如果您在 VPC 中部署的云服务需要共享给其他地域下的 VPC 访问,您可以使用私有连接和云联网服务。
背景信息
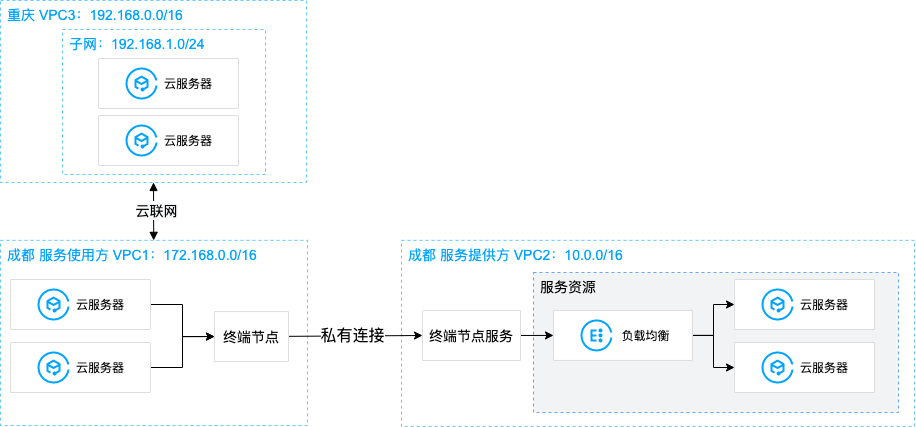
VPC 是您独有的云上私有网络,不同 VPC 之间默认完全隔离。您可以通过私有连接(Private Link)服务,实现腾讯云 VPC 与同地域其他 VPC 上安全稳定的访问连接,简化网络架构,避免公网访问服务带来的潜在安全风险。如果您需要跨地域提供VPC服务共享,那么可以结合云联网打通跨地域 VPC 通信,然后再通过私有连接服务使用方 VPC 的终端节点实现对服务提供方 VPC 中服务的访问。
使用私有连接 Private Link,您需要创建终端节点服务和终端节点。在创建终端节点服务之前,您需要创建一个内网负载均衡实例,并创建监听器关联已经部署业务的云服务器实例,之后在创建终端节点服务时关联该负载均衡实例,此时终端节点服务将作为服务提供方的业务访问入口,供服务使用方创建的终端节点来申请连接,连接建立成功后,服务使用方即可访问服务提供方部署的业务服务。
场景示例
本文以下图业务场景为例。某公司业务部署在成都地域 VPC2 中,现需要将该业务共享给同地域下其他 VPC1 网络及重庆地域下的 VPC3 网络中的客户端访问,为避免公网访问带来的潜在安全风险,使用腾讯云私有连接以及云联网来实现该通信方案。
说明:
本文假设三个 VPC 为同账号下 VPC。
前提条件
已创建服务提供方 VPC2 和服务使用方 VPC1,以及跨地域服务使用方 VPC3。
