通过存储桶策略(Policy)授权案例
准备工作
1. 创建存储桶
通过存储桶策略(Policy)授权仅针对特定的存储桶,因此您需要先 创建存储桶。如需针对账号维度进行授权,请参见本文的 通过访问管理(CAM)授权案例。
2. 准备被授权账号的 UIN
本文假设拥有目标存储桶的主账号 UIN 为100000000001,其下的子账号为100000000011,子账号需要被授权才能访问目标存储桶。
3. 打开添加策略对话框
进入目标存储桶的权限管理,选择 Policy 权限设置 > 图形设置,并单击打开添加策略对话框,随后请参见本文的授权案例进行配置。添加策略的详细操作指引,可参见 添加存储桶策略 文档。
以下列举了几种不同的授权案例,您可按照实际情况进行配置。
授权案例
案例一:授予子账号拥有特定目录的所有权限
配置信息如下:
配置项 | 配置值 |
效力 | 允许 |
用户 | 选择子账号,然后输入子账号的 UIN,该子账号必须为当前主账号下的子账号 |
资源 | 选择指定资源路径,例如 folder/sub-folder/* |
操作 | 选择所有操作 |


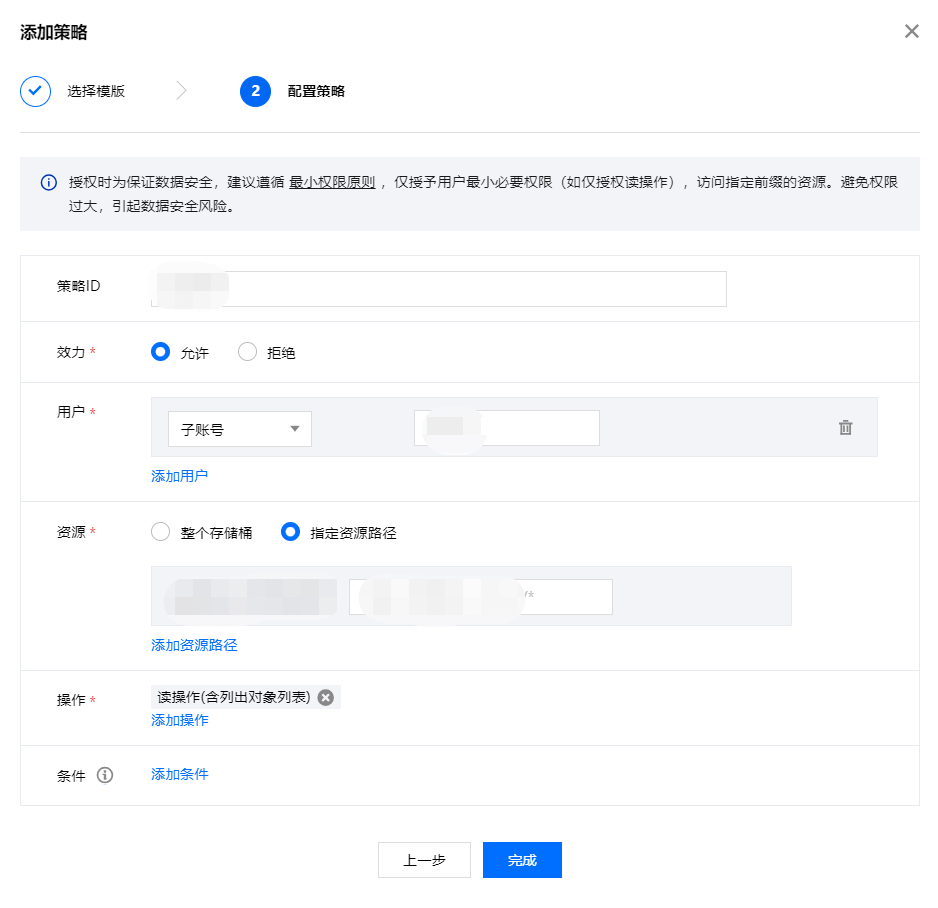
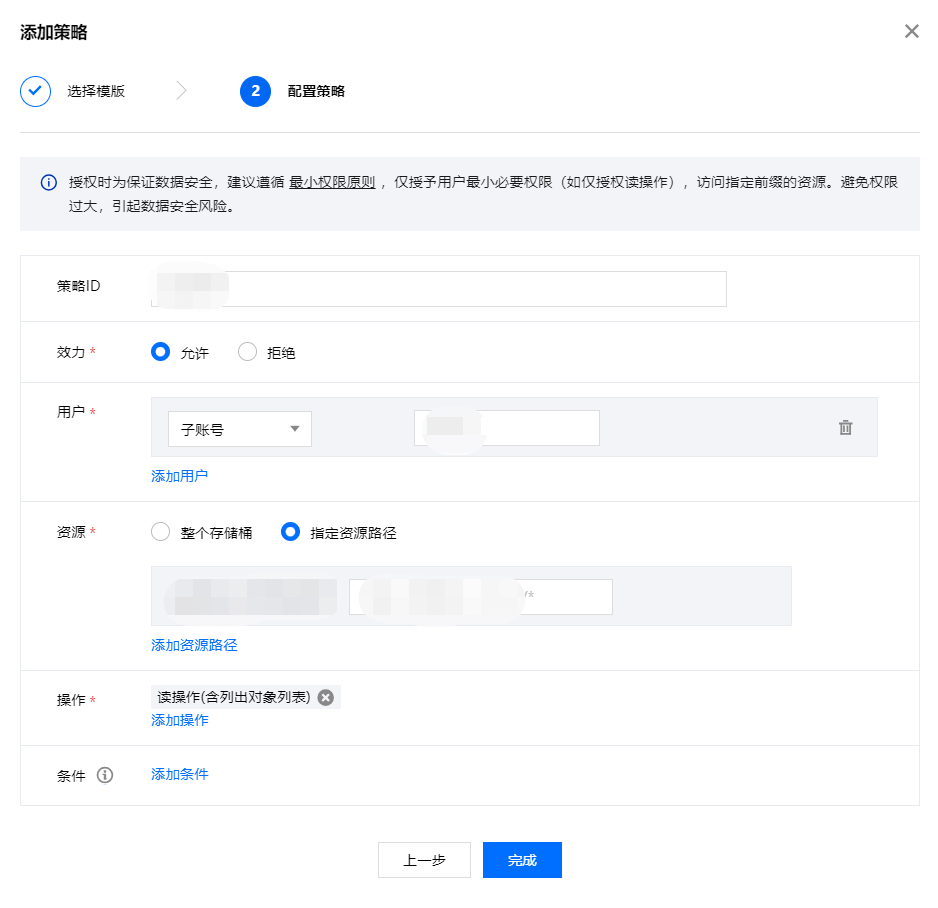
案例二:授予子账号拥有特定目录内所有文件的读权限
配置信息如下:
配置项 | 配置值 |
效力 | 允许 |
用户 | 选择子账号,然后输入子账号的 UIN,该子账号必须为当前主账号下的子账号 |
资源 | 选择指定资源路径,例如 folder/sub-folder/* |
操作 | 读操作(含列出对象列表) |
案例三:授予子账号拥有特定文件的读写权限
配置信息如下:
配置项 | 配置值 |
效力 | 允许 |
用户 | 选择子账号,然后输入子账号的 UIN,该子账号必须为当前主账号下的子账号 |
资源 | 选择指定对象键,例如 folder/sub-folder/example.jpg |
操作 | 所有操作 |


