现象描述
使用 VPN 连接建立 VPC 与 IDC 的通信,VPN 通道显示为已联通状态,但内网无法联通,现象如下:
VPN 通道状态为已联通:

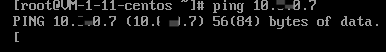
VPC 侧服务器 ping IDC 侧内网 IP,无法 ping 通:
可能原因
通道状态正常但内网却无法联通,可能原因如下:
VPC 子网路由表未添加指向 IDC 侧内网网段的路由
VPC/IDC 侧的安全策略未放通对应源 IP、目的 IP
VPN 网关未添加指向 IDC 侧内网网段的通道(路由型)
VPC/IDC 侧的内网服务器操作系统的防火墙未放行对端网段
VPC/IDC 侧的 SPD 策略未包含该源 IP、目的 IP
VPN 网关未配置路由策略
处理步骤
1. 检查 VPC 子网路由表中,是否有目的地址为 IDC 侧内网网段,下一跳地址为对应 VPN 网关的路由,同时检查 IDC 侧是否有目的地址为 VPC 网段,下一跳地址为对应 VPN 隧道的路由。
进入 VPC 子网路由表,单击路由表 ID,进入详情界面检查:

IDC 侧执行命令检查路由情况(以华为设备为例):
display ip routing-table //查看是否有对应目的地址为云上 VPC 网段,下一跳为对应 VPN 隧道的路由
若是,请执行 步骤3。
若否,请根据业务需求,补全相应路由信息,再执行 步骤2。
2. 检
查通信是否恢复正
常,即登录 VPC/IDC 中的一台服务器,ping 对端服务器内网 IP。说明:
若是,通信正常,问题解决,结束。
若否,请执行 步骤3。
3. 检查 V
PC 中服务器关联的
安全组和子网关联的网络 ACL 是否放通来自云下 IDC 的流量,同时检查 IDC 侧是否放通来自云上 VPC 的流量。
进入 VPC 中服务器安全组 界面,单击安全组 ID,进入“安全组规则”页检查: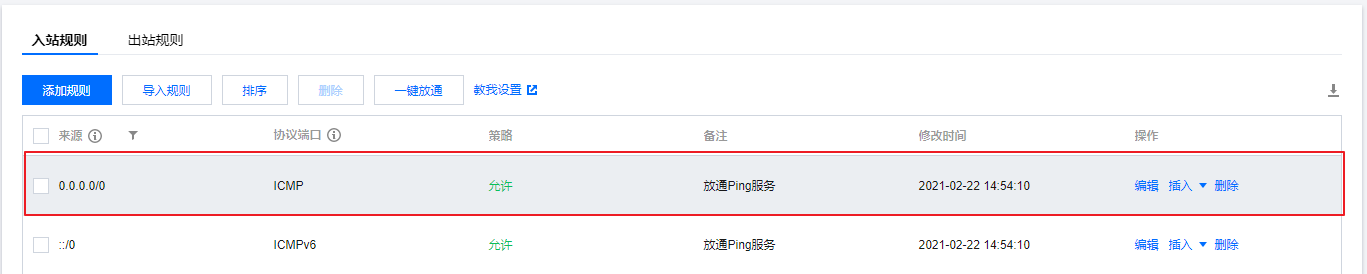
IDC 侧安全策略检查(此处以华为防火墙为例):
display current-configuration configuration security-policy
若是,请执行 步骤5。
若否,请放通安全组/网络 ACL/IDC 侧安全设备需要互通的内网地址段,再执行 步骤4。
4. 检查通
信是否恢复正常
,即登录 VPC/IDC 中的一台服务器,ping 对端服务器内网 IP。若是,通信正常,问题解决,结束。
若否,请执行 步骤5。
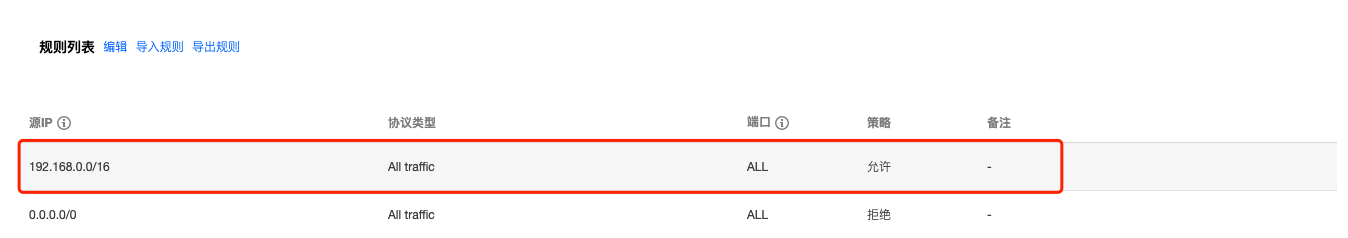
5. 分
别检查 VPC 中云服
务器和 IDC 侧内网服务器操作系统自带防火墙,是否有放通对端网段的策略。
Linux 服务器查看防火墙:iptables --list
Windows 服务器查看防火墙:控制面板/系统和安全/Windows 防火墙/允许的应用若是,请执行 步骤7。
若否,请在内网机器防火墙中放通需要联通的业务网段,再执行 步骤6。
6. 检查
通信是否恢复正常
,即登录 VPC/IDC 中的一台服务器,ping 对端服务器内网 IP。若是,通信正常,问题解决,结束。
若否,请执行 步骤7。
7. 分别检查
VPC 和 IDC 侧的
VPN 通道的感兴趣流(SPD 策略)是否包含需要互通的内网网段。
进入 VPC 侧 SPD 策略,单击 VPN 通道 ID,进入“基本信息”页,即可检查 SPD 策略: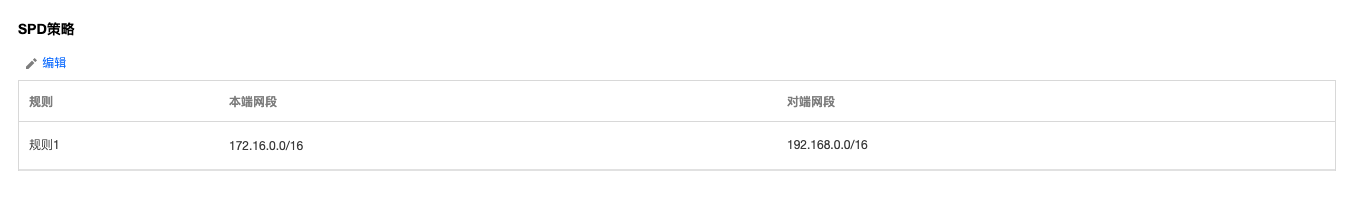
IDC 侧 SPD 策略检查(此处以华为防火墙为例):
display current-configuration configuration acl
若是,请执行 步骤8 。
若否,请补充缺失的 SPD 策略,再执行 步骤8。
8. 检查 VP
N 网关的路由表中
是否包含对应的路由策略。进入 VPN 网关,单击 VPN 网关 ID,进入“路由表”页,即可检查路由策略。
若是,请执行 步骤9。
若否,请在 VPN 网关 > 路由页签指定下一跳,再执行 步骤9。

9. 检查通
信是否恢复正
常,即登录 VPC/IDC 中的一台服务器,ping 对端服务器内网 IP。若是,通信正常,问题解决,结束。
若否,请执行 步骤10。
10. 请收
集以上检查信
息,并 提交工单 或联系设备厂商跟进处理。