在服务提供方 VPC2 中已创建内网 CLB 实例,并在 CLB 后端云服务器实例中部署相关服务资源,请确保后端云服务器实例可以正常处理负载均衡转发的请求,具体请参见 负载均衡快速入门。
操作步骤
步骤1:服务提供方创建终端节点服务
1. 登录 私有网络控制台。
2. 在左侧导航栏单击私有连接 > 终端节点服务。
3. 单击新建,在弹出的新建终端节点服务界面,配置相关参数。


参数名称 | 描述 |
服务名称 | 自定义终端节点服务的名称。 |
所在地域 | 终端节点服务所在地域。 |
所属网络 | 选择所属 VPC,本例选择 VPC2。 |
服务类型 | 终端节点服务的类型,目前支持应用型内网 CLB、MySQL、Redis 和 GWLB。 |
后端实例 | 选择 VPC 下已创建的对应类型实例。 |
自动接受 | 指定终端节点服务是、否自动接受终端节点发起的连接请求,本例选择是: 当选择是,自动接受时,终端节点服务默认接受所有连接的终端节点的请求,终端节点创建成功后,状态即为可用。 当选择否,不接受自动连接时,终端节点连接状态将为待接受,需要终端节点服务手动执行接受连接才能将状态从待接受变为可用。 |
4. 完成参数设置后,单击确定完成终端节点服务的创建。
步骤2:服务使用方创建终端节点
注意:
本例为同账号 VPC 间访问,故无需在终端节点服务中添加服务使用方的白名单账号;如果是跨账号 VPC 间访问,则需要服务使用方提前将 UIN 账号告知服务提供方,由服务提供方的终端节点服务先添加白名单,再执行本步骤,详情请参见 跨账号 VPC 间服务共享。
1. 在左侧导航栏单击私有连接 > 终端节点。
2. 单击新建,在弹出的新建终端节点界面,配置相关参数。
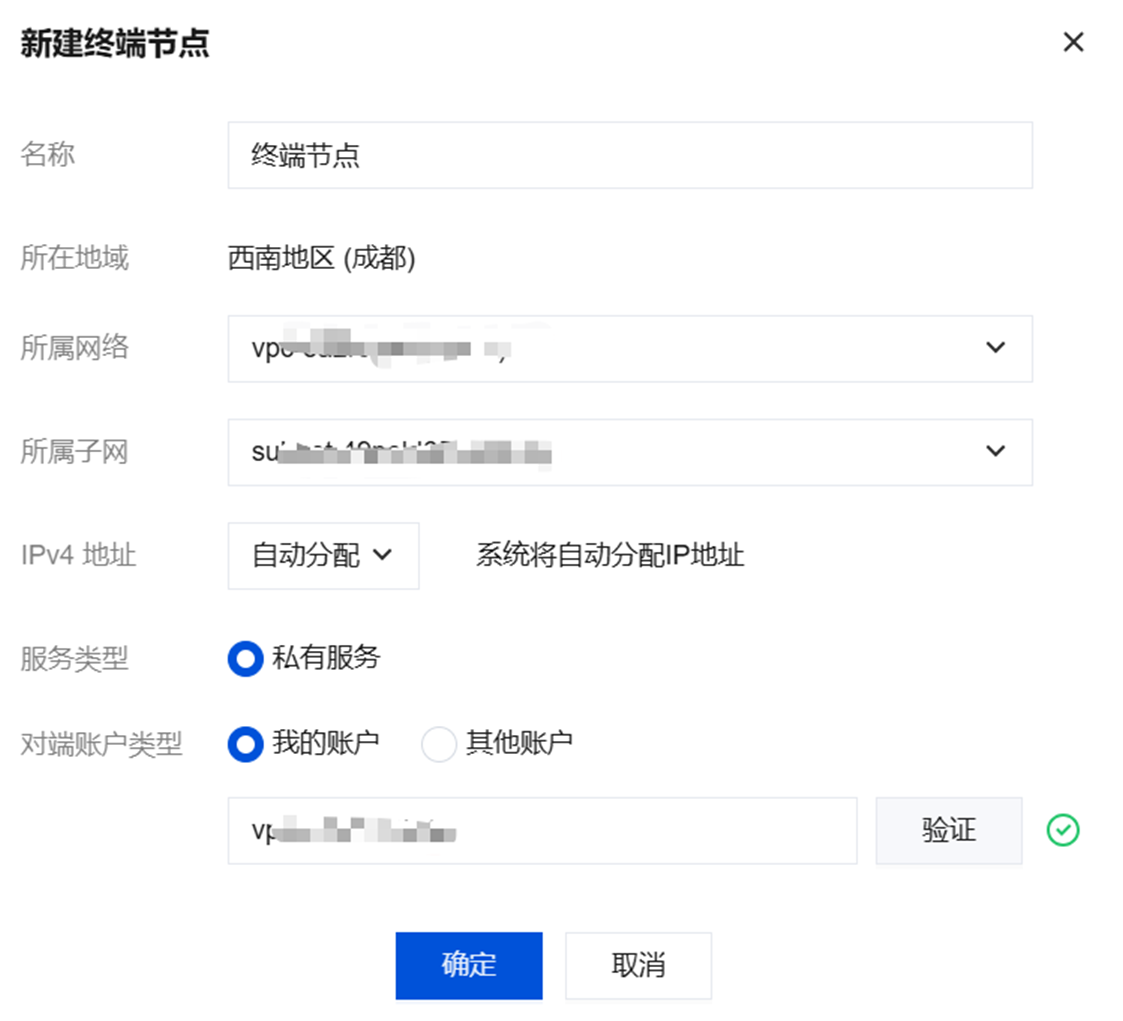