案例四:授予子账号拥有特定目录下所有文件的读写权限,并禁止拥有该目录下指定文件的读写权限
针对此案例,我们需要添加两个策略:允许策略和禁止策略。
1. 首先添加允许策略,配置信息如下:
配置项 | 配置值 |
效力 | 允许 |
用户 | 选择子账号,然后输入子账号的 UIN,该子账号必须为当前主账号下的子账号 |
资源 | 指定目录前缀,例如 folder/sub-folder/* |
操作 | 所有操作 |


2. 随后添加禁止策略,配置信息如下:
配置项 | 配置值 |
效力 | 拒绝 |
用户 | 选择子账号,然后输入子账号的 UIN,该子账号必须为当前主账号下的子账号 |
资源 | 指定需要禁止被访问的对象键,例如 folder/sub-folder/privateobject |
操作 | 所有操作 |


案例五:授权子账号对指定前缀的文件的读写权限
配置信息如下:
配置项 | 配置值 |
效力 | 允许 |
用户 | 选择子账号,然后输入子账号的 UIN,该子账号必须为当前主账号下的子账号 |
资源 | 指定前缀,例如 folder/sub-folder/prefix |
操作 | 所有操作 |


通过访问管理(CAM)授权案例
用户如需针对账号维度进行授权,请参见以下文档进行配置: