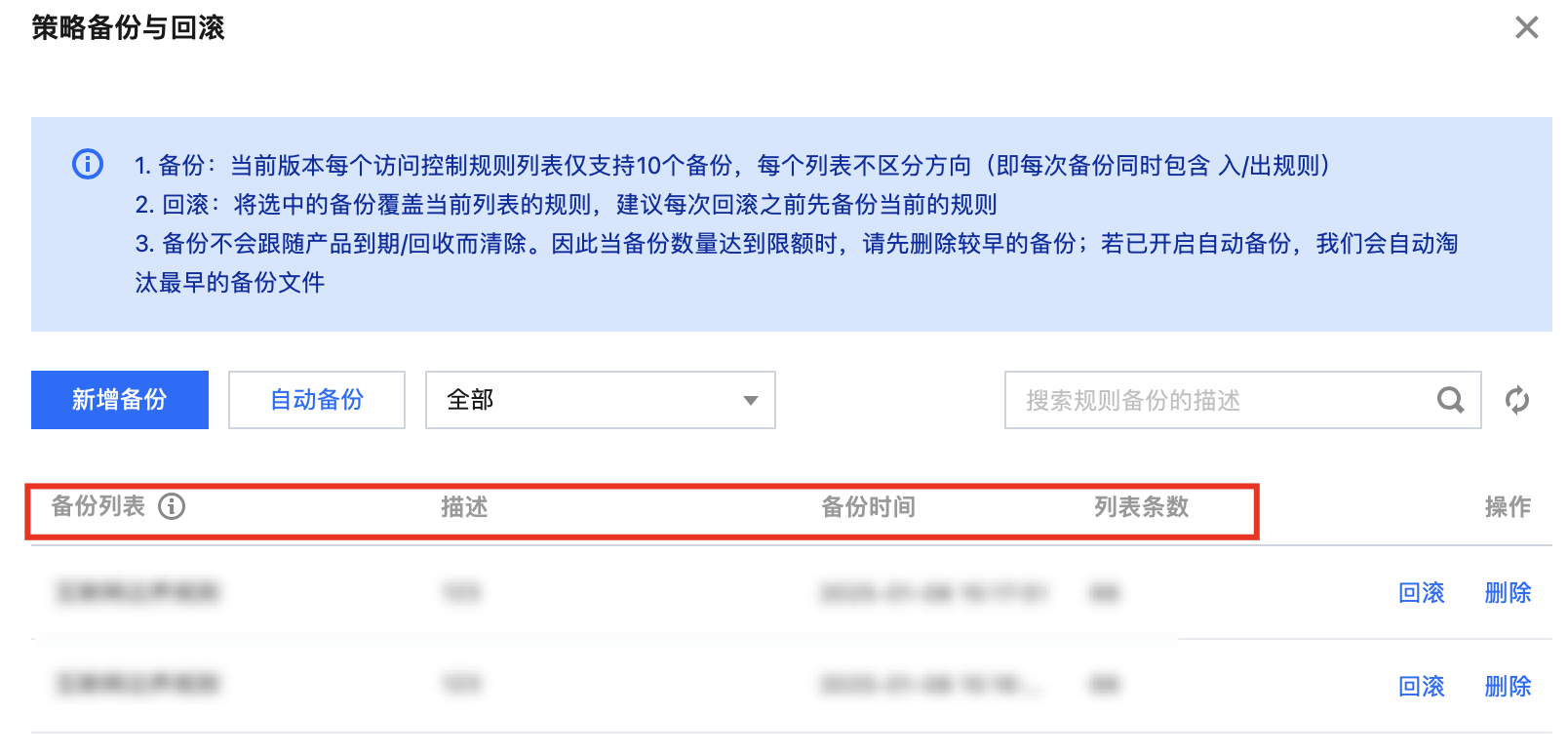
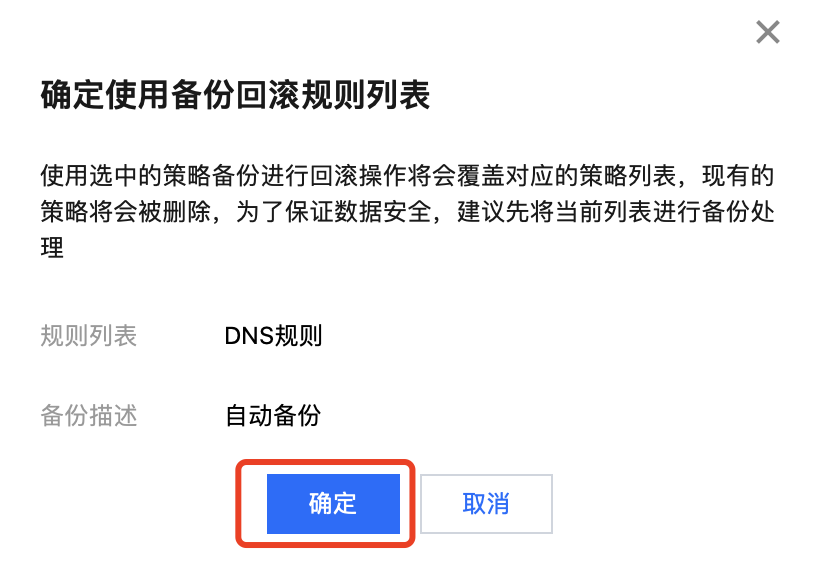
4. 下拉选项框找到需要进行回滚的规则,单击回滚。
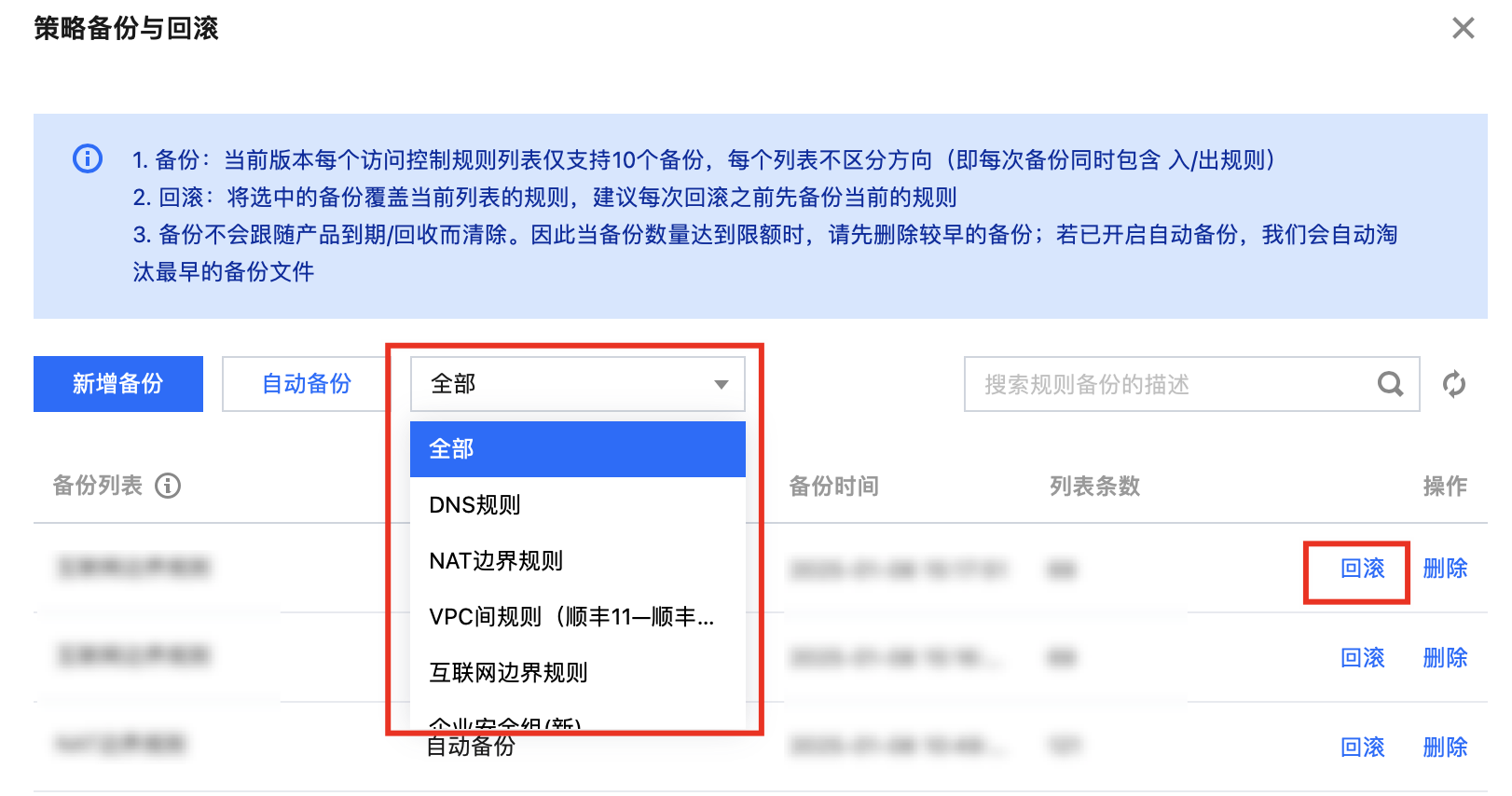
5. 单击确定,系统立即开始将备份的规则覆盖当前规则列表。
使用场景
场景类型 | 策略详情 | |
策略备份 | 定期备份 | 按固定周期备份防火墙策略,有助于留存网络防护策略各阶段状态。后续回溯策略演变、合规审计,或对比不同阶段策略优劣时,能快速获取资料依据。例如:企业每季度内部网络安全审查,依靠定期备份可清晰展现季度间防火墙策略调整走向与重点。 |
| 重大业务变更前 | 企业上线新业务系统、拓展网络区域、大规模调整服务器架构前,务必进行策略备份。新策略实施若出现影响原有业务访问、引发网络延迟、暴露安全漏洞等问题,可迅速还原备份策略,避免业务长时间中断受损。例如:电商企业在 “双 11” 购物狂欢节前,对服务器进行扩容并调整防火墙策略,若提前备份,即使新策略出现意外,也能快速回滚,保障购物节期间网络交易的顺畅。 |
| 人员交接场景 | 在网络安全管理团队成员更替时,提前备份好策略,能够减少因人员变动带来的工作延误与风险。同时,备份策略也可作为新成员后续策略调整的参考基准,确保策略修改的连贯性与合理性。 |
策略回滚 | 误操作后 | 由于操作失误,如误删重要规则、错误配置访问权限,导致部分业务无法正常访问或出现安全隐患时,策略回滚功能可立即将策略恢复到误操作前的正确状态,保障业务正常运行。例如:管理员清理过期规则误删在用关键业务访问规则,回滚前一天备份策略就能快速修复。 |
| 策略调整测试失败后 | 企业因业务发展或应对新安全威胁调整优化防火墙策略,测试中若出现与现有网络架构不兼容、无法阻挡新型攻击、影响业务性能等状况,利用回滚功能还原到调整前稳定状态,重新评估测试方案,规避失败调整带来的损失。例如:金融企业测试新入侵检测策略后发现误报率高影响效率,回滚原策略再深入研究改进。 |
| 遭受网络攻击或故障后 | 企业网络遇恶意攻击致防火墙策略被篡改,或因系统故障(如硬盘损坏、软件崩溃)造成策略文件丢失、损坏,回滚功能可助企业迅速恢复到此前可靠策略配置,降低损失,为排查修复争取时间。例如:企业深夜遭 DDoS 攻击,策略被恶意修改,回滚前一天备份策略快速恢复防护,同时技术人员紧急响应查源修复。 |