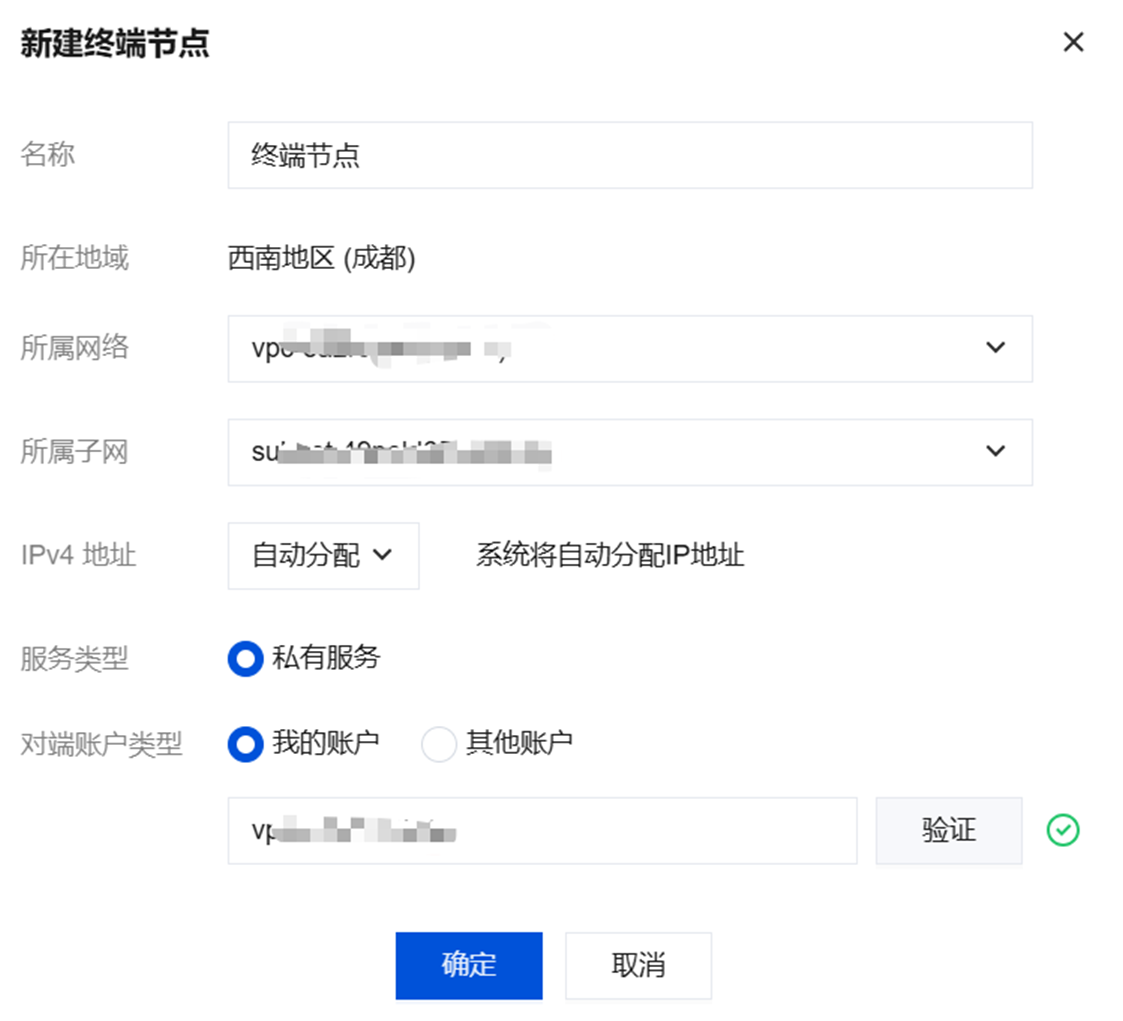
参数名称 | 描述 |
名称 | 自定义终端节点的名称。 |
所在地域 | 终端节点所在地域。 |
所属网络 | 选择终端节点所在的 VPC,本例选择 VPC1。 |
所属子网 | 选择终端节点所在的子网。 |
IP 地址 | 终端节点的 IP 地址。可以指定 IP 地址,IP 地址为 VPC1 内的内网 IP,也可以选择自动分配 IP。 |
服务类型 | 默认私有服务。 |
对端账户类型 | 选择待连接的终端节点服务所属账户,本例选择我的账户: 同账号VPC间访问,选择我的账户。 跨账号VPC间访问,选择其他账户。 说明: 系统会自动校验主账号 UIN 是否有效。如果校验不通过,您需要确认输入的 UIN 是否正确,或确认该 UIN 对应的腾讯云账户是否存在。 输入终端节点服务的 ID 后单击验证,只有验证通过的服务才可建立连接。 |
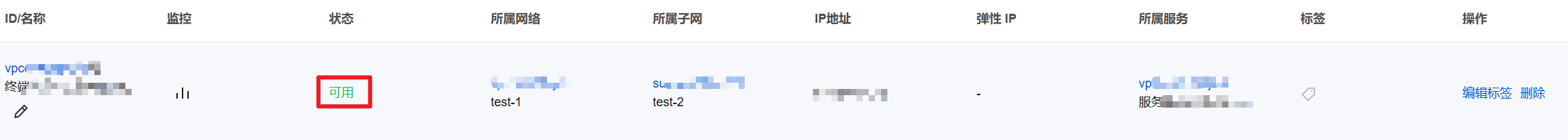
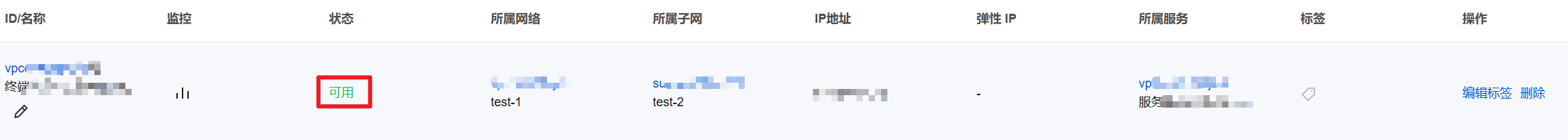
3. 完成参数配置后,单击确定,由于本例 步骤1 中终端节点服务设置的是自动接受连接,即终端节点服务默认接受所有连接的终端节点的连接请求,故终端节点创建成功后,状态即为可用。
步骤3:创建云联网打通 VPC3 和 VPC1 网络
1. 登录 云联网控制台。
2. 单击新建创建云联网实例,关联跨地域 VPC1 和 VPC3,单击确定,即可实现 VPC1 和 VPC3 的互联。


说明:
步骤4:服务使用方发起访问请求进行连接验证
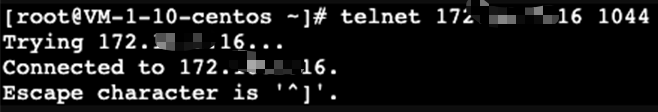
验证成都地域服务使用方 VPC1 访问 VPC2:
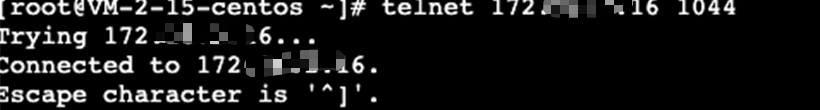
a. 登录服务使用方 VPC1 下的某台 CVM,通过 VIP + VPORT 访问服务提供方的后端服务。
b. 本例使用 telnet 验证连通性,执行 telnet VIP VPORT。
说明:
如果服务器没有安装 telnet,请先执行
yum install telnet 安装 telnet。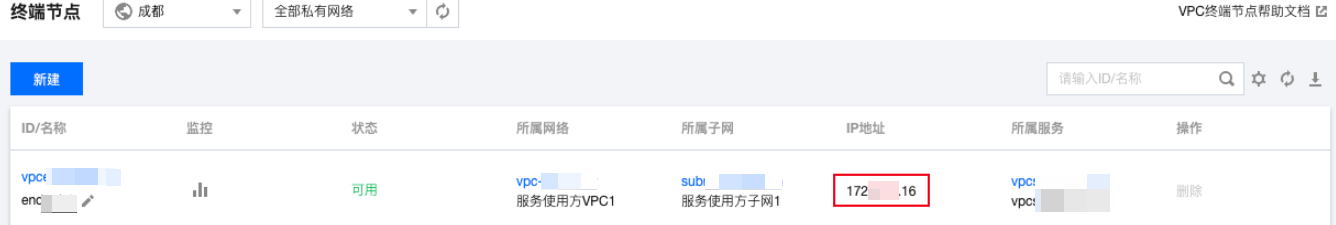
可在对应内网 CLB 监听器页面获取 CLB 的 VPORT。

返回如下信息,表示访问成功:
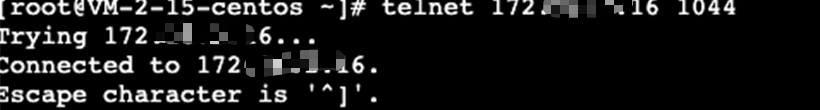
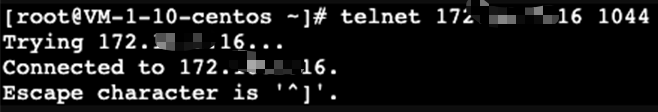
验证重庆地域下 VPC3 通过成都地域服务使用方 VPC1 中的终端节点访问服务提供方 VPC2:
a. 登录 VPC3 下的某台 CVM,通过 VIP + VPORT 访问服务提供方的后端服务。该 VIP 为 VPC1 中终端节点获取的 VIP,本例中为172.16.2.16,VPORT 为 VPC2 中 CLB 的监听端口,本例为1044。
b. 依然使用 telnet 验证连通性,执行 telnet VIP VPORT。
说明:
如果服务器没有安装 telnet,请先执行
yum install telnet 安装 telnet。返回信息如下,表示访问成